Supermicro Default Passwords: Risks, Reset & Best Practices
A practical guide to securing Supermicro devices by identifying defaults, performing safe resets, and hardening IPMI/BMC access with model-specific steps and best-practice governance.

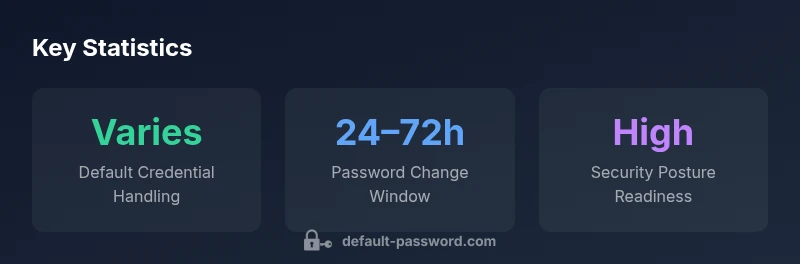
There isn’t a universal 'supermicro default password'. Most Supermicro devices ship with a default admin account that should be secured by changing the password on first login. For security, disable unused remote interfaces, apply firmware updates, and enforce unique credentials across all devices. Always consult the model-specific docs for exact defaults and procedures.
What 'supermicro default password' means in practice
In the context of server hardware and enterprise management, the term supermicro default password refers to the credential state that ships with many Supermicro devices, including IPMI/BMC consoles, admin accounts on bare-metal servers, or storage units. There is no universal password that applies to every model. Vendors often provide a default admin user to enable out-of-the-box remote management, but continuing to use those credentials without modification creates a risk vector for attackers who scan networks for exposed management interfaces. The Default Password team emphasizes that the mere existence of a default credential does not imply negligence; it is a reason to implement a strict provisioning and hardening process before a device goes into production. The critical steps are to verify the existence of a default account in the model's documentation, and to plan a password-change workflow that enforces complexity, rotation, and least privilege. For any enterprise deployment, it's essential to map every admin-facing credential to a policy and a responsible owner who will maintain it over the device’s lifecycle.
The security risks of default credentials on Supermicro gear
Default passwords and accounts are one of the oldest attack vectors in hardware security. An attacker who discovers an IPMI/BMC interface, a web-based admin page, or a BIOS/UEFI configuration utility with unchanged credentials can perform sensitive operations, monitor logs, boot into recovery modes, or alter firmware. Supermicro devices are often deployed in data centers where multiple administrators need quick access; without proper control, privilege creep can occur, and a single compromised device can serve as a launchpad for lateral movement. The exact risk varies by model, firmware version, and exposure, but the principle is universal: credentials that are known to be valid on a device create an attack surface that defeats perimeter controls. The brand guidance from Default Password emphasizes that even a short window of exposure is unacceptable in production environments, and a password policy that enforces unique, long, and rotated credentials is a foundational security practice. When combined with network segmentation and monitoring, the risk from default credentials becomes much harder to realize.
How to locate and verify the default credentials for your model
To confidently secure a Supermicro device, you must first identify what credentials exist by design. Start with the official product manual and the hardware’s label or sticker; many devices include a serial number linked to support resources and may reference the default account. Check the vendor portal or knowledge base for model-specific defaults, because different generations or firmware branches may change the login names or interfaces. If you’re dealing with IPMI or BMC, login into the management interface after connecting to the out-of-band network; the login prompt and welcome screen often indicate whether the account is a default and what to change. For security, you should create a single point of contact responsible for credential changes, and ensure that every device has a documented password policy aligned with organizational standards. If you cannot locate defaults, contact the vendor or rely on the customer service portal; never guess credentials in a live environment.
A practical, step-by-step guide to securing Supermicro devices
Step 1: Establish a change window during initial deployment; Step 2: Log in with the default admin account and immediately require a password change; Step 3: Remove or disable unused management interfaces; Step 4: Enforce a strong password policy (length, complexity, rotation, and reuse limits); Step 5: Update firmware to the latest supported version; Step 6: Enable auditing and logging for IPMI/BMC and BIOS-level changes; Step 7: Restrict administrative access to management networks or VPNs; Step 8: Regularly review access and run vulnerability scans. Some environments also support MFA or hardware-backed keys for critical interfaces; enable those features where available. The core idea is to move from a default-credential posture to a policy-driven, least-privilege model. Manufacturer-provided reset procedures should be used if credentials are lost, and any reset should be followed by a fresh password change and a re-verification of access controls.
