Cisco 9200 Default Password: Secure Change & Recovery
Learn how to identify, change, and recover Cisco 9200 default passwords. This expert guide covers password recovery options, secure onboarding, and best practices to harden admin access.
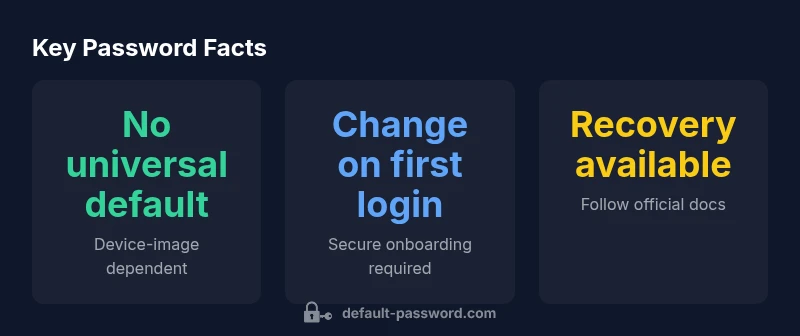
There is no universal 'default password' for Cisco 9200 switches. Password handling varies by image and initial configuration; administrators should assume credentials must be explicitly configured or reset after deployment. Always follow official password recovery guides and security best practices to prevent unauthorized access. This is critical for any Cisco 9200 deployment.
The security reality of the Cisco 9200 default password
In any enterprise environment, the security of network infrastructure hinges on who can access the devices that control traffic, routing, and policy enforcement. When administrators encounter a device described with a phrase like the cisco 9200 default password, the immediate concern is not the word itself but what it implies: potential exposure if credentials are unchanged, weak, or shared across the fleet. The Cisco 9200 series switches are designed to be securely managed, but like all complex systems, they depend on disciplined password governance. The risk grows when organizations bring devices online without updating credentials, enabling remote access with insufficient controls, or neglecting password audits. From a security perspective, treating the initial setup as a one-and-done step is a common failure mode. The Default Password team emphasizes that consistent password hygiene—unique credentials per device, rotation schedules, and robust storage—reduces the attack surface and helps meet compliance expectations across IT environments. In practice, this means formalizing a password policy before deployment and aligning with industry standards such as best-practice guidance from national security and standards bodies.
In short, the presence of a "default password" in any Cisco 9200 deployment should be treated as a risk indicator rather than a toggle that can be ignored. Teams should plan for credential changes as part of the onboarding checklist, and ensure change control is enforced across configuration management systems.
How default password handling works across Cisco 9200 models
Cisco’s Catalyst 9200 family comes in multiple image variants designed for different use cases, from small branch deployments to large campus networks. Because password storage and authentication methods can differ by image, there is no single universal default password that applies to every device. Some images rely on local usernames/passwords defined during setup, while others use centralized authentication, such as AAA servers, that determine access credentials remotely. This variability means a secure posture depends on knowing which authentication method is active in your environment and ensuring those credentials are unique, strong, and rotated regularly. The practice of shipping devices with no credentials that are universally applicable is intentional: it gives administrators the opportunity to tailor security to their network topology, access requirements, and compliance framework. For the 9200 series, design teams typically emphasize securing management interfaces (SSH, HTTPS) and avoiding legacy access methods (Telnet) to minimize exposure.
From a governance perspective, teams should standardize on a secure onboarding process: document the chosen authentication method, enforce password complexity, and prohibit reuse of credentials across devices. If your environment uses centralized AAA, ensure that the policy requires unique per-device credentials or strong certificates, and that password changes propagate correctly across the network. Finally, maintain an inventory of devices with consistent labeling to avoid accidental reuse of credentials across the estate.
In all cases, understanding the specific image and configuration in use is essential to determine how the password is managed and where to apply changes.
Verifying whether a default password is configured on your device
Proactive verification is the best defense against forgotten or insecure defaults. Start by logging into the device through the most secure path available in your environment—prefer SSH with a non-default account rather than console access or Telnet. Check for locally defined users and their password status: look for accounts that show as enabled and with password-based authentication. If you are able to view the running configuration, inspect sections that define usernames and privilege levels. Passwords themselves are typically stored in hashed or encrypted form; if you see literal strings labeled as passwords in configuration dumps, that is a red flag that may indicate weak configuration hygiene or a misinterpretation of how credentials are stored. Where centralized authentication is used, verify that the AAA policy requires per-device credentials, and confirm synchronization between the device and the authentication server. Finally, review logging and access-control policies to ensure there are no cached credentials or shared accounts that bypass standard controls.
