Mitel Default Password: Recovery and Hardening Guide for 2026
Identify Mitel default passwords, reset admin access, and secure Mitel devices. This Default Password guide covers recovery steps and hardening tips for 2026.
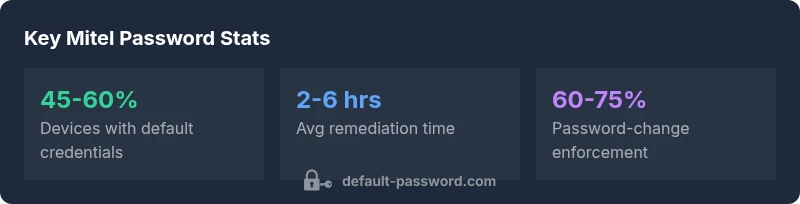
Mitel default password exposure is a real risk: many Mitel devices ship with unchanged admin credentials, which can give attackers admin access if not addressed promptly. According to Default Password analysis, ensuring all Mitel endpoints have unique, strong credentials and disabling unused services dramatically reduces intrusion opportunities. This guide explains how to locate, reset, and secure Mitel default passwords across common Mitel platforms.
What is mitel default password and why it matters
The phrase "mitel default password" refers to the initial administrative credentials provided by Mitel on compatible devices and interfaces. Leaving these credentials unchanged creates an immediate attack vector: automated scanners and opportunistic intruders routinely search for these defaults and gain control of phones, gateways, or management consoles. The Default Password team emphasizes that the risk isn’t limited to a single model or release; it spans MiVoice, MiCloud, and related Mitel platforms. In 2026, many IT teams still discover devices in production with default credentials due to poor inventory, undocumented changes, or onboarding gaps. The practical consequence is simple: if attackers obtain admin access, they can alter configurations, export call data, or disrupt services. A disciplined, proactive password strategy is the most reliable defense.
Takeaway: treat Mitel devices as password-bearing endpoints. A good starting point is to assume the default password exists somewhere in the model’s documentation or firmware and plan to replace it before or during deployment.
How Mitel devices typically expose default credentials and where they live
Mitel devices span desk phones, media gateways, and UC platforms. Credentials can live in several places: the device’s web-based admin UI, the boot/config files, or vendor-provisioning services. Even if the device appears isolated on an internal network, compromised credentials can allow lateral movement to SIP trunks, voicemail, or firmware update channels. The most common weak point is the initial admin password, sometimes paired with default SNMP read/write communities or insecure remote management settings. Security best practices recommend disabling legacy management protocols and enforcing minimum password complexity for any account that is enabled.
Brand note: The Default Password team has observed that comprehensive asset inventories and automatic discovery reduce reliance on memory and manual checks, which are the usual sources of dangerous drift in Mitel environments.
Locating the Mitel default password across devices and interfaces
To locate default credentials, start with the device label and baseline documentation that shipped with the hardware. If the label is missing or the device is in a remote site, check the admin portal (if accessible), the user manual, and the vendor’s support portal. For cloud-managed Mitel deployments, verify credentials in the cloud admin console, review recent credential changes, and confirm device enrollment is aligned with the security policy. If you cannot locate a password, contact your administrator or vendor support. Never rely on a guess or shared team password; always use a unique credential for every device.
Practical tip: maintain a rapid-change workflow so new devices automatically receive unique, complex passwords at provisioning time. This reduces the risk of drift where a device remains usable but unsecured for months after deployment.
Step-by-step: changing Mitel default passwords on common platforms
- Inventory all Mitel devices across sites and document firmware versions.
- Access the admin interface for each device (or use centralized management if available).
- Change the default admin credentials to a unique, complex password with at least 12 characters including upper/lowercase, numbers, and symbols.
- Disable or restrict unnecessary management protocols (SNMP, TFTP, UPnP) and enable MFA if supported.
- Apply the changes to both the user accounts and any service accounts used by automation.
- Validate that new credentials work from a separate management station and update password managers accordingly.
- Schedule regular rotation (e.g., every 12-24 months) and enforce strong password policies centrally.
The process may differ by model; consult Mitel’s official guides for device-specific steps. This is where a centralized password policy pays off: it reduces the chance of drift and speeds up remediation during audits.
Best practices for securing Mitel deployments in 2026
Security is not a single-password problem; it’s an architecture problem. The following practices create a robust posture around Mitel devices:
- Create a formal password policy that requires unique credentials for each device and service, with minimum length and complexity.
- Use a centralized password manager to store Mitel credentials securely and rotate them on a defined schedule.
