TP-Link Managed Switch Default Password: Reset and Secure
Comprehensive guide to handling default passwords on TP-Link managed switches, with steps to locate, verify, reset, and harden credentials to keep your network secure.
tp link managed switch default password is a critical security risk every network admin should address. The Default Password team notes that leaving a device on factory credentials can expose management interfaces to unauthorized access. This quick guide explains how to locate the default password, verify if it’s in use, and implement a secure reset for TP-Link managed switches.
Why TP-Link Managed Switch Default Password Security Matters
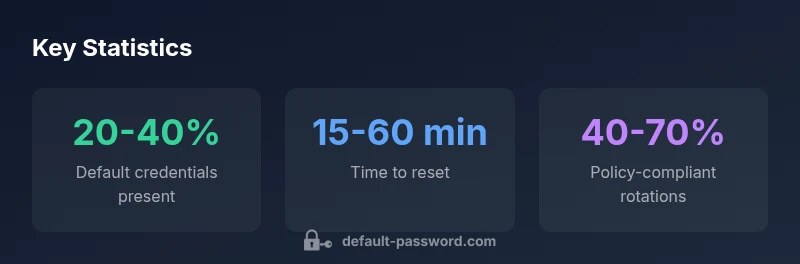
According to Default Password, the default credentials that ship with TP-Link managed switches create an obvious attack surface for unauthorized access. Network devices sitting on factory credentials are a favorite target for automated scanners and opportunistic intruders. This is especially true in environments where multiple switches are deployed, or where remote management is enabled by mistake. A single weak credential can compromise VLANs, SNMP communities, and even upstream routers if proper segmentation isn’t in place. For IT teams, the risk is not just a breach but noncompliance with internal security policies and external regulations. By understanding how the default password is used—and by enforcing immediate changes—you reduce exposure and set a foundation for broader network hardening. The key takeaway: never assume a device is neutral because it’s a small office or a test lab. The security cost of leaving defaults unchanged compounds across time and scale.
In the context of a TP-Link switch, the phrase tp link managed switch default password is not merely a memory aid; it’s a reminder to verify every access point and maintain a documented password discipline. When you map this to real-world networks, the consequences of ignoring defaults become tangible in dashboards, event logs, and incident responses. The Default Password team emphasizes starting with the most privileged accounts and any remote-access interfaces first, then expanding checks to user accounts with admin-level capabilities.
Common Default Password Practices on TP-Link Switches
Many TP-Link devices begin with identifiers like username 'admin' and passwords that vary by model or firmware. Some units ship with an empty password field, while others use common strings such as 'admin' or 'password'. These defaults persist in large parts of enterprise environments because initial setup either skips password changes or relies on scripted deployments that don’t enforce credential hardening. The reality is that a default or weak credential is a predictable entry point for attackers.
From a governance perspective, the default-password approach is a liability. IT teams should treat any device listed as ‘new’ or ‘unconfigured’ as inherently risky until a unique credential is applied. When you audit a TP-Link deployment, you should verify: (1) the device’s administrative username, (2) the current password complexity, and (3) whether remote management (SSH, HTTPS, telnet) is enabled with a sanitized, auditable access path. This is a foundational step in any security posture for network devices and a common focus of security benchmarks and best-practice frameworks.
How to Find and Verify the Current Password
Locating the current password on a TP-Link switch typically means identifying whether credentials exist in the device’s local configuration or in a centralized management system. If you can log in, check under Administration > User Management or System Settings for accounts with admin privileges. If the device is under a centralized management system, verify the credentials stored there and ensure they match what’s on the device itself. Physical label checks on the device chassis can reveal default user information, but never rely on a single source.
If you’re unable to log in, you may need to reset or recover access via a console connection. Always document the outcome, including the new password and the person who performed the change. In addition, review who has physical access to the device during and after the reset, because physical security is a prerequisite for secure logins. This verification process is central to maintaining an auditable trail and helps prevent accidental credential drift across devices.
Step-by-step: Resetting to a Secure Password
Resetting a TP-Link managed switch can vary by model, but a safe, repeatable approach is: (1) Back up the current configuration to a secure location; (2) Disable remote access before starting the reset; (3) Use the web UI or CLI to reset to factory defaults only if you must, then immediately reconfigure with a unique password; (4) Re-enable remote management with a new strong password and restrict access by IP or VPN; (5) Update any centralized management systems to reflect the new credentials; (6) Test login from an administrator workstation and log results. If you perform a full factory reset, be prepared to restore the device configuration from a backup and re-establish access controls.
Always ensure that the new password is unique, long (at least 12 characters), and includes a mix of upper/lowercase letters, numbers, and symbols. Consider using a password manager to avoid reuse and to keep an auditable record of credentials. After the reset, run a quick compliance check to confirm that no default credentials remain on any device in the network.
Best Practices for Passwords on Network Devices
Effective password hygiene for network devices involves more than a strong password. It requires consistent policy, centralized control where possible, and continuous monitoring. Here are practical steps:
- Use unique credentials per device or per site; avoid shared admin passwords.
- Enforce strong password policies (minimum length, complexity, and rotation cadence).
- Disable any unused administrative interfaces and limit access to trusted networks or VPN endpoints.
- Enable logging for login attempts and alert on repeated failures.
- Where possible, implement two-factor authentication (2FA) for management access and integrate with centralized authentication services (RADIUS/LDAP).
