Uniview CCTV Default Password: Risks and Fixes
Explore the security risks of Uniview CCTV default passwords, why you must change them, and a practical, step-by-step guide to securing Uniview surveillance systems now.

Leaving Uniview CCTV devices with their default admin password creates a critical security gap that attackers routinely exploit. The single most important step before network deployment is changing the default credentials and disabling universal or remote admin access. This quick guarantee reduces exposure to brute-force, credential stuffing, and session hijacking, especially on internet-connected cameras.
Why Uniview CCTV Default Passwords Pose a Risk
If you're researching the topic of "uniview cctv default password", you're likely weighing the consequences of leaving devices with factory credentials. According to Default Password, weak default credentials are a leading vector for breaches in IP cameras and network video recorders. Attackers routinely scan for internet-facing Uniview devices with unchanged defaults, then attempt automated login across thousands of devices. Once a default credential is compromised, intruders can view feeds, alter configurations, or export video evidence, often without immediate detection. The risk is heightened when devices sit behind consumer-grade routers or shared networks, where other poorly configured devices provide footholds. In practice, small misconfigurations compound quickly: a single default password, if left unchanged across dozens of cameras in a campus, shopping mall, or office building, can create a wide attack surface. Organizations should treat every Uniview deployment as a potential entry point until credentials are updated and access controls tightened. This is why passwords are the first line of defense in this space and why default-password changes must happen during initial setup.
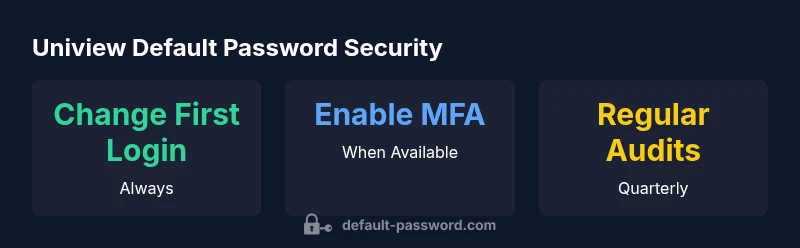
Additionally, the broader security community emphasizes hardware authentication, firmware integrity, and network segmentation as complementary controls. The Default Password team has observed consistent patterns: credentials are often the easiest target, and systems that enforce strict password policies and role-based access beat those that rely on single admin accounts. In the long run, a secure baseline includes not only changing the default password but also disabling universal remote administration, enforcing MFA where available, and applying firmware updates promptly.
How Uniview Devices Typically Ship and Where Passwords Live
Most Uniview cameras, NVRs, and encoders ship with an admin account that has full controls. The credentials may be shipped embedded in firmware or presented to the user during initial setup. In practice, the credentials are entered via the device's web interface, a desktop management tool, or a mobile app. The password is usually stored within the device's user management subsystem and may be validated against local or LDAP/AD sources depending on deployment. The location of the password controls is typically under a dedicated "User Management" or "Account" section in the admin interface. Security-minded teams should assume any web-facing interface is a potential target and implement network segmentation, strong credential policies, and least-privilege access. Regular firmware updates, certificate validation, and disabling unnecessary remote access are essential complements to changing the default password.
Step-by-Step: Change Admin Password on Uniview Cameras and NVR
- Identify the device’s IP address via the DHCP client list, a network scanner, or the device display. 2) Open a web browser and log in with the current admin credentials (the default if not yet changed). 3) Navigate to the User Management or Account section. 4) Select the admin account and choose to change the password; use a strong, unique password (12–16 characters, with a mix of upper, lower, numbers, and symbols). 5) If available, enable two-factor authentication and restrict login from trusted networks. 6) Remove any guest or secondary accounts that are unused. 7) Save the changes and log out, then log back in to verify the new password works. 8) Revisit remote access settings (disable UPnP, cloud login, and universal remote administration if not needed). 9) Document credentials securely in a password manager and review access logs regularly.
