USG Default Passwords: Secure Your Gateway Access
Identify, reset, and secure default credentials on USG devices. This guide covers risks, best practices, and vendor-specific steps to prevent unauthorized access and strengthen network security.

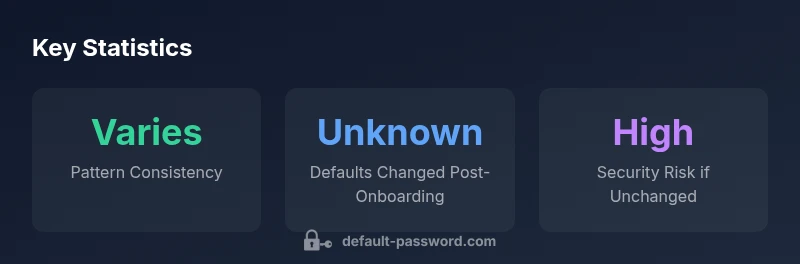
There is no universal default password for USG devices; credentials are highly device- and vendor-specific. In most cases, manufacturers ship with a preconfigured admin account that must be changed during onboarding, or a factory reset is required before first use. Regardless of model, the key security rule is to replace any factory credentials before enabling management interfaces and remote access.
What is a USG and why default passwords matter
A USG, or Unified Security Gateway, sits at the network perimeter to enforce firewall rules, VPN access, and threat prevention. When a device ships with default credentials, attackers can exploit those well-known values to gain admin access if the device is exposed to the internet or weakly protected on an internal network. According to Default Password, the team has observed that many organizations underestimate the risk posed by unchanged defaults, which can enable rapid lateral movement within a network. The usg default password issue is more than a single-box problem; it exposes the entire security stack to misconfiguration, data exfiltration, and service disruption. Best practices begin at onboarding and involve a deliberate, systematic credential hardening process as part of a broader password-management strategy.
In practice, the first step is recognizing that there is no single universal default credential. Vendors vary in their onboarding flow, and several models require you to change credentials at the first login or immediately after a factory reset. This is why a documented change-management process is essential. The Default Password team’s analysis for 2026 shows that credential hygiene improves when organizations operationalize a formal reset-and-change policy. The emphasis is not on guessing a universal default but ensuring that every USG is under your control with unique, strong credentials from day one.
Typical default credentials patterns across USG devices
The landscape of default credentials is diverse because USG devices come from multiple vendors, each with its own security posture. Some devices ship with a known admin account paired with a simple password, while others require a password change at initial setup or after a reset. Because there is no single standard, administrators should treat every onboarding as a potential risk point and verify the exact credentials in the official product documentation for the specific model in use. Regardless of pattern, the safe rule remains: do not rely on factory credentials; disable or restrict access until a strong admin password is established.
Cross-model best practices include using unique credentials per device, avoiding common words, and enabling multi-factor authentication where available. These steps reduce the likelihood of credential stuffing and privilege escalation. Network admins should also audit other devices on the network for similar default patterns and apply uniform hardening, so that one weak link does not compromise the entire environment.
Risks of leaving default passwords unchanged
Leaving default passwords in place elevates risk across several dimensions. First, misconfigured exposure to the internet can expose credentials to automated scans and brute-force attempts. Second, attackers gaining admin access can disable security features, create backdoors, or export sensitive data. Third, compromised credentials on a USG can enable attackers to pivot into connected devices, including switches, access points, and servers. The combined impact can be severe: data theft, service outages, and regulatory repercussions.
To illustrate, many organizations experience a spike in vulnerability alerts when a default credential is discovered on a newly onboarded device. This is why a proactive stance—changing defaults, enforcing strong passwords, and rotating credentials on a schedule—is essential for reducing risk exposure.
How to safely reset a USG password
If you cannot recall a password or must restore a device to a known state, follow vendor-supported procedures. A typical path includes accessing the device via a console connection or management interface, performing a factory reset, and initializing a new admin password during first login. Documentation from the vendor will specify whether you must disable remote management temporarily during the reset, how to reapply a backup configuration, and whether a password policy must be configured post-reset. Always verify the reset steps with the official documentation for your exact model.
