Resetting and Securing the USG 3P Default Password
Learn how to reset the USG 3P default password, secure admin access, and maintain ongoing password hygiene with practical, step-by-step guidance from Default Password.

This guide shows you how to locate and reset the default password on USG 3P devices, secure admin access, and implement ongoing password hygiene. You’ll follow a clear, step-by-step process designed for IT admins and informed end users. It emphasizes safe reset methods, role-based access, and proper documentation.
Understanding the risk of default passwords on network devices
Default passwords on network gear like USG 3P represent a critical security risk. Leaving credentials unchanged provides an easy entry point for attackers, potentially compromising VPN access, firewall rules, and administrative control. The Default Password team emphasizes that changing defaults is the first line of defense. In this article, we explore why default credentials linger, how attackers exploit them, and practical methods to mitigate those risks through disciplined password hygiene and device hardening.
- Attackers commonly gain initial footholds when admin credentials are left unchanged after deployment.
- Pairing password changes with firmware updates reduces exposure to known vulnerabilities.
- Disabling unused management interfaces minimizes the attack surface.
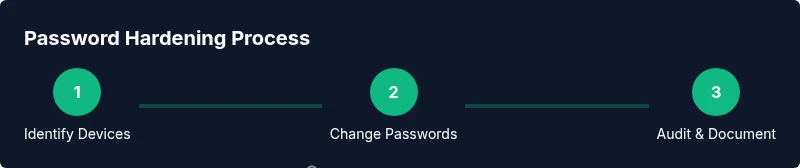
To begin, perform a quick audit of your environment to identify devices that still use factory-default or weak credentials. The process benefits from a central asset inventory, standardized naming, and a policy that requires password changes during onboarding and periodic reviews. This approach aligns with security best practices and helps IT teams enforce consistent controls across diverse vendors and models.
According to Default Password, changing default credentials on network devices like USG 3P is essential for reducing risk across corporate networks.
Quick overview: USG 3P authentication architecture
USG 3P devices expose multiple authentication surfaces to manage and secure. The primary admin interface is the web UI, typically secured with HTTPS, while SSH may be available for advanced users. API access and service accounts can exist for automation or integration tasks. A strong security posture relies on restricting admin interfaces to trusted networks, disabling unused methods, and segregating administrative accounts from regular user access. This section explains how these layers interact and why protecting every surface matters for overall device security. By understanding the authentication architecture, you can design a resilient hardening plan and avoid common misconfigurations that leave doors unlocked for attackers. The goal is to minimize exposure while keeping legitimate administration efficient.
Planning and prerequisites before changing default credentials
Before making changes, establish a controlled plan. Inventory every USG 3P or similar device in your network and note current credential states. Verify you have a working backup of the device configuration and a recovery path if something goes wrong. Ensure you have access to the device documentation and the latest firmware—firmware updates often include security improvements that complement password changes. Prepare a dedicated maintenance window if possible, and notify affected users. Create a formal change record to document the new credentials, the person responsible, and the date of the change. Finally, confirm that you have a secure channel to communicate the new credentials and that password storage follows your organization’s policy (prefer a password manager with MFA).
This planning phase helps prevent missteps and ensures you have a rollback option if the change impacts legitimate access.
Step-by-step manual password reset and secure configuration
Resetting a default password should be a deliberate, auditable process. Start by exporting a backup of the current configuration so you can restore if needed. Then access the device’s admin interface via a secure method (prefer HTTPS or SSH over telnet возможностей). Change the default password to a long, unique passphrase generated by a password manager. After updating, review other security settings: disable unnecessary services, limit admin access to trusted IPs, and enable automatic logout after inactivity. Finally, test all admin access paths (web UI and CLI) from trusted networks and update your password registry.
This section emphasizes keeping a detailed audit trail and confirming successful login with the new credentials. If two-factor authentication is supported, enable it for an additional layer of security. Remember to document the changes in your asset log and update any automated scripts to use the new password if needed.
