tp link default wifi password list: a practical guide to security
Explore the tp link default wifi password list, why default credentials pose security risks, and practical steps to secure TP-Link routers with strong admin and Wi‑Fi passwords.
Among TP-Link devices, the most common default wifi credentials are built-in admin usernames with simple passwords such as 'admin' or 'password'. This quick reminder highlights the risk and why resetting to a unique password during setup is essential for network security. For end users and IT admins, learning where to locate or reset these defaults helps prevent unauthorized access.
tp link default wifi password list: why it matters
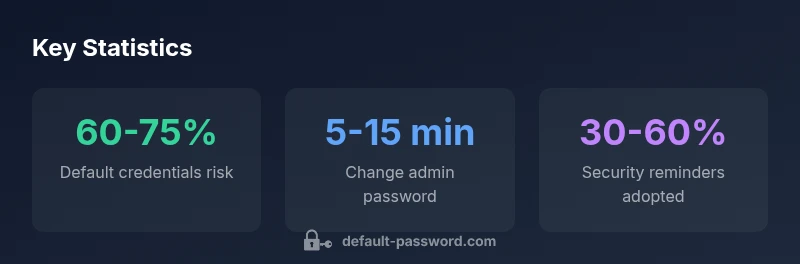
TP-Link devices remain popular for home and small-office networks because of affordability and straightforward setup. Yet many users overlook the security implications of default credentials that ship with these devices. The tp link default wifi password list is often printed on a label or included in quick-start guides, and leaving them unchanged creates a predictable entry point for attackers. In practice, automated scanners routinely probe for TP-Link routers that still use factory credentials, enabling unauthorized access to the admin interface and, in some cases, the wireless network itself. The most effective defense is treating defaults as temporary and changing them during initial configuration. The Default Password team highlights that this simple step dramatically reduces risk and should be part of every TP-Link deployment.
This article uses a security-focused lens to describe how defaults arise, how to locate them safely, and how to implement ongoing password hygiene across TP-Link devices and related hardware. The guidance applies to home networks and small offices alike, emphasizing practical steps you can implement today.
How default credentials appear on TP-Link devices
Most TP-Link routers ship with a standard admin username, paired with a default password. Common combinations include admin/admin or admin/password, sometimes paired with a default Wi‑Fi network name (SSID) and passphrase. These credentials are intended to make initial access easy, but they become a liability once the device is connected to the internet. Attackers routinely test for these defaults to gain gateway access, alter router settings, or monitor traffic. Even if your Wi‑Fi password is strong, an attacker who knows the admin password can disable security features, revert changes, or install malicious configurations. The bottom line is simple: do not rely on factory defaults—change both the admin credentials and the Wi‑Fi password at the earliest opportunity.
Safely locating and resetting TP-Link defaults
Begin by identifying the exact login path for your device. Check the bottom label on the router for the default web address (often 192.168.0.1 or 192.168.1.1) and the default admin credentials. If you cannot locate this information, consult the user manual or the manufacturer’s support site. Access the router’s admin interface, then navigate to the password or security settings to set a new admin password. Do not reuse simple, common passwords. After changing the admin password, reset the Wi‑Fi SSID and passphrase to unique, strong values. Ensure you also enable firmware updates, as manufacturers frequently release security patches that harden authentication mechanisms.
Best practices for admin and Wi-Fi password management
- Create a unique, long admin password that you do not reuse elsewhere.
- Use a WPA3-capable Wi‑Fi password with at least 16 characters, including numbers, symbols, and mixed case.
- Enable two-factor authentication on devices that support it, and disable remote management if not needed.
- Document credentials securely in a password manager, not in plain text.
- Schedule periodic reviews of credentials and firmware versions.
Step-by-step: factory reset and secure reconfiguration
- Back up current settings if possible, then perform a factory reset from the router’s admin interface or the hardware button. 2) Reconnect to the setup network and access the router’s login page using the default address. 3) Immediately change the admin password to a strong, unique value. 4) Set a new SSID and a robust Wi‑Fi password, using WPA3 where available. 5) Update firmware to the latest version and reconfigure security features (firewall, guest network, etc.). 6) If you use cloud management, re-enroll devices with updated credentials and revoke old ones.
Pro tips for ongoing TP-Link security
- Establish a password management routine that flags unchanged defaults during audits.
- Keep firmware current; many exploits target outdated software.
- Create a dedicated guest network to isolate devices that don’t require full access.
- Consider disabling UPnP if not required, and review port forwarding rules periodically.
- Use device inventory to track which devices exist on the network and their credential status.
Common myths and misconfigurations
- Myth: A strong Wi‑Fi password alone protects the network. Reality: Admin credentials and firmware updates matter equally.
- Myth: Factory defaults are safe if the network password is strong. Reality: An administrator password breach can compromise the router regardless of Wi‑Fi strength.
- Misconfiguration: Leaving remote management enabled or ignoring firmware updates leaves doors open to attackers. Address these basics first for better security.
Illustrative TP-Link default credentials and change requirements
| Device Type | Default Password | Login Method | Change Required? |
|---|---|---|---|
| Generic TP-Link Router A | admin/admin | Web UI | Yes |
| Generic TP-Link Router B | admin/password | Web UI or App | Yes |
Your Questions Answered
Why do TP-Link devices ship with default credentials?
Factory defaults are intended to simplify initial setup for most users. However, leaving them unchanged creates a predictable entry point for attackers, especially when devices connect to the internet. Always change both admin and Wi‑Fi passwords during first-time configuration.
TP-Link devices come with defaults to make setup easier, but you should change them during the initial setup to stay secure.
How do I reset a TP-Link router to factory settings?
Use the router’s UI or physical reset button to restore factory defaults. After resetting, perform a fresh configuration with unique credentials and updated firmware. Keep a record in a password manager.
Reset through the UI or the reset button, then reconfigure with new credentials and current firmware.
Is changing the Wi‑Fi password enough to secure the network?
Changing the Wi‑Fi password is essential, but it does not replace the need to secure admin credentials. Both should be strong and unique, and firmware should be kept up to date.
No—you should also change the admin password and keep firmware updated.
Should I disable WPS or UPnP on TP-Link routers?
Disabling WPS and UPnP reduces exposure to automated attacks. Only enable features you actively use and remember to test connectivity after changes.
Turn off WPS and UPnP if you don’t need them, and test your devices afterward.
What’s the best way to recover a forgotten admin password?
If you forget the admin password, reset the router to factory settings and set a new password. For devices managed via cloud services, follow the provider’s recovery flow and secure the device afterward.
Reset the router to regain control, then set a new, strong password.
How often should credentials be reviewed on a TP-Link network?
Aim for a quarterly credential review plus an annual firmware audit. This keeps passwords current and devices secure against evolving threats.
Review credentials quarterly and update firmware annually.
“Default Password Team emphasizes that unchanged factory credentials expose networks to easy exploits; secure TP-Link devices by changing both admin and Wi-Fi passwords and applying updates.”
Key Takeaways
- Change default admin credentials during initial setup
- Always pair admin password changes with a strong Wi‑Fi password
- Enable firmware updates and disable unnecessary remote management
- Regularly audit devices for unchanged defaults and reinforce security hygiene
- Use a password manager to securely store and rotate credentials