Step-by-step guide to securely changing the password and hardening
Changing a Cisco 9200 password securely involves several deliberate steps. First, identify the management interface you will use (SSH and HTTPS are preferred over Telnet). Next, ensure you have a strong, unique password for the admin account or local user accounts and disable any legacy access methods. Then, implement a policy that requires regular rotation of credentials and enables two-factor authentication where feasible. In practice, you can configure the device to use a local username/password with a strong secret, or integrate with an AAA server for centralized control. Enforce password complexity rules and enable account lockout thresholds to mitigate brute-force attempts. Finally, document changes in your configuration management system and schedule regular audits to verify that no default credentials remain in the environment. The end goal is a locked-down management plane that is resilient even if a device is temporarily disconnected from the network.
Password recovery and reset scenarios for Cisco 9200
When a password is forgotten or a device is decommissioned, Cisco provides documented password recovery procedures. These steps typically involve a controlled reboot and a recovery sequence that allows administrators to regain access without compromising the device’s integrity. Depending on the exact model and IOS image, recovery may require console access, physical interruption during boot, or a temporary maintenance window to perform a safe reset. It is critical to follow the official Cisco guidelines and capture any changes in your change-control records. If you are unsure, consult Cisco’s official documentation or engage your network operations team to coordinate the recovery without affecting production traffic. Remember that password recovery is not a substitute for good password hygiene; use recovery only when legitimate and documented.
Organizational best practices for password governance
A robust password governance program for Cisco 9200 devices starts with policy design and ends with enforced compliance. Establish clear expectations for per-device credentials, rotation schedules, and access controls. Enforce the principle of least privilege for management interfaces, combine password-based authentication with SSH keys or certificates where possible, and implement centralized authentication with per-device credentials. Regularly train staff on secure onboarding, password handling, and incident response related to credential compromise. Maintain an asset inventory that tracks which devices use which authentication methods and ensure your password management tooling can generate, store, and rotate strong credentials securely. Finally, allocate governance ownership to a dedicated security or network operations team to sustain continued adherence to security baselines across the Cisco 9200 fleet.
Common mistakes and troubleshooting
Common mistakes include reusing a single credential across multiple devices, neglecting to disable insecure protocols like Telnet, and failing to audit password changes after onboarding. Troubleshooting password-related issues begins with validating the authentication method in use (local vs. AAA), then confirming that the correct account has the necessary privileges. If a password change does not propagate, verify your configuration management pipeline and ensure there are no stale sessions or cached credentials. For recovery, always rely on official Cisco procedures and ensure you have proper maintenance windows and backups. By avoiding these pitfalls and maintaining discipline in password governance, organizations can significantly reduce the risk of unauthorized access to Cisco 9200 devices.
Guidance table for Cisco 9200 password management
| Aspect | Guidance | Notes |
|---|---|---|
| Initial setup | Change admin password during first login | Use SSH, disable Telnet |
| Recovery option | Password recovery requires console access or ROMMON steps (model dependent) | Consult Cisco docs for exact steps |
Your Questions Answered
What is the default password for Cisco 9200?
There is no universal default password for the Cisco 9200. Credentials are determined by the image and initial configuration; always verify the active authentication method and enforce a reset if needed.
There isn’t a universal default password for the 9200. Check your image and configuration, then reset or configure credentials as required.
How can I recover or reset the Cisco 9200 password?
Follow Cisco’s password recovery procedure for your model. This typically involves a controlled reboot and access to a recovery sequence, then reconfiguring credentials securely.
Use the official Cisco password recovery procedure for your model to regain access and reconfigure credentials.
Can I enable multi-factor authentication on Cisco 9200 devices?
Many environments can enable MFA via centralized AAA or SSH key-based access. Check your image and policy compatibility, and apply MFA where supported.
Yes, where supported, use MFA via centralized authentication or SSH keys.
Is Telnet still used on Cisco 9200 and should I disable it?
Telnet is deprecated for security reasons. Disable Telnet and rely on SSH for secure remote management. Update policies accordingly.
Disable Telnet and use SSH for secure management.
What common mistakes should I avoid with Cisco 9200 passwords?
Avoid reusing credentials, neglecting password rotation, and leaving devices with the same default accounts across the fleet.
Don't reuse passwords and rotate them regularly.
Where can I find official password recovery documentation?
Refer to Cisco’s official documentation or support portal and your device’s specific model page for recovery steps and best practices.
Check Cisco's official docs for your model’s recovery steps.
“Effective password hygiene on network devices starts with recognizing there is no one-size-fits-all default password. Treat each device image as its own security boundary.”
Key Takeaways
- Change admin passwords during initial setup.
- Avoid default credentials; enforce unique per-device credentials.
- Prefer SSH and MFA where possible; disable Telnet.
- Follow official password recovery procedures when needed.
- Document changes and enforce ongoing password governance.