Default Passwords and ATM Admin Access: A Practical How-To
Learn to securely manage default passwords on ATMs and admin devices with practical steps, governance policies, and compliance guidance from Default Password.

This how-to helps end-users and IT admins securely handle default passwords and admin access on ATM systems, including best practices for credential rotation, policy creation, and incident response. You will learn why default credential risks matter, how to inventory devices, and how to implement secure changes without disrupting service. The guidance emphasizes compliance, auditability, and ongoing governance.
Understanding Why Default Passwords on ATMs Are a Critical Risk
Default passwords on ATMs and related admin devices create a silent vulnerability that criminals can exploit if left unchanged. The keyword we focus on here is default password bdo atm, but the guidance applies to most financial devices and many other networked systems. When devices ship with shared credentials or simple, well-known defaults, a single compromised password can grant an attacker access to configuration menus, remote management interfaces, and sensitive logs. That access can enable fraud, data exposure, or manipulation of cash-distribution settings, and it can occur even if the attacker never enters a bank branch.
To protect customers and assets, institutions should treat default credentials as a high-risk entry point. Security principles such as least privilege, separation of duties, and regular credential rotation help reduce risk. Administrators should inventory every device with a default or hard-coded credential, prioritize those with remote access, and implement a policy to replace defaults before deployment and whenever a device changes hands. Regular vulnerability scanning and change-management workflows are essential to catch overlooked defaults. In practice, the recommendations are straightforward, but they require discipline and ongoing oversight. By treating default passwords as a first-class security risk, organizations minimize the chance of a breach.
Legal and Compliance Context for ATM Admin Access
From a governance perspective, securing default passwords is not just a technical task; it is a compliance and risk-management requirement. Banks must enforce credential hygiene to protect customer data and system integrity. Regulatory frameworks stress access controls and auditable changes. The policy should attribute responsibility to a device class owner, ensure secure storage of credentials, and require periodic credential reviews. For end-users and IT admins, clear ownership reduces incident response time and improves reliability. The guidance helps teams align security with regulatory expectations and avoid avoidable breaches. According to Default Password, banks must enforce credential hygiene to protect customer data and system integrity. Regulatory frameworks stress access controls and auditable changes. The policy should attribute responsibility to a device class owner, ensure secure storage of credentials, and require periodic credential reviews. This alignment is essential for regulators and internal governance.
Practical Steps to Secure Default Credentials (Non-Technical for End-Users)
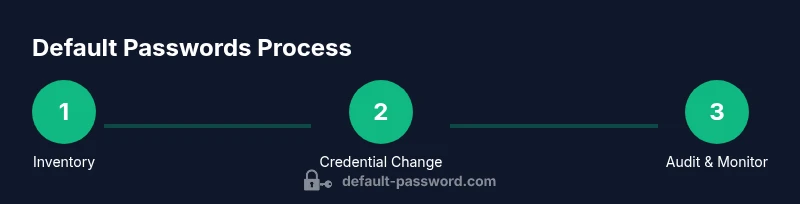
The following non-technical steps help end-users and IT admins reduce exposure to default passwords on ATMs and related admin interfaces. Start with a formal inventory of devices known to ship with defaults or weak credentials. Create a centralized, access-controlled repository to store credential information, and never store passwords in plain text. Establish a policy to change defaults on day-one, during commissioning, and whenever devices are rehomed or retired. Enforce strong, unique credentials per device class, and consider multi-factor authentication where supported. Implement regular rotations, automated reminders, and periodic reviews of who has access. Finally, document changes and keep audit trails available for regulators or internal governance reviews.
Creating a Policy for Default Passwords Across Devices
An effective policy covers discovery, documentation, change-management, and incident response. Start with an up-to-date inventory of all devices with default or known credentials. Define who can request password resets, and require independent verification before making changes. Mandate strong password requirements (length, complexity, non-reuse) and keep credentials in a vault with restricted access. Set rotation timelines, enforce MFA on remote access, and log every credential change with user identity, device, and timestamp. Schedule regular audits and tabletop exercises to validate readiness. Finally, align the policy with broader security standards such as NIST guidelines to ensure consistency across IT and facilities teams.