Verification and documentation after changes
Verification is about ensuring the change sticks and does not break legitimate access. After saving the new credentials, attempt to log in from a management station on a trusted network. Check device logs for any failed login attempts or unusual activity and set up alerts if possible. Update the central inventory with device name, location, firmware version, and the new password management entry. Store the new credentials in a secure password manager and review backup configurations to guarantee you can recover configurations if a device loses power or reboots. Finally, communicate the completion of the change to stakeholders and schedule a follow-up audit to verify ongoing compliance.
Ongoing best practices for USG 3P and similar devices
To maintain a robust security baseline, adopt a regular password hygiene routine. Enforce strong password policies, rotate passwords on a scheduled cadence, and disable unused services. Favor centralized credential management and consider enabling MFA where supported. Maintain an up-to-date asset inventory and conduct quarterly reviews to identify devices that still rely on defaults. Ensure that admin interfaces are only accessible from trusted networks and that all devices in the fleet receive timely firmware updates. Documentation should accompany every change, and backups should be routinely tested to verify recoverability.
Authority sources
- https://www.cisa.gov/ known-best-practices-for-default-passwords
- https://pages.nist.gov/800-63-3/sp800-63b.html
- https://www.nist.gov/topics/cybersecurity-framework
Tools & Materials
- USG 3P device manual(Have the manual on hand for model-specific steps)
- Computer or mobile device with admin access(Browser or SSH client; ensure secure network access)
- Backup power supply (UPS)(Prevents power loss during config changes)
- Strong, unique password(Generated via a password manager; avoid reuse)
- Current configuration backup/export(Pre-change snapshot in case rollback is needed)
- Asset inventory document(For tracking devices and credentials)
Steps
Estimated time: 30-60 minutes
- 1
Identify devices and credentials
Inventory all USG 3P devices and note which still use factory-default or weak passwords. Compile a list of admin accounts and interfaces that require attention. This prepares you for a controlled change with minimal impact.
Tip: Create a centralized, access-controlled list and mark devices with high-risk exposure. - 2
Access management interface securely
Open the device’s admin interface over HTTPS or SSH from a trusted network. Verify you can reach the login page and that you have the current admin credentials documented in the inventory.
Tip: Prefer wired connections for reliability during the change window. - 3
Change the default password
Replace the default password with a long, unique passphrase generated by a password manager. Save the new credential in a secure vault and confirm it is accepted by the device.
Tip: If the device supports MFA, enable it for an extra layer of defense. - 4
Harden other security settings
Disable unused services, restrict admin access to trusted IP ranges, and enable automatic logout. Review firmware to ensure you’re on a supported, secure version.
Tip: Document any changes to policies and access controls. - 5
Test, document, and back up
Test login from all expected management paths. Export a new configuration backup and update the asset record with the new password details. Confirm that monitoring alerts reflect the change.
Tip: Perform a dry run with a spare admin account if available.
Your Questions Answered
What is the risk of leaving the default password on a USG 3P device?
Leaving default credentials creates an easy entry point for attackers, potentially compromising VPN access, firewall rules, and administrative control. Always change defaults as part of initial setup.
Leaving defaults creates easy access for attackers; change them during initial setup.
Can I change the default password without rebooting the device?
In most cases you can change the password via the admin UI without rebooting. Confirm the change is saved and that you can re-authenticate afterward.
You can usually update the password without rebooting.
What should I do if I forget the admin password after a reset?
If you forget the admin password, you may need to perform a recovery procedure per vendor guidelines, often involving a factory reset. Maintain a backup admin account if available.
If you forget it, you may need to reset to factory defaults and reconfigure.
Is two-factor authentication supported on USG 3P?
Two-factor authentication availability varies by model. If supported, enable it, and pair with strong passwords for a layered defense.
Check if 2FA is available and enable it if possible.
How often should I review default credentials across devices?
Schedule regular audits, at least quarterly, and maintain an up-to-date inventory of devices and credentials.
Set a regular schedule to audit device passwords.
Watch Video
Key Takeaways
- Replace default credentials with unique passwords.
- Document changes and back up configurations.
- Limit admin access to trusted networks and log out inactive sessions.
- Regularly audit devices for default credentials.