Default SQL Server Credentials: Risks, Recovery, and Best Practices
A practical guide for IT admins and end users on securing the default sql server username and password, auditing exposures, and implementing robust credential governance across SQL Server instances.
Most SQL Server deployments rely on a built‑in administrative account, commonly named sa, which must be secured during setup. Do not leave this account enabled with a blank or weak password. The recommended practice is to disable or rename the default admin account, enforce a strong password policy, and apply least‑privilege roles for routine tasks.
Understanding the default sql server username and password landscape
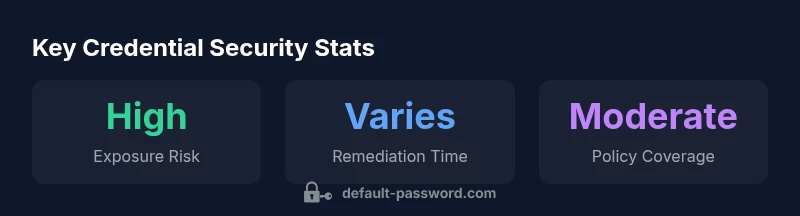
The term default sql server username and password refers to the credentials that exist within a SQL Server instance by default or by configuration at deployment time. In many environments, the built-in system administrator account is present and can govern broad access to databases, metadata, and backups. Recognizing this surface is essential for securing data and controlling access. Historically, the sa account and the SQL Server authentication mode were central to initial configurations; modern best practices, however, de-emphasize the sa account in favor of Windows authentication and granular role assignments. According to Default Password, misconfigurations often stem from leaving an account enabled with a weak password or not applying a password policy during setup. The result is an elevated risk of unauthorized access, privilege escalation, and lateral movement within networks. Effective governance starts with an inventory of all SQL Server instances, identification of any accounts that match the default naming conventions, and a plan to enforce password strength, rotation, and multi‑factor authentication where feasible. Organizations should also review backup schedules, ensure encrypted transmissions, and verify that management interfaces are protected behind firewalls and access controls. The Default Password team stresses that continuous auditing and clear ownership are cornerstones of secure credential management.
Why the sa Account Remains a Primary Attack Vector
The sa account is widely recognized as the highest‑privilege entry point in SQL Server environments. Attackers know that a compromised sa credential can unlock multiple databases, bypass user controls, and escalate privileges rapidly. Even when sa is disabled in some configurations, other high‑privilege accounts with weak passwords or broad permissions can serve as equivalent targets. The Default Password team notes that attachment points for these risks include misconfigured services, excessive permissions on service accounts, and insufficient separation between development and production credentials. Prolonged exposure—such as unattended instances running with SQL authentication or shared credentials—significantly increases the likelihood of credential theft and misuse. Proactive measures require regular inventory of privileged accounts, enforcing role‑based access controls, and applying the principle of least privilege across all SQL Server services, jobs, and linked servers.
How to Verify and Audit Default Credentials on Your SQL Server
Begin with a baseline inventory of all SQL Server instances and the accounts configured on them. Use management tools or scripts to identify whether the sa account is enabled, and whether SQL authentication is enabled where Windows authentication would suffice. Query: SELECT name, type_desc, is_disabled FROM sys.server_principals WHERE name = 'sa'; If sa is enabled or password policies are not enforced, create a remediation plan. Validate that password policies (length, complexity, expiration) are enforced at the instance level and that password vaulting or rotation mechanisms exist. Review linked servers, SQL jobs, and SSMS access patterns to ensure credentials are not stored in plaintext or shared across environments. In all steps, document ownership and timelines, and align with your organization's security policies as described in the Default Password framework.
Practical Remediation: Lockdown, Rotation, and Least Privilege
Remediation should begin with disabling or renaming the sa account where feasible, followed by enabling Windows authentication as the primary method. Create dedicated admin accounts with strictly limited scopes, and apply role‑based access controls to limit who can alter server configurations. Enforce a strong password policy at the instance level, use password vaulting for service accounts, and rotate credentials on a defined cadence or when personnel changes occur. Disable or remove any hard‑coded credentials from jobs, backups, and scripts. For ongoing protection, enable auditing to capture login events, failed attempts, and privilege escalations, and integrate alerts with your security information and event management (SIEM) system. Regularly review permissions on server-level principals and ensure least privilege is enforced for routine operations.