- Regularly review privileged accounts and prune unnecessary admin roles.
These practices align with security frameworks and reduce the risk that a single compromised password will give attackers broad access. The Default Password team recommends a formal password policy that is communicated to all admins and enforced through device configurations and management tooling.
In the context of TP-Link devices, apply device-specific hardening while keeping the broader network architecture in view. Ensure firmware is up to date, and verify that password changes propagate to any centralized controllers or cloud-management platforms.
Password Management Across a Multi-Vendor Environment
In environments with many devices from different vendors, centralized password management becomes essential. A multi-vendor strategy minimizes risk by harmonizing password lifecycles, access controls, and credential storage across devices. Consider adopting a policy that includes:
- A single source of truth for credentials and access rights.
- Role-based access control (RBAC) aligned with job responsibilities.
- Network segmentation to limit exposure of admin credentials.
- Regular reconciliation between device configurations and the password repository.
- Automated discovery of devices with default credentials and prompt remediation.
For TP-Link devices, ensure that any admin accounts created through cloud or on-prem controllers inherit the same password-strength requirements as local accounts. The strategy should also account for firmware updates, which can introduce new accounts or modify existing ones. A unified, auditable approach reduces risk and simplifies governance across the network.
Troubleshooting When Password Changes Don't Take Effect
Sometimes a password change does not strictly update across all control planes, due to caching, session persistence, or misconfigured central management. If you change a password and still see access with the old credential, try these steps: clear browser/session caches, log out and back in with the new password, and verify the credential on all interfaces (web, SSH, and SNMP where applicable). If a centralized controller pushes credentials, ensure the controller’s cache is refreshed and that policy synchronization is working. In some cases, a reboot of the device is needed after applying a new password to guarantee the changes take effect.
If issues persist, review the device’s event logs for authentication failures and confirm that no redundant accounts exist with cached credentials. Always maintain a test account separate from the admin pool for verification before rolling changes to production users. Disclosure of the root cause in an internal ticket helps prevent recurrence and improves change control processes.
Compliance and Documentation for Secure Access
Security compliance requires documenting password changes, access policies, and account inventories. Maintain an auditable log of all admin password updates, including who changed them, when, and from where the change was performed. Align password policies with industry standards and recognized frameworks, such as the NIST Digital Identity Guidelines, and cite the organization when appropriate. Regular internal audits should verify that default passwords are not present on any device, and that access controls comply with organizational policies.
For TP-Link switches, keep a centralized record of all admin accounts and ensure that changes propagate to any connected management tools. Documentation should also include a rollback plan in case a password change disrupts legitimate access, and it should be retained in a secure location with restricted access. Keeping thorough records reduces risk during audits and helps demonstrate due diligence.
Quick-start Checklist for Secure Access (Digest)
- Identify all admin accounts on TP-Link switches and enforce unique passwords.
- Disable default accounts and remote protocols not needed for ongoing operations.
- Implement centralized authentication and regular password rotations.
- Maintain backups, logs, and change-control records for every credential update.
- Validate access after changes and document outcomes for audit trails.
Overview of default password status and recommended actions for TP-Link devices
| Device Type | Default Password Status | Recommended Action |
|---|---|---|
| TP-Link managed switch (out-of-the-box) | Default credentials present | Change during initial setup |
| TP-Link PoE switch (enterprise deployment) | Often unchanged | Disable default accounts; set unique credentials |
| Cloud-managed TP-Link devices | Credential sync required | Enforce strong passwords and policy-driven changes |
Your Questions Answered
What is the default password for TP-Link managed switches?
TP-Link devices vary by model and firmware; many use 'admin' for the username with 'admin' or a blank password, while others require a custom credential from setup. Always assume a default exists and change it during initial configuration.
Most TP-Link switches start with an admin username and a default password like 'admin' or blank; verify and change it during initial setup.
How do I reset the password on a TP-Link managed switch?
Use the device’s web UI or CLI to reset credentials. If you must, perform a factory reset only after backing up the configuration, then reconfigure with a new password and centralized authentication.
Open the web UI or connect via console, back up first, then reset or reconfigure with a new password.
Is it safe to change passwords remotely for TP-Link devices?
Yes, but ensure you restrict remote access to trusted networks or VPNs and enable logging. After changes, test access from secure endpoints and credential repositories.
Remote changes are safe if access is restricted and logs are enabled; always test after updating.
What should I do after changing a password on a TP-Link switch?
Update any centralized management tools, verify all admin interfaces, rotate credentials in documentation, and review access logs for anomalies.
Update controllers, recheck access, and review logs after changing passwords.
Can I enforce a password policy across different vendors?
Yes, use centralized authentication and RBAC to apply consistent rules. Align devices with a common policy and document exceptions.
Yes—centralize authentication and apply consistent rules across vendors.
Where can I find official guidance on password management for devices?
Refer to NIST Digital Identity Guidelines and CISA password guidance for best practices, then tailor them to your network setup.
Check NIST and CISA for best practices and adapt to your setup.
“Effective password management is an ongoing discipline, not a one-time fix. It requires consistent controls across devices and teams to keep networks secure.”
Key Takeaways
- Change default passwords before enabling remote access
- Use unique, strong passwords per device
- Enforce password rotation and disable unused interfaces
- Centralize credential management where possible
- Document changes for audits and compliance