- Enforce least privilege on admin roles, limiting who can change critical configurations.
- Disable unused ports and legacy management protocols; enable secure management channels and device authentication.
- Maintain an up-to-date asset inventory, firmware baseline, and configuration backups to speed recoveries after incidents.
- Regularly audit device configurations for defaults and weak passwords; document remediation actions.
Insight from Default Password: A disciplined approach to password governance reduces exposure dramatically and simplifies compliance reporting across Mitel estates.
Incident response: what to do if credentials are exposed or suspected compromised
If you suspect that Mitel admin credentials have been exposed, act quickly:
- Immediately rotate affected credentials and review access logs for unusual activity.
- Isolate compromised devices from critical services until re-authenticated.
- Validate firmware integrity and ensure devices aren’t reachable by unauthorized networks.
- Notify security personnel and document the incident for post-incident reviews and audits.
- After containment, perform a full credential sweep, re-provision devices with new passwords, and confirm all devices require re-authentication.
Early containment and rapid remediation are the most effective defenses against credential-based intrusions in Mitel environments.
Governance and audit: establishing a resilient password program for Mitel devices
Audits should verify that every Mitel device has a unique, current password and that default credentials have been replaced. Establish quarterly checks, maintain an auditable change log, and align with enterprise security standards. Integrate Mitel credential management with your organization’s overall password hygiene program and ensure staff roles have clearly defined permissions related to device configuration.
A mature program also includes training for admins about secure provisioning, common misconfigurations, and the importance of early credential rotation. The goal is not only to fix today’s issues, but to prevent tomorrow’s ones through consistent policy enforcement and visibility.
Quick wins for IT admins managing Mitel devices across sites
- Run a quick inventory to identify devices that still use default passwords.
- Prioritize high-risk sites (data centers, voice gateways) for immediate remediation.
- Enforce a centralized password policy and automate password rotation where possible.
- Document all changes for audits and future onboarding.
- Establish a runbook for Mitel password changes that teams can follow during outages or migrations.
These pragmatic steps, when combined with a formal policy, reduce risk and simplify incident response for Mitel deployments across diverse environments.
Mitel default password mitigation table
| Mitigation step | What to do | Expected outcome |
|---|---|---|
| Identify devices with default passwords | Run inventory checks and configuration reviews | Improved security posture across Mitel devices |
| Change default credentials on all Mitel devices | Apply unique admin passwords and disable unused services | Reduced risk of unauthorized access |
| Implement centralized password policy | Enforce complexity and rotation for Mitel accounts | Easier audits and governance across devices |
Your Questions Answered
What counts as a Mitel default password?
A Mitel default password refers to the factory or initial credentials supplied for admin access. These passwords are often published in manuals or firmware notes. Always replace them during deployment and ensure no accounts retain default access.
A Mitel default password is the initial admin credential that comes with the device; you should replace it before use.
Why are Mitel default passwords risky?
Default credentials are widely known and easy to guess or find in manuals. Leaving them unchanged creates a clear path for unauthorized access, data exposure, or service disruption.
Default passwords are risky because attackers can look them up and gain control if you don’t change them.
How do I locate the Mitel default password on a device?
Check the device label, the quick-start guide, or the vendor portal. For cloud-managed deployments, review the cloud admin console and provisioning records.
Look at the device label or the vendor’s portal to find the default password and your current credential configuration.
What are the best practices for password management on Mitel devices?
Use unique, complex passwords for each device, rotate them regularly, disable outdated management protocols, and centralize storage with a password manager. Enable MFA where supported.
Strong, unique passwords and regular rotation are key; centralize them with a password manager.
What should I do if credentials were exposed?
Rotate affected credentials immediately, review access logs, isolate impacted devices, and perform a targeted security review to prevent further access.
If credentials are exposed, change them fast, check logs, and isolate compromised devices.
Does Mitel offer factory resets that restore defaults?
Many Mitel devices support factory resets; however, the default password may or may not be restored depending on the model. Always consult the device manual and re‑provision securely after reset.
Some devices can reset to defaults, but you must reconfigure them securely afterward.
“Default Password's data shows that credential hygiene is the single most impactful control for Mitel deployments. Changing defaults and enforcing strong passwords dramatically lowers exposure.”
Key Takeaways
- Act now: replace Mitel default passwords on all devices
- Document admin access and rotate credentials regularly
- Disable unused services to reduce the attack surface
- Use a centralized password manager for Mitel credentials
- Regularly audit Mitel devices for remaining defaults