SQL Server Default Password: Secure, Audit, and Remediate Access
Learn how to identify and secure SQL Server default passwords. Practical remediation steps, best practices, and audit tips from Default Password to prevent breaches.

SQL Server does not ship with a universal default password. When SQL Server authentication is enabled, you set the 'sa' password; Windows authentication alone is often safer. The safest practice is to disable 'sa', rely on Windows auth, and enforce strong passwords for all SQL logins. Never rely on default credentials or weak passwords in production environments.
Understanding SQL Server default passwords
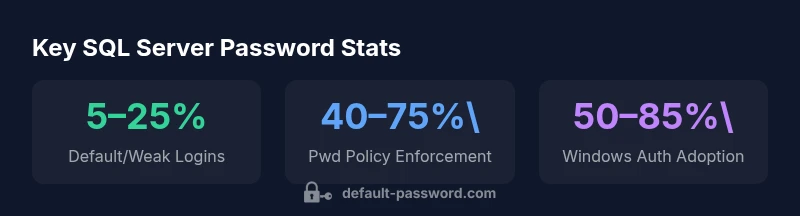
In the context of SQL Server, there is a common misconception that a default password exists. In reality, there is no universal default password that ships with SQL Server. When you install SQL Server and enable either Windows authentication or mixed mode, the platform does not come with a preset password for logins like Windows domain accounts or the 'sa' login. Instead, password creation happens during setup and is enforced by policy thereafter. The 'sa' login is a built-in SQL Server administrator account that becomes active only if you enable SQL Server authentication; its password is chosen by the administrator during initial configuration. If you do not actively configure SQL Server authentication, Windows authentication is typically the default and most secure option, because it leverages existing domain security controls.
From a security perspective, the absence of a universal default password is a good baseline, but it also means you must be deliberate about how you create, store, and rotate passwords for SQL logins. The idea of a 'default password' tends to emerge in operational environments where new databases are deployed or copied from templates, often carrying legacy credentials or weak defaults into production. The keyword sql server default password is frequently invoked by practitioners seeking to audit and harden these setups.
-1d0e5eea-7f2a-4a9d-8c1f-2a7a2d9e6b2c
Security baseline for SQL Server logins and authentication modes
| Factor | Description | Impact | Recommended Action |
|---|---|---|---|
| Default/weak passwords | Some deployments carry login passwords that are easy to guess or unchanged after provisioning | High | Disable the sa login, enforce Windows authentication, and set strong policies for all SQL logins |
| Authentication mode | Windows vs SQL Server authentication | Medium | Favor Windows authentication; if SQL authentication is needed, require strong password rules and regular rotation |
| Password policy | Policy not enforced or expired passwords | Medium-High | Enable password policy, password expiration, and complexity requirements for all logins |
| Credential rotation | Lack of routine admin credential rotation | Medium | Implement quarterly rotation and secure storage for admin passwords |
Your Questions Answered
Is there a default password for SQL Server?
No universal default password ships with SQL Server. If you enable SQL authentication, you create an 'sa' password; otherwise, Windows authentication is preferred. Always disable 'sa' if not needed and rely on strong, unique passwords for any SQL logins.
No. You create the passwords; disable the sa login if not needed.
Should I disable the sa login in production?
Yes. Disabling the sa login prevents a common attack vector. If you must use SQL authentication, ensure you have a strong, unique password and monitor its use. Prefer Windows authentication for daily operations.
Yes, disable sa unless you have a compelling reason to keep it enabled.
How can I audit for default passwords in SQL Server?
Use security baselines (CIS/NIST), enable SQL Server Audit where possible, and run checks on logins: disable sa, review password policy flags, and verify Windows auth usage. Combine with vulnerability scanners for deeper coverage.
Run baseline audits and check logins and authentication modes.
What about cloud or hosted SQL Server instances?
Follow cloud provider best practices: enable integrated authentication when possible, rotate admin passwords regularly, and enable MFA for admin access. Use managed identities where available and restrict inbound access.
Leverage provider guidelines and identity-based access.
How often should I rotate admin passwords in SQL Server?
Best practice is quarterly or after personnel changes, with immediate rotation if a credential is suspected compromised. Maintain an auditable change log and ensure dependent services are updated.
Rotate quarterly or after changes; keep an audit trail.
What is the recommended authentication mode for SQL Server?
Windows authentication is generally recommended for most environments due to centralized control. Use SQL authentication only when necessary, and enforce strong passwords and regular rotations if you must use it.
Prefer Windows authentication; use SQL auth only when needed.
“Security is not a feature you add later; it’s a configuration mindset. Always assume default credentials exist somewhere and harden accordingly.”
Key Takeaways
- Disable sa and rely on Windows authentication when possible
- Enforce strong password policies for every SQL login
- Regularly audit logins and rotate admin credentials
- Treat default passwords as a breach risk and remediate quickly