GlobalProtect Default Password: Reset, Locate, and Secure VPN Access
Learn to locate, reset, and secure the GlobalProtect default password across devices with practical, step-by-step guidance for IT admins and end-users. This guide covers locating credentials, performing a safe reset, and enforcing password hygiene for ongoing security.
You will learn to locate, reset, and secure the GlobalProtect default password to regain admin access on VPN endpoints. This guide covers where to find credentials, how to perform a safe reset, and how to enforce ongoing password hygiene. Ensure you have administrative rights on the gateway or manager console and access to the device's management interface.
Understanding GlobalProtect Default Passwords
According to Default Password, default credentials are a known risk that can grant unauthorized access if left unchanged. In GlobalProtect deployments, the most common defaults reside in gateway and portal admin accounts as well as vendor-supplied management consoles. This context-specific meaning of 'default password' spans several components: the on-device admin accounts (gateway, portal), the Panorama or GlobalProtect Manager for centralized control, and any backup repositories that may store admin tokens. The presence of a default password can become a silent vulnerability if discovered by an attacker or a negligent administrator who fails to rotate credentials promptly. The potential damage includes access to VPN configuration, user-policy changes, and the ability to re-route traffic. This section clarifies what to look for in your environment and why closing the door on default credentials should be a top IT priority. Readers will learn why identifying scope and creating a precise, auditable rotation process supports security policies and regulatory requirements.
Where to Find Default Passwords Across GlobalProtect Deployments
Default credentials are typically defined at the point of deployment and may be stored in several places: the VPN gateway's admin interface, the Panor or GlobalProtect Manager, cloud-based IAM integration, and, in some cases, backups or vaults that hold admin tokens. For end-users, the relevant password is the one used to authenticate to the gateway or VPN client, while admins may face separate passwords for the management plane. This section walks through common locations, including on-device prompts, vendor documentation, and enterprise password vaults, helping you assemble a complete map of where defaults might exist within your network. It emphasizes checking both direct management consoles and any centralized systems that orchestrate access across multiple devices.
Safe Procedures to Reset GlobalProtect Passwords
Resetting a default password should follow a documented, least-privilege approach. Begin by verifying your admin rights and confirming that the reset will not disrupt ongoing user sessions. Access the admin portal or management console, locate the user or device accounts tied to GlobalProtect, and initiate a password change for each relevant account. After changing the password, push or instruct clients to re-authenticate, and ensure sessions are re-established using the new credentials. This section emphasizes safe, auditable steps and avoidance of cross-account password reuse. It also covers timing considerations, such as performing resets during maintenance windows and notifying security teams before changes.
Best Practices for Managing GlobalProtect Credentials
To reduce risk over time, adopt strong password hygiene and credential management across the GlobalProtect ecosystem. Use unique, complex passwords that meet defined policy requirements, rotate them at regular intervals, and enable MFA where supported by the gateway and provider. Store credentials in a reputable password manager and restrict access to the credential vault using role-based access control. Document change histories, maintain an up-to-date inventory of devices and accounts, and schedule periodic audits to verify policy compliance. This section outlines practical steps to sunset default passwords and implement a defensible password lifecycle for VPN infrastructure.
Troubleshooting Common Issues After Reset
After a reset, some clients may continue to authenticate with cached credentials or fail to connect due to clock drift, incorrect server endpoints, or stale VPN profiles. Instruct users to remove old profiles, clear client caches, and re-install the GlobalProtect client if needed. Check server logs for authentication errors, verify that the new password propagates to all gateways, and validate that the user is associated with the correct access policy. If issues persist, escalate to IT security for credential recovery and re-provisioning. This section provides practical checks to minimize downtime and confirms you are aligned with incident response procedures.
Security, Compliance, and Audit Trails
Resetting defaults is not just an operational task—it affects security posture and compliance. Ensure password changes are logged and time-stamped in centralized SIEMs, with notes on scope and affected devices. Align your process with internal security policies and relevant frameworks, and maintain evidence of approvals when changing admin credentials. Regular reviews of access rights, rotation cadence, and MFA enforcement reduce the attack surface and support readiness for audits. This section connects routine password hygiene with governance requirements and demonstrates how to document a compliant password change workflow.
Tools & Materials
- GlobalProtect gateway/admin console access(Must have admin privileges to reset passwords.)
