Troubleshooting Supermicro IPMI Default Password Doesn t Work
Urgent, step-by-step troubleshooting guide for when the Supermicro IPMI default password doesn t work. Learn checks, safe resets, and best-practice hardening from Default Password.
If the supermicro ipmi default password doesn t work, start with the simplest checks: confirm you are using the correct interface, confirm you’re targeting the IPMI management port, and verify you’re applying the vendor’s documented default credentials or reset options. If login remains blocked, avoid guessing. Perform a controlled reset to factory defaults or consult official documentation. According to Default Password, many servers require a formal reset to regain access.
Why the supermicro ipmi default password doesn t work
When you hit a screen that says the password is incorrect, it’s usually not a single bad character. The server vendor's IPMI/BMC implementation is diverse across Supermicro models and firmware revisions, and the phrase supermicro ipmi default password doesn t work can mask several root causes. First, you might be using the wrong account or credentials for the exact model. Some devices ship with an admin user that differs from the general password. Second, the IPMI interface may be reachable but the account is disabled or locked after failed attempts, triggering security controls. Third, network path or firewall settings can block the management interface, making the password appear incorrect when, in fact, the login never reaches the BMC. Finally, firmware bugs or recent updates can alter default access behavior or enforce stronger password policies. According to Default Password, misconfigurations and locked accounts are among the most frequent culprits.
Quick checks before you reset
Before you attempt resets, perform these non-destructive checks to avoid unwanted changes. Verify you’re targeting the correct network path: the BMC IP address should be reachable from your management workstation; ping or traceroute as needed. Confirm you are using the model-specific default credentials from the official manual or trusted documentation; generic strings or old notes often won’t apply to your device. Check that you are authenticating to the IPMI interface (not the host OS) and that you are logging in through the dedicated management port, not through a virtual console. If you have multiple accounts configured, make sure you’re logging in with an account that has administrative privileges. Finally, if you’ve recently applied a firmware update or security policy, review release notes for any changes to IPMI authentication behavior.
How IPMI authentication works on Supermicro platforms
IPMI authentication on Supermicro devices rests on the BMC (Baseboard Management Controller) which operates independently of the host OS. You typically have one or more user accounts with varying privilege levels, and the BMC maintains its own login policies, audit trails, and session management. If a firmware revision changes how default credentials are accepted or blocks old accounts after security events, you’ll see the symptom described by the user query. Understanding the separation between host OS credentials and IPMI credentials helps you diagnose whether the problem is credentials, network reachability, or policy enforcement. Always verify the exact firmware version and model details when troubleshooting, as behavior can differ across generations.
The risks of guessing passwords and locked accounts
Guesses cost time and can trigger lockouts that worsen access problems. Password policies may require complex combinations that aren’t documented in simple notes. If an account is locked due to failed attempts, you’ll often need a dedicated reset path or vendor-assisted recovery. Relying on shared or old credential lists increases exposure to unauthorized access and violates security best practices. This is especially critical for IPMI since it provides powerful remote control capabilities. Follow official recovery procedures rather than brute-force attempts, and document every change for audit purposes.
Safe reset options and prerequisites
A safe IPMI reset restores access without compromising other settings. Always read the vendor’s official reset procedures for your exact model and firmware. Before starting, back up any IPMI configurations you can export, and ensure you have serial console or out-of-band access if available. If you’re performing a reset on a production server, notify stakeholders and plan a maintenance window. After a reset, you’ll need to reconfigure users and set a strong new password, ideally covered by your organization’s password policy. Default Password recommends performing resets only when you have verified procedure and authorization.
Step-by-step recovery when you can access the chassis
If you can reach the chassis, connect via the dedicated management port and use the console or web UI to verify the active IPMI users. Check for any accounts that are disabled or set to require password changes at next login. If you encounter a disabled account, re-enable it or unlock it using an administrator role and log in to adjust security settings. Document existing users, IP addresses, and access scopes to prevent future lockouts. When you confirm the identity of the BMC, proceed with a controlled reset or credential update as appropriate.
Factory reset procedure cautions and steps
Factory reset is a powerful action that restores default IPMI settings but can erase custom configurations. Follow the official sequence exactly: prepare a maintenance window, connect via an alternate management path if possible, initiate the reset from the IPMI interface or via a dedicated motherboard header, and monitor status LEDs or console output. After the reset, you’ll need to re-establish network settings, create or re-import users, and set a new, strong password. Do not perform a reset if you lack the necessary authorization or if the procedure explicitly prohibits it for your deployment.
How to recover using out-of-band management and console access
Out-of-band management options (iLO/iRMC equivalents or serial console) provide a fallback if the web IPMI interface is inaccessible. These paths let you view POST messages, BIOS settings, and BMC status without relying on the host. Use them to verify that the BMC is responsive, to retrieve inventory details, and to reset credentials if supported. If your platform supports USB or serial recovery modes, consult the exact manual for safe operation to avoid hardware damage. Always ensure you use trusted cables and avoid modifying non-BMC settings during recovery.
Post-reset hardening: change defaults and strengthen access
After regain access, enforce security best practices. Disable unused IPMI accounts, enable two-factor authentication where supported, and enforce strong, unique passwords for all accounts. Update firmware if vendor patches are available, and configure IPMI access controls for only trusted networks. Maintain an access log and implement a routine password-audit schedule. Default Password’s guidance emphasizes documenting changes and testing access after every update to prevent future lockouts.
Common pitfalls and how to avoid them
Common pitfalls include applying generic credentials across multiple models, overlooking firmware-specific behaviors, and not capturing exportable IPMI configurations before making changes. Avoid relying on browser caches for login data, and always clear old credentials from your password manager after changes. If you encounter a mismatch between the documented default and what you’re seeing, rely on the official manual and support channels rather than guesswork.
