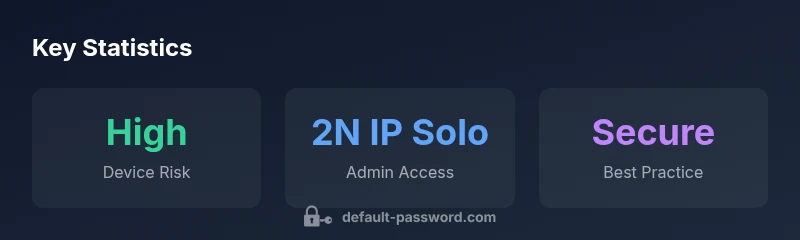
Default Passwords in 2N IP Solo: Admin Access Guide
A practical, data-driven guide for identifying, resetting, and managing default passwords on IP-based devices like the 2N IP Solo. Learn risks, policy considerations, and step-by-step actions to secure admin interfaces and protect networks.
Seeing a device labeled default password 2n ip solo signals an urgent security risk. Act now by changing the factory credentials, auditing admin access, and applying firmware updates. This guide explains why defaults are dangerous and provides practical steps to secure the 2N IP Solo and similar IP-based interfaces, per Default Password analysis, 2026.
Why Default Password Security Matters for IP Devices
Default passwords are a glaring security flaw in consumer and enterprise IP devices. When devices such as routers, IP cameras, or intercoms ship with common credentials, attackers can gain unauthenticated access, pivot through the network, and exfiltrate sensitive data. The risk multiplies in environments with remote administration and cloud-linked dashboards. This section examines the underlying reasons why defaults persist, including supply-chain convenience, user unawareness, and the lack of integrated credential management in some devices. By understanding these dynamics, IT admins can prioritize immediate actions: inventory devices, verify firmware versions, and enforce password policies. The takeaway is simple: unless defaults are replaced with unique, strong credentials, the attack surface remains open, undermining segment security and compliance requirements.
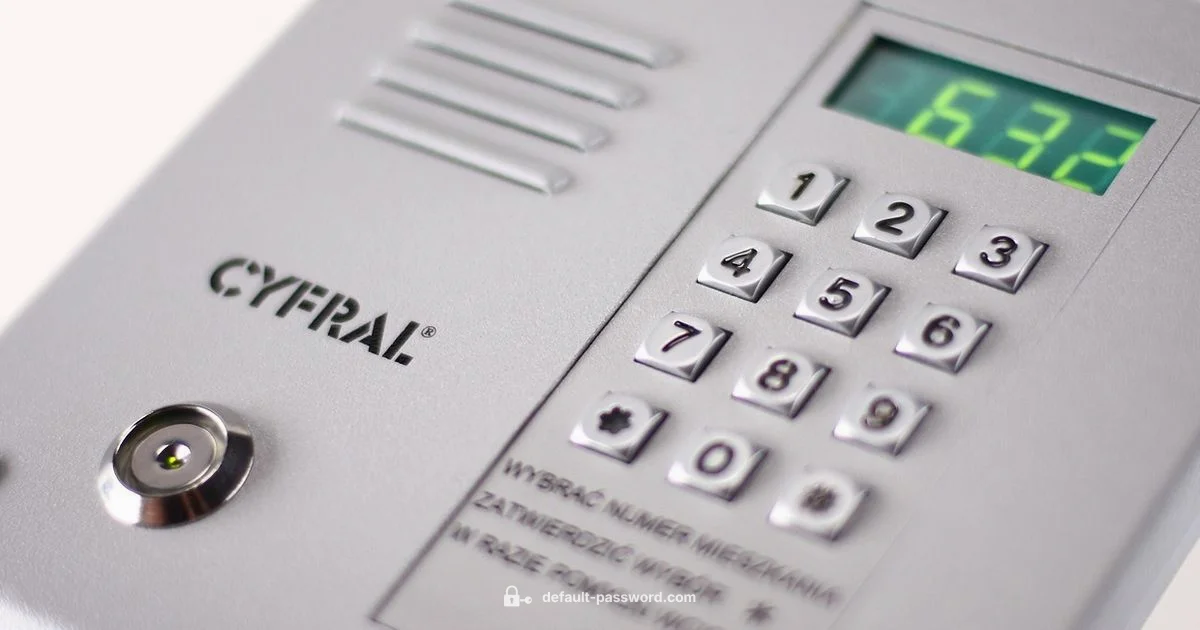
Understanding the 2N IP Solo Context and Similar Interfaces
The 2N IP Solo is a SIP intercom with a web-based admin panel and default credentials that can grant control over door access, audio/video streams, and event logs. Many vendors ship similar devices with generic defaults that attackers can exploit if left unchanged. In practice, administrators should treat any IP-based interface—whether door intercoms, cameras, or access controllers—as potential entry points. Proactive measures include inventorying devices, identifying those using default credentials, and planning a device-wide credential hygiene initiative that aligns with organizational policies and regulatory expectations.