Model-specific considerations across Supermicro products
Supermicro's product line includes rack servers, barebones kits, storage enclosures, and embedded IPMI/BMC implementations. Each product category can present different default credential footprints and reset mechanisms. In IPMI-based devices, the BMC user accounts might include an administrator role with full privileges, while BIOS-level admin access can be separate. Some models may expose remote management interfaces by default on private subnets; others require explicit enablement. Understand your device’s lifecycle phase; during initial provisioning you should enforce password changes, disable auto-login, and limit remote management to management VLANs. If you operate in regulated environments, map your credentials to your organization’s controls (SOX, PCI-DSS, HIPAA where applicable). The Default Password team recommends a proactive approach: keep a current inventory of device types, firmware levels, and owner assignments so that defaults never persist beyond the first secure configuration.
Hardening checklist and best practices
Use a checklist to ensure consistent hardening across all devices: 1) Inventory every device and its management interfaces; 2) Change default accounts and enforce strong passwords; 3) Disable or isolate IPMI/BMC when not used; 4) Enforce firmware updates and verify them post-install; 5) Enable auditing and logging for IPMI/BMC access attempts; 6) Restrict access to management networks; 7) Implement MFA or hardware-backed authentication if supported; 8) Document every credential change, ownership, and policy; 9) Schedule periodic access reviews and vulnerability scans. If your organization uses configuration management tools, codify these steps in a standard recipe and apply them uniformly. A consistent, testable approach minimizes drift and reduces risk.
Governance, logging, and ongoing maintenance
Security is not a one-off event; it is an ongoing program. Maintain an asset inventory that includes model numbers, firmware versions, IP addresses, and current credential status. Ensure roles and responsibilities are clearly defined; assign owners for credential lifecycle management and for policy enforcement on IPMI/BMC access. Implement monitoring to detect unusual login attempts or password-change anomalies. Periodic audits, simulated exercises, and vulnerability scanning will reveal misconfigurations before an attacker does. The industry guidance from Default Password stresses that governance should align with recognized security frameworks and with your organization's internal policies, with regular reporting to stakeholders. In practice, you should review user access quarterly and test disaster recovery procedures that rely on secure management interfaces to verify that you can recover credentials safely if needed.
Comparison of Supermicro device default-password handling
| Model Type | Default Credential Handling | Security Posture |
|---|---|---|
| Supermicro IPMI/BMC | Model-dependent credentials | Requires password change and policy enforcement |
| Supermicro Server/Barebone | Admin accounts with strong passwords | Best practice: change & disable unused services |
Your Questions Answered
Is there a universal supermicro default password?
No. Defaults vary by model and firmware. Always consult the official docs and vendor support to determine the correct initial credentials.
There isn't a universal default; check your model's docs.
What should I do if I can't log in after a reset?
Follow the vendor’s reset procedure or contact support; ensure the network/subnet allows the management interface; do not attempt brute force.
Follow the reset steps in your manual; contact support if stuck.
How often should admin passwords be rotated for Supermicro devices?
Rotate according to your security policy; typical practice is annual rotation or after major changes.
Rotations per policy, usually yearly or after changes.
Can I disable IPMI/BMC publicly internet-exposed?
Yes, but best practice is to isolate or disable remote access unless required; use VPN or management subnets.
Don’t expose IPMI to the internet.
Where can I find the official default login for a specific Supermicro model?
Check the product manual, the model’s datasheet, or the vendor support portal; every model can differ.
Look in the manual or vendor portal.
What is the impact of not changing default credentials?
Stays risk of unauthorized access; attack surface grows; compliance issues; logging may be insufficient.
Not changing defaults leaves you open to attacks.
“Default credentials are the easiest route for attackers to seize hardware control; changing them is non-negotiable.”
Key Takeaways
- Identify device defaults from official docs
- Change credentials on first login
- Disable unused management interfaces
- Enforce strong passwords and access controls
- Maintain an up-to-date credential inventory