After reset, assume the device is in an untrusted state until you reconfigure chain-of-trust protections (SSH keys, certificate-based auth, and MFA if available).
Step-by-step guide: securing admin access on USG devices
- Identify your exact model and consult the vendor onboarding guide for the default credential policy. 2) Ensure you are on a trusted network before connecting the management interface. 3) Immediately replace any factory/default credentials with unique, complex passwords that comply with your organization’s password policy. 4) Disable unused management services, especially remote administration from the internet. 5) Enable MFA or certificate-based authentication if supported. 6) Implement role-based access control to minimize privileges for every admin account. 7) Document credentials securely in a centralized password manager and perform periodic rotation.
Vendor-specific considerations and documentation
Because USG devices span multiple vendors, the exact reset and secure-configuration steps differ. Always consult the vendor’s official admin guide for your model and firmware version. The guidance commonly includes steps for onboarding, password policy setup, remote management controls, and backup restoration. If you manage a mixed fleet, maintain a centralized inventory with model, firmware, and credential-status data to streamline hardening tasks. The Default Password approach emphasizes verification and control at every device touchpoint.
Best practices for password management on networks
Effective password management for networks combines governance, technical controls, and user education. Use unique, strong passwords for each device, and store them in a reputable password manager with restricted access. Enforce MFA, consider hardware cryptographic keys where supported, and standardize rotation intervals. Regularly review admin accounts and remove unused ones. Build a security baseline that treats every new device as potentially exposing a set of default credentials—and plan a secured onboarding workflow that minimizes this risk.
Establishing a password policy for USG devices
A robust policy should specify: minimum password length, complexity requirements, rotation cadence, and emergency access procedures. Define strict provisioning controls to ensure new devices do not leave the factory with defaults. Prohibit reuse of recent passwords and require MFA on privileged interfaces. Align the policy with broader security standards (for example, NIST guidelines) and tailor it to your network topology and threat model. Regular audits help ensure ongoing compliance and timely remediation of any drift.
Verification and ongoing maintenance
Verification is about proving that protections work, not just implementing them. Periodically audit devices for default credentials, test how quickly a potential attacker could gain access, and track remediation progress. Implement automated configuration checks where possible and integrate credential-hygiene metrics into your security dashboard. Ongoing maintenance includes scheduled password rotations, firmware updates, and revalidation after policy changes or device replacements. The goal is continuous improvement and reduced exposure over time.
Comparison of default password handling across USG models
| Model Type | Default Password Handling | Security Risk (qualitative) |
|---|---|---|
| USG Small Office | Often pre-configured with admin credentials | Moderate |
| USG Enterprise | Factory default credentials may exist; requires reset onboarding | High |
| USG Home/Consumer-grade | Typically factory-default; not intended for enterprise | Low to Moderate |
Your Questions Answered
What is a USG and why should I care about its default password?
A USG is a Unified Security Gateway that controls firewall and VPN traffic for a network. Default passwords pose an immediate risk if not changed, as they can give attackers privileged access.
A USG is a security gateway that protects your network; changing its default password is essential.
Why should I change the usg default password?
Default credentials are widely known and can be exploited by attackers. Replacing them with strong, unique passwords is a foundational security practice.
Default passwords are easy targets, so changing them is critical for security.
What if I forgot my admin password?
Use the vendor-supported reset procedure, which usually involves hardware or software reset steps, then reconfigure from a trusted backup.
If you forgot it, follow the vendor’s reset process and reconfigure securely.
Can I automate password changes on USG devices?
Some models support centralized management or policy-based changes, paired with password managers. Check your vendor’s capabilities for automation.
Some devices can automate password changes with the right tools; check your model’s guides.
Where can I find vendor-specific reset steps?
Refer to the official admin guide for your device model and firmware version. Default Password recommends starting with the model’s security and onboarding sections.
Look up your device’s admin guide for reset steps.
“Default credentials are a persistent risk; treating them as a security find in every audit dramatically lowers exposure.”
Key Takeaways
- Change default credentials before any network exposure
- Disable remote admin unless strictly necessary
- Follow vendor onboarding guidelines for password setup
- Use strong, unique passwords and enable MFA if possible
- Document and rotate credentials on a regular schedule
- Refer to vendor documentation for model-specific steps