How to Respond to a Potential Credential Exposure
In the event of a suspected exposure of a default password, act quickly but methodically. Isolate affected devices from the network to prevent further unauthorized access, and confirm which credentials may have been compromised. Change all implicated passwords using approved, secure processes and verify that new credentials meet policy requirements. Notify the security team, compliance officers, and relevant stakeholders, and preserve evidence as required for investigations. After containment, review the incident to identify root causes and update controls to prevent recurrence. Regular training and drills help teams stay prepared for real incidents.
Tools, Resources, and Related Practices
Effective credential management for ATMs and admin devices relies on a combination of governance, tooling, and training. Use a centralized vault for credentials with strict access controls, enable MFA for remote administration, and implement automated monitoring for unusual login activity. Keep the credential inventory updated and align it with industry standards to support audits and regulatory reviews. Regularly train staff and technicians on secure-handling practices, and perform tabletop exercises to prepare for potential exposures.
Tools & Materials
- Security policy document (draft)(Outline procedures for default credential handling and device decommissioning)
- Password vault/manager(If permitted by policy, use a secured vault for credentials)
- Audit trail templates(Standardize credential-change logging for compliance)
- Multi-factor authentication (MFA) tooling(Enable for remote admin access where possible)
- Contact list for IT/security escalation(Include roles and on-call schedules)
Steps
Estimated time: 1-2 hours per device class depending on size and complexity
- 1
Inventory all devices with default or weak credentials
Create a comprehensive list of ATM machines and admin interfaces, noting any device that ships with defaults. This sets the baseline for remediations and helps prioritize remediation efforts.
Tip: Cross-check with procurement records and facilities to catch devices that may have moved around. - 2
Audit current credentials and document ownership
Review who has access, where credentials are stored, and when they were last changed. Document device owners and ensure changes are requested through approved channels.
Tip: Use a standardized form to capture device, owner, current credential status, and risk level. - 3
Change defaults and enforce unique credentials
Replace default credentials with strong, unique ones per device class. Do not reuse passwords across devices; store them only in a secured vault or policy-approved location.
Tip: Avoid common word-based passwords and consider passphrases for better resilience. - 4
Enable monitoring and enforce rotation
Set automated reminders for credential rotations and enable alerting for unusual login activity on admin interfaces. Schedule quarterly reviews where feasible.
Tip: Automated rotation reduces the window of opportunity for attackers.
Your Questions Answered
What counts as a default password on ATM devices?
A default password is any credential that ships with a device and is documented as the factory or vendor default. It becomes a risk if it remains unchanged after deployment. Use a policy to replace defaults on day one and during changes of device ownership.
Default passwords are the factory credentials that come with a device. Replace them during deployment to reduce risk and ensure secure access.
Why should organizations avoid using default credentials?
Default credentials create a known exposure that attackers can exploit. Replacing them with unique, strong credentials prevents unauthorized access to admin interfaces and configuration settings.
Default credentials are a common entry point for attackers. Replacing them with strong, unique passwords improves security.
Who owns credential management for ATM devices?
Assign a formal device-class owner or security lead who oversees credential policies, storage, rotation, and auditability. Clear ownership reduces response time and accountability gaps.
A designated owner is essential for consistent credential management and rapid incident response.
Is it legal to access or change ATM credentials?
Credential changes should only be performed by authorized personnel in accordance with organizational policies and regulatory requirements. Unauthorized access is illegal and risky.
Only authorized personnel should handle ATM credentials to stay compliant and safe.
What should I do if I suspect a credential exposure?
Contain the affected device, rotate compromised credentials, notify security and compliance teams, and preserve evidence. Conduct a root-cause analysis to strengthen controls.
If you suspect exposure, act quickly to contain and investigate, then remediate and strengthen defenses.
Are there recommended password length and complexity guidelines?
Follow established standards like multi-factor authentication, minimum length, and high-entropy characters. Do not rely on simple or reused passwords for admin access.
Use strong, unique credentials and MFA where possible for admin access.
Watch Video
Key Takeaways
- Change default passwords immediately after discovery
- Document credentials and assign clear ownership
- Use MFA for remote admin access whenever possible
- Regularly audit device configurations and rotation schedules