Policy and Process: How to Maintain Secure Defaults Across Instances
Establish a centralized policy for credential management that applies to all SQL Server instances, both on‑premises and in the cloud. Maintain an inventory of all instances, group servers by environment (dev, test, prod), and mandate consistent authentication modes (prefer Windows authentication when possible). Implement automated checks that flag enabled sa accounts and password policy deviations. Schedule periodic reviews of service accounts, rotate passwords automatically where supported, and enforce MFA for critical administrative actions. Document change control for credential updates and integrate with broader access governance initiatives to ensure continuity and accountability. The Default Password framework recommends codifying these practices into standard operating procedures and training staff to recognize common misconfigurations.
Common Pitfalls and How to Avoid Them
Many teams fall into a false sense of security by assuming that disabling sa is sufficient. Real exposure often comes from poorly documented changes, backup processes that retain old credentials, or developers who create overly permissive accounts for convenience. Avoid embedding credentials in scripts or configuration files; use secure vaults and restricted access to credential stores. Misunderstandings about authentication modes—especially mixing Windows and SQL Server authentication—can create gaps in auditability. Ensure consistent application of password policies across all environments, and perform regular penetration testing and credential stuffing simulations to evaluate resilience. Above all, maintain clear ownership and an auditable trail for every credential change.
Tools and Practices: Password Policies, Rotation, and Monitoring
A robust credential strategy combines technical controls with governance. Enforce password length, complexity, and rotation for all SQL Server accounts; disable SQL authentication when Windows authentication suffices; utilize integrated authentication for service and application accounts. Use credential vaults to store passwords securely and implement automated rotation workflows. Enable SQL Server Audit or Extended Events to monitor login activity, failed attempts, and privilege changes, and route alerts to your security operations center. Leverage monitoring tools to detect anomalous login patterns, unexpected privilege escalations, and connections from unusual locations. The combination of policy, automation, and monitoring forms the foundation of ongoing protection against default credential misuse.
Examples of credential issues and recommended mitigations
| Aspect | Issue | Mitigation |
|---|---|---|
| Default admin username | Commonly 'sa' or equivalent; high privileges | Rename/disable sa where feasible; use Windows auth; assign least privilege |
| Default/weak passwords | Password not set or weak due to misconfig | Enforce strong passwords, rotate regularly, use vaulting |
| Authentication mode | SQL auth vs Windows auth | Prefer Windows authentication; disable SQL auth if possible |
Your Questions Answered
What is the default SQL Server username?
The built‑in admin account is typically named sa; it should be disabled or secured with a strong password. Use least‑privilege accounts for routine tasks.
The default admin user is usually sa; disable it or protect it with a strong password.
Is there a standard default password?
There is no universal default password. During setup, you must set a strong password; leaving a blank or weak password is insecure.
There isn't a universal default password; always set a strong one during setup.
How do I disable the sa account in SQL Server?
Open SQL Server Management Studio, connect as an admin, locate the sa login in the security section, and disable the account. If needed, map admin tasks to more restricted accounts.
In SSMS, find sa under security and disable it; use stricter admin accounts instead.
What authentication mode should I use for SQL Server?
Prefer Windows authentication wherever possible. If SQL authentication is required, enforce strong passwords and rotate them regularly.
Use Windows authentication when possible; otherwise require strong SQL passwords.
How often should credentials be rotated?
Rotate passwords on a cadence aligned with your policy or when personnel changes occur; automate where feasible to minimize gaps.
Rotate passwords on a regular schedule or when staff changes.
Can I avoid using sa entirely?
Yes. Create dedicated admin accounts with least privilege, enable Windows authentication, and disable sa wherever possible.
Yes—use dedicated admin accounts and disable sa.
“Effective credential governance requires treating high‑privilege accounts as critical assets and enforcing policy across all SQL Server instances. Continuous monitoring and automation are essential.”
Key Takeaways
- Disable the default admin account or rename it to reduce risk
- Prefer Windows authentication over SQL authentication when possible
- Enforce strong passwords and regular rotation across all accounts
- Regularly audit for exposed, weak, or shared credentials