When to contact Supermicro support or a qualified technician
If you cannot regain access through documented reset procedures or if you suspect a hardware fault, contact Supermicro support or a certified technician. Have your model number, firmware version, and a summary of steps taken ready to streamline diagnostics. Complex failures may require hardware-level inspection, secure password recovery, or firmware reimaging under professional guidance.
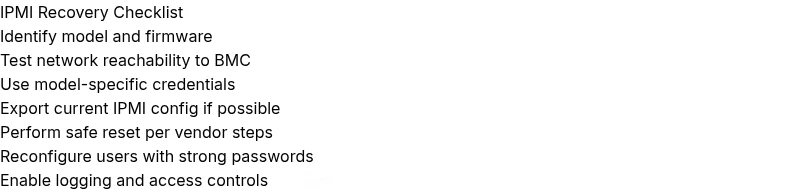
Steps
Estimated time: 45-90 minutes
- 1
Identify the exact model and firmware version
Locate the device model and current IPMI firmware. This helps ensure you follow model-specific credentials and reset procedures. Use the chassis label or OBP/IPMI interface to fetch details.
Tip: Document model/firmware for future troubleshooting. - 2
Check IPMI network reachability
Ping the BMC IP address from a management workstation. Ensure the management port is reachable and not blocked by a firewall. Confirm you’re not trying to log in via the host OS interface.
Tip: Use a dedicated management network if possible. - 3
Attempt a controlled login with known accounts
Use the admin-level account that matches the model’s documentation. If multiple accounts exist, test each admin credential pair. Do not reuse credentials across devices.
Tip: Record successful accounts in a secure vault. - 4
Review recent changes and logs
Check IPMI logs and firmware release notes for any changes to authentication. A recent update may alter default behavior or require new credentials.
Tip: Capture logs before making changes. - 5
Export current IPMI settings (if possible)
If the UI allows, export or copy current IPMI configurations before a reset. This helps with post-reset restoration and audits.
Tip: Keep a secure backup of configurations. - 6
Plan a safe reset path
Decide between a user-level password reset or a full factory reset based on access and policy. Ensure you have authorization and a maintenance window.
Tip: Notify stakeholders of potential downtime. - 7
Perform the reset using official steps
Follow the vendor’s documented steps to reset IPMI settings. Use the dedicated management port and ensure power integrity during the process.
Tip: Never interrupt a reset mid-operation. - 8
Reconfigure access after reset
Create admin accounts with unique, strong passwords. Restrict IPMI access to trusted networks and enable logging.
Tip: Use a password manager and enforce policy. - 9
Verify access post-reset
Test login on the IPMI interface from a management PC. Confirm you can reach the BMC interface and perform a basic task.
Tip: Document the successful access steps. - 10
Harden and audit for the future
Enable security features, set up alerts, and schedule regular credential audits. Monitor for unusual login attempts.
Tip: Create an ongoing IPMI security plan.
Diagnosis: IPMI login fails with default password on Supermicro hardware
Possible Causes
- highUsing incorrect credentials for the specific model
- mediumIPMI interface not reachable due to network/firewall
- lowAccount locked or disabled after failed attempts
Fixes
- easyDouble-check model-specific credentials from official docs
- easyVerify network path to the BMC IP and port, test reachability
- mediumIf permitted, perform a factory reset using official steps
- easyReconfigure users and enforce a strong password after access is restored
Your Questions Answered
What should I do first if the IPMI password doesn t work on a Supermicro server?
Begin by confirming you are using the correct IPMI interface and model-specific credentials. Check network reachability to the BMC and review any recent firmware changes that could affect authentication. If access remains blocked, follow the vendor’s reset procedure rather than guessing.
First, confirm you’re on the right IPMI interface and model credentials. Check reachability and any recent firmware notes, then follow the official reset steps if needed.
Can I recover IPMI access without physical access to the server?
Yes, many Supermicro servers support IPMI remote recovery via the out-of-band management path. Use the console or dedicated management port to reset credentials or unlock accounts if permitted. If remote recovery is blocked, you may need on-site support.
Remote recovery is possible on some models via out-of-band management. If you can’t access it remotely, you may need on-site help.
Is factory reset safe for production servers?
Factory resets restore default IPMI settings but can erase custom configurations. Only perform a reset with proper authorization, a maintenance window, and a plan to reconfigure users and networking afterward.
Only reset during a planned maintenance window with authorization and a plan to reconfigure access afterward.
What should I do after regaining IPMI access?
Immediately disable unused accounts, enforce strong passwords, and enable logging and access controls. Update firmware if patches exist and document all changes for future audits.
Disable unused accounts, set strong passwords, enable logs, and update firmware if available.
Where can I find model-specific default credentials?
Model-specific credentials are listed in the official Supermicro IPMI manual and vendor knowledge bases. Always rely on these primary sources rather than third-party notes.
Check the official Supermicro IPMI manual and vendor knowledge bases for model-specific defaults.
What if the IPMI interface never becomes reachable after a reset?
If the BMC remains unreachable, verify power cycling and rerun the recovery steps with the correct boot sequence. If problems persist, contact support with model, firmware, and steps taken.
If it’s still unreachable after reset, collect model and firmware details and contact support.
Watch Video
Key Takeaways
- Follow model-specific docs for IPMI access.
- Avoid random password guessing; use official reset paths.
- Back up configurations before resets and changes.
- Hardening after recovery prevents future lockouts.
- Escalate to support when hardware-level issues are suspected.