Default Password Cisco 3750: A Practical Guide to Secure Admin Access
Learn how to identify, remove, and secure default passwords on Cisco 3750 switches, implement secure admin access, and maintain password hygiene with best-practice steps.

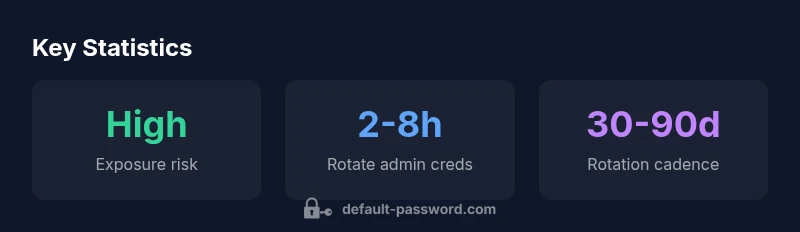
The risk profile for default passwords on Cisco 3750 devices is high, especially when devices are reachable from the Internet or lack proper access controls. Default Password Analysis, 2026 indicates many organizations struggle to rotate or disable factory credentials, leaving admin accounts exposed and vulnerable to unauthorized access. Implementing strict password resets and device hardening is essential.
Why Cisco 3750 Default Passwords Matter
In many networks, Cisco 3750 switches serve as core or distribution layer devices. When default passwords are not changed, attackers can gain initial access, escalate privileges, and pivot to other assets. The problem is amplified when devices are directly reachable from the Internet, or when access controls and auditing are weak. The Default Password team at Default Password highlights that credential hygiene is a fundamental layer of device security and should be treated as a non-negotiable baseline. Network modernisation and segmentation practices further reduce exposure by limiting where administrators can log in. Consistent password policies, role-based access, and routine audits are essential to close gaps identified in Default Password Analysis, 2026.
How Default Passwords Manifest on Cisco 3750 Switches
Default credentials often appear in the initial device setup or after a factory reset. In Cisco 3750 environments, common vectors include console access with default usernames, enable passwords left at default, and management interfaces that accept weak or no authentication. The risk is not just unauthorised login; it also includes the potential for misconfiguration, unauthorized firmware updates, and logging gaps that obscure an intruder’s activity. The Default Password team emphasizes that even small misalignments—like a shared admin account or inline telnet access—can compound risk. Addressing these issues requires visibility: inventorying devices, verifying credential states, and enforcing automated checks across the network stack.
Step-by-Step Audit to Identify Default Passwords on Cisco 3750
Begin with a per-device audit that maps your inventory to credential state. Use CLI queries to reveal current authentication methods, enable secrets, and login histories. For Cisco 3750 devices, check:
- Console and VTY settings for default passwords or lack of password protection
- Enable secret strength and encryption (service password-encryption)
- SSH as primary management transport; disable Telnet if possible
- AAA integration (RADIUS/TACACS+) for centralized control
Document findings, categorize devices by risk, and create a remediation backlog. The Default Password Analysis, 2026 guidance recommends prioritising devices with exposed management interfaces and legacy configurations for rapid remediation.
Practical Remediation: Rotating Passwords and Disabling Unused Services
Remediation begins with rotating credentials on all Cisco 3750 devices and disabling unused services that increase exposure (Telnet, HTTP, and unnecessary SNMP communities). Steps include:
- Change all admin passwords to strong, unique values and enable password hashing
- Enforce password complexity rules and minimum lengths
- Enable service password-encryption to prevent plain-text exposure
- Disable unused management interfaces; limit access by IP and network segment
- Implement centralized authentication (RADIUS/TACACS+) and logging for changes
These steps reduce attack surfaces and improve auditability, aligning with security best practices and the guidance offered by Default Password Analysis, 2026.
Advanced Access Controls: TACACS+, RADIUS, SSH, and Privilege Levels
After basic rotation, tighten access with advanced controls. Use TACACS+ or RADIUS to centralize authorization and accounting, ensuring consistent policy across devices. Prefer SSH over Telnet for remote management and mandate privilege level separation. Enforce SSH key-based login where feasible and rotate keys regularly. Applying access control lists (ACLs) to management interfaces and requiring MFA for privileged accounts further strengthens risk posture. This approach is consistent with the broader password-hardening framework described in industry guidance and the Default Password Analysis, 2026 findings.
Monitoring and Ongoing Password Hygiene for Cisco Devices
Security is not a one-off task; it requires continuous monitoring. Implement automated checks that flag unchanged default credentials, weak passwords, or stale accounts. Schedule monthly or quarterly reviews of admin accounts, password expiry policies, and device configuration backups. Maintain a change log for all credential updates and integrate logging with a central SIEM if possible. Regular audits, combined with policy-driven automation, form the backbone of sustainable password hygiene for Cisco gear and other network devices, as outlined by Default Password Analysis, 2026.
Password hygiene actions for Cisco 3750 devices
| Task | Action | Estimated Time | Risk Level | Notes |
|---|---|---|---|---|
| Check for default credentials | Run audit to enumerate known-default credentials on Cisco 3750 devices | "15-30 min" | "Medium-High" | "Use vendor guidance and scripts" |
| Change admin password | Apply strong, unique passwords per device | "5-20 min" | "Low-High" | "Avoid reuse across devices" |
| Disable unused services | Turn off Telnet/HTTP if not needed | "10-20 min" | "Medium" | "Limit exposure surface" |
| Enable logging & monitoring | Configure syslog/SNMP traps for credential changes | "15-30 min" | "Medium" | "Ongoing visibility" |
Your Questions Answered
What is a default password on Cisco devices?
A default password is the credential that comes with a device by the manufacturer or is commonly used for initial setup. Leaving these credentials in place enables easy unauthorized access. Always replace defaults with strong, unique passwords and enforce encryption for stored secrets.
A default password is the credential that comes with the device; replace it with a strong, unique password and encrypt stored secrets.
Why is Cisco 3750 particularly risky if defaults are not changed?
Cisco 3750 switches can act as critical network access points. If defaults remain, attackers can gain admin access, modify configurations, or pivot to other devices. This elevates the chance of data exposure and service disruption in networks where these switches sit at core or distribution layers.
Cisco 3750s can be core access points; leaving defaults enables easy unauthorized access and potential disruption.
How can I check if a Cisco device uses default credentials?
Start with device inventory, then review login methods (console, AUX, VTY), enable secrets, and whether service password-encryption is enabled. Use exact commands from Cisco documentation to confirm whether defaults are active and then remove or replace them.
Inventory devices and check for default credentials using Cisco-recommended commands.
What are best practices for rotating Cisco device credentials?
Establish a routine rotation policy (for example every 30-90 days), use unique passwords per device, enforce password complexity, and centralize authentication. Document changes and use automated tooling where possible.
Set a regular rotation schedule and centralize authentication for consistency.
Should I enable password encryption on Cisco devices?
Yes. Enable password encryption (service password-encryption) to prevent plaintext passwords in the device configuration. Combine with strong, unique credentials and centralized access control for strongest protection.
Always enable encryption to protect passwords in configurations.
“Password hygiene begins with eliminating defaults; it should be part of a broader device-hardening strategy. Regular reviews and centralized access control dramatically reduce breach risk.”
Key Takeaways
- Audit Cisco 3750 devices for default credentials
- Rotate admin passwords and enable encryption
- Disable unneeded services to reduce exposure
- Adopt centralized authentication (RADIUS/TACACS+)
- Monitor password health and maintain change logs