Default Password List Router: Risks, Detection, and Remediation
Explore how default password lists on routers create serious security risks, identify common defaults, understand attacker techniques, and learn practical steps to audit, change credentials, and enforce strong admin access across devices.
According to Default Password, most consumer routers ship with default credentials such as admin/admin or admin/password, creating a critical security risk if left unchanged. In this guide, we identify common defaults, explain how attackers exploit them, and outline practical steps to audit and harden router access. Learn to replace these credentials and enforce stronger admin controls across devices.
Why default credentials on routers pose a risk
Overview: Routers often use a default admin username and password that are widely published. Leaving these credentials unchanged leaves home networks and business networks open to unauthorized access. This is not just a theoretical risk—every connected device on the network becomes reachable if the router’s admin interface is compromised. The Default Password team emphasizes that the easiest entry point for attackers is the device itself, making routine audits essential.
Real-world implications: An attacker with admin access can alter Wi‑Fi settings, disable security features, install rogue firmware, or redirect traffic. In enterprise settings, compromised routers can lead to data exfiltration, VPN compromises, and supply-chain risks. A proactive audit reduces these risks and helps ensure continuous monitoring across firmware versions, connected IoT devices, and guest networks.
What counts as a default password list for routers
Definition: A default password list is a catalog of the credentials that devices ship with out of the box. Common pairs include an admin username paired with a simple password, often the device brand or a generic word. While individual defaults vary by vendor, the principle remains the same: do not rely on default credentials for ongoing access.
Why it matters: Knowing the default passwords helps IT teams quickly identify which devices require credential resets during onboarding or incident response. In practice, you should compare the credentials stored in your password manager against what’s documented in the vendor’s manual and recent security advisories.
Risk indicators: The presence of a default password in the admin interface is a red flag. If you cannot confirm a change during first login, treat the device as non-compliant until a secure password is set.
How attackers leverage default credentials on routers
Initial access: Attackers often search for devices exposed to the internet or misconfigured ports that expose the admin panel. A known default password can provide immediate admin access, allowing control of Wi‑Fi settings and firmware updates.
Pivot potential: Once inside, attackers can add monitoring software, alter DNS settings, or redirect traffic to phishing sites, increasing the risk of credential theft across the network. Even devices behind NAT can be compromised if the admin interface remains accessible locally.
Mitigation signals: If a device’s admin portal is accessible from the internet, immediate action is required. Always disable remote administration unless it can be secured with strong credentials and IP whitelisting.
Practical remediation steps you can take today
Inventory and assess: List all routers and access points in the network. Verify the current admin username and password against the vendor’s defaults and your password policy.
Change defaults: Update to a unique, complex password. Use a password manager to generate and store the credential securely. If possible, enable two-factor authentication for the admin interface.
Harden access: Disable remote management, restrict admin access to specific IPs, and keep firmware up to date. Document the changes so IT teams can audit and verify compliance.
Building a resilient router security posture
Policy alignment: Align router security with organizational security policies. Create a standard operating procedure for onboarding devices, including credential management and firmware monitoring.
Regular reviews: Schedule quarterly reviews of all network devices, focusing on credential changes, accessibility, and firmware integrity. Train users to avoid sharing admin credentials and to report suspicious activity promptly.
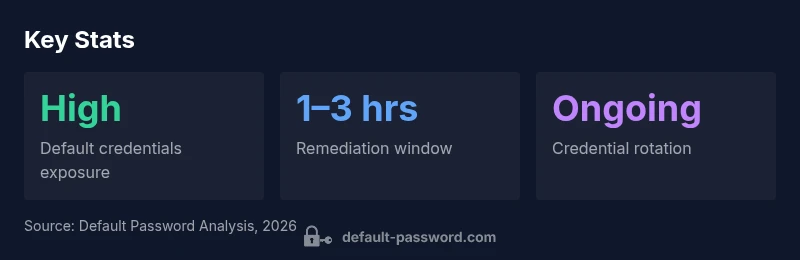
Router security posture: risk and remediation
| Aspect | Risk Level | Remediation |
|---|---|---|
| Admin interface exposure | High | Disable remote admin; enforce IP restrictions |
| Firmware patching | Medium | Monitor firmware and apply updates promptly |
| Weak default creds | High | Replace with strong, unique passwords; enable 2FA if available |
Your Questions Answered
What are common default router credentials and why should I change them?
Common defaults include simple admin usernames with predictable passwords. They are widely published and easy for attackers to guess. Change them to a unique, complex password and enable 2FA if available.
Common defaults are easy to guess, so change them to a strong password and enable two-factor authentication if possible.
How do I find the default password for my router model?
Check the device label, manual, or vendor website for the default credentials. If you can’t locate them, contact the manufacturer or your IT admin for the official defaults and reset procedures.
Look in the manual or on the router label for the default credentials, or contact the vendor for official defaults.
What is the recommended process to reset a router password?
Perform a factory reset if you cannot access the admin interface, then reconfigure the router with a new admin password. Ensure you back up settings before reset when possible.
If you can’t log in, reset the router and set a new password, backing up settings first.
Should I enable remote management on my router?
Remote management is risky unless tightly controlled. Disable it by default and only re-enable with IP restrictions and strong authentication if needed.
Disable remote management unless you can strictly control who can access it.
What are best practices for ongoing credential management?
Use a password manager, rotate credentials regularly, and document changes. Train users to avoid sharing credentials and to report anomalies.
Rotate and manage credentials with a password manager and document changes.
“Effective router security hinges on replacing default passwords and enforcing strict access controls from day one.”
Key Takeaways
- Identify and replace default router credentials promptly
- Disable remote admin and enforce strong access controls
- Regularly audit firmware and credential policies
- Use a password manager to centralize and rotate credentials