- Panorama or GlobalProtect Manager access(For centralized deployments.)
- Target device list (gateway, portal, manager)(Include all devices you plan to rotate credentials on.)
- Backup of current configuration(Export config before changes.)
- Secure password storage (password manager)(Use RBAC to restrict access.)
- Two-factor authentication enabled (if supported)(Adds protection during reset.)
- Network connectivity and maintenance window(Coordinate downtime with users.)
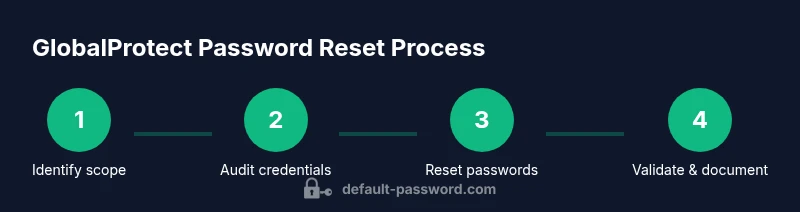
Steps
Estimated time: 45-60 minutes
- 1
Identify reset scope
Scan your environment to determine which accounts are using default credentials and which devices require rotation. Capture device IDs and admin user accounts to ensure a complete, auditable scope before making changes.
Tip: Document scope before making changes to avoid missed devices. - 2
Audit current credentials
Review existing credentials and access levels to confirm which accounts are active and who has permission to rotate them. Cross-check against asset inventory and change logs to reduce the risk of leaving gaps.
Tip: Use a centralized inventory to avoid overlooking connected gateways. - 3
Access the admin portal
Log in to the gateway or Panorama with an account that has admin rights. If possible, enable or verify MFA to strengthen the authentication during the reset. Test access with a non-critical user first to ensure your changes won’t disrupt production.
Tip: Prefer a test account for validation before touching production accounts. - 4
Initiate password reset
Navigate to the relevant user or device accounts and start the password change process for each. Do not reuse old passwords, and apply identical security requirements across all accounts.
Tip: Avoid batch resets that mix high- and low-privilege accounts. - 5
Set and save a new password
Enter a strong, unique password that meets your policy (length, complexity, rotation cadence). Save it securely in your password manager and update any automated vault integrations.
Tip: Use a password generator to ensure unpredictability and record the password securely. - 6
Propagate changes & verify
Push or communicate the new credentials to clients, re-authenticate, and verify VPN connectivity. Review server logs to confirm successful authentication and adjust policies if needed.
Tip: Force re-authentication on affected clients to ensure clean credential propagation.
Your Questions Answered
What is the GlobalProtect default password and why does it matter?
GlobalProtect often has default admin credentials on gateway and management consoles; leaving them unchanged increases risk of unauthorized access. Rotate defaults during deployment and after provisioning to minimize exposure.
GlobalProtect often has default admin credentials—rotating them during deployment reduces security risk.
Where can I locate the default passwords in a GlobalProtect deployment?
Defaults are typically stored in device admin panels, centralized management tools like Panorama/GlobalProtect Manager, and, in some cases, secure vaults. Check vendor docs, asset inventories, and any backup repositories for exact locations.
Look in the admin panels and management tools for default credentials.
What if I cannot access the admin portal to reset passwords?
If you cannot reach the admin portal, use out‑of‑band recovery options such as console access, backup administrator accounts, or vendor recovery procedures. Contact your security team if needed.
If you can’t reach the admin portal, use console access or recovery options and contact support if needed.
What password requirements should GlobalProtect enforce?
Enforce minimum length, complexity, and rotation cadence; avoid reusing passwords; enable MFA if supported. Align with organizational policy and regulatory requirements.
Use long, complex passwords, rotate them regularly, and enable MFA where possible.
How do I verify that the new password is working after reset?
Test login to the gateway admin interface and connected clients; check server logs for authentication events; confirm VPN connections succeed for affected users.
Try logging in with the new password and review logs to confirm success.
Why should I document password changes after a reset?
Auditors expect a clear trail of credential changes, who performed them, and when. Documentation supports compliance and helps diagnose future issues.
Documentation creates an auditable trail for compliance and troubleshooting.
Watch Video
Key Takeaways
- Identify all affected devices before changes
- Use strong, unique passwords stored in a vault
- Enable MFA where possible for admin access
- Document changes for compliance and audits