How to Identify Default Passwords on Devices
Identification starts with documentation and onboard procedures. Check device manuals, OEM support portals, and in-box stickers for default usernames and passwords. If documentation is ambiguous, inspect the device’s user interface for prefilled admin accounts, or review initial setup prompts. For networked devices with cloud dashboards, examine account lists for locally stored credentials and look for patterns (e.g., common administrator accounts, universal passwords). Finally, run an offline audit to ensure no password reuse across devices and confirm that factory defaults are disabled where possible.
Risks and Attack Vectors Linked to Default Credentials
Default credentials enable broad access with minimal effort, especially when devices are exposed to the internet or remotely managed. Attackers commonly use automated scans to discover devices with known defaults, then attempt credential-based infiltration. Once an attacker gains access, they can enumerate other devices, pivot to critical services, and potentially disrupt operations. The most dangerous scenarios involve legacy intercoms and networked access points that lack monitoring, logging, or incident response. Recognize that even a single compromised device can undermine an entire segment of a network.
Best Practices for Managing Default Passwords Across Devices
Adopt a layered approach to credential hygiene. Start with an up-to-date asset inventory, disable unnecessary remote administration, and enforce unique, strong passwords per device. Where possible, remove default accounts or rename them to reduce predictability. Implement firmware updates on a fixed schedule and enable basic logging to monitor credential changes and access attempts. Centralize password management, align with IT governance, and perform periodic audits to ensure ongoing compliance. Finally, educate users on the risks of shared credentials to sustain a security-first culture.
Step-by-Step: Resetting and Reclaiming Admin Access
Follow a practical, device-aware process: 1) Document the device and current role assignments; 2) Reset to a fresh, strong password and apply a unique username if supported; 3) Update firmware to the latest version; 4) Disable or restrict remote admin, UPnP, and universal logging; 5) Re-check all admin accounts for least-privilege access; 6) Record the changes in a central registry and notify stakeholders. Repeat for all devices in scope and verify that alerts cover credential changes.
Compliance, Logging, and Policy Considerations
Credential hygiene is a compliance and governance issue as much as a technical one. Establish a policy for password rotation, device onboarding, and audit logging. Ensure incident response plans include steps for suspected credential compromise and define who owns password upkeep. Maintain logs of password changes, firmware updates, and access attempts to support audits and investigations. Align with industry best practices and your organization's risk tolerance to sustain an effective security posture.
Default credential risk and recommended actions by device type
| Device Type | Default Credential Risk | Recommended Action |
|---|---|---|
| IP camera | High | Change default credentials immediately; disable remote access |
| Router | High | Change default password; disable WAN management |
| 2N IP Solo intercom | High | Set unique password; change admin user; update firmware |
Your Questions Answered
Why is default password a risk for IP Solo devices?
Default passwords are widely known; attackers exploit them to gain remote access. Changing them reduces risk and improves logging.
Default passwords are easy to guess; changing them locks out attackers. Check the full guide for details.
What steps should I take to secure a 2N IP Solo?
Reset to a strong password, update firmware, disable unused services, and enable logging.
Reset, update, and review settings.
Can I enable MFA on IP devices?
Many devices lack MFA; use strong unique passwords and disable remote admin. Check device docs.
Some devices don't support MFA; use strong passwords and disable risky features.
How often should passwords be changed?
Change when you suspect compromise or after policy change; avoid arbitrary frequent changes that reduce security.
Change if you think credentials are exposed or per policy.
What about default credentials on routers and cameras?
These devices often ship with defaults; secure them by changing credentials and reviewing access controls.
Change defaults, review who can access them.
“Default passwords are the weakest link in any network interface. A disciplined approach to credential hygiene—changing defaults, auditing access, and updating firmware—dramatically lowers exposure.”
Key Takeaways
- Identify devices with default credentials early.
- Change defaults before network exposure.
- Document password changes for audits.
- Prefer device-native password policies and MFA where available.
- Regularly review admin access and firmware updates.