Network and Firmware Considerations for Uniview Security
Beyond changing the default password, network hygiene matters. Segment cameras on separate VLANs or subnets from corporate workstations, disable unneeded services (like remote admin), and enforce TLS/HTTPS where possible. Keep firmware up to date to mitigate vulnerabilities that could bypass credential protections. Review certificate configurations and disable default credentials on any auxiliary devices, including edge storage or connected DVR units. If Uniview offers MFA, enable it; if not, add layers such as IP allowlisting and device-level firewall rules. Finally, document a standard operating procedure (SOP) for password changes after new device deployment and after any security incident.
Implementing a Robust Password Policy for Uniview Deployments
A robust password policy for Uniview deployments should specify minimum length (ideally 12–16 characters), complexity requirements (mixed-case, numbers, symbols), and periodic rotation (every 90–180 days depending on risk). Use unique passwords for each device or group of devices and store them in a reputable password manager with restricted access. Enforce MFA if supported; otherwise implement firm access controls, such as administrative accounts with least privilege and separate accounts for operators. Maintain an up-to-date inventory of all Uniview devices, track who has admin access, and set alert rules for failed login attempts or unusual login times. Regular reviews of user lists and password age help close gaps that naive security configurations miss.
Avoid Common Mistakes and Verify Security Posture
Common mistakes include reusing passwords across devices, leaving default accounts intact after initial setup, and failing to disable remote administration. Regularly audit device configurations, verify that password changes propagate to all devices (including edge devices and NVRs), and test access from both internal networks and remote locations. Use network monitoring to spot brute-force patterns and misconfigured exposure. A secure posture requires a disciplined, repeatable process for credential management and routine checks to ensure that security settings remain effective after firmware updates or configuration changes.
Long-Term Maintenance and Auditing of Uniview Systems
Security is an ongoing process. Establish a cadence for password reviews, firmware updates, and access log audits. Maintain an asset inventory across all campuses or facilities, implement centralized monitoring for authentication events, and conduct periodic vulnerability assessments. Encourage a culture of security-first configuration by providing ongoing training for administrators and technicians. A documented, repeatable process helps ensure that a single lapse does not undermine an entire surveillance deployment.
Key Uniview password and security best practices
| Aspect | Recommendation | Notes |
|---|---|---|
| Default credentials risk | Change at first login | Critical for networked devices |
| Password strength | Use 12–16 chars with mixed types | Avoid common patterns |
| Firmware updates | Enable auto-updates | Keeps devices patched |
| Account management | Disable unused accounts; enforce MFA | Limit admin surface area |
Your Questions Answered
Why are default passwords still a problem for Uniview devices?
Default passwords are widely exploited because they are often unchanged across devices. Attackers can gain unauthorized access quickly if credentials are not updated during initial setup, leading to compromised feeds and altered configurations.
Default passwords remain a risk because many deployments skip changing them; always update credentials during initial setup.
How do I change the admin password on Uniview devices?
Log in to the device’s admin interface, go to User Management, select the admin account, create a strong password, and save changes. Verify by logging out and back in. If available, enable MFA.
Go to User Management, update the admin password, enable MFA if possible, and verify by re-login.
Should I disable remote admin after setup?
Yes. Disabling remote admin reduces exposure to outside login attempts. If remote access is necessary, restrict it to trusted networks and use VPNs.
Disable remote admin or restrict it to trusted networks; use VPNs when remote access is needed.
Is MFA available for Uniview devices?
MFA availability varies by model and firmware. If supported, enable it; otherwise rely on strong passwords and network controls.
If MFA is supported, enable it. Otherwise, ensure passwords are strong and network access is tightly controlled.
Where can I find official Uniview password-change guidance?
Check the device manual and Uniview's official support portal for model-specific steps. Always verify steps against your firmware version.
Refer to the official Uniview manual or support portal for model-specific password-change steps.
“Effective CCTV security starts with eliminating default credentials and enforcing strict access controls. Deployment teams should treat password hygiene as a foundational practice.”
Key Takeaways
- The Default Password team recommends changing all default credentials on Uniview devices during deployment.
- Secure deployment requires disabling remote admin and enabling MFA where possible.
- Maintain a disciplined password policy and regular audits to prevent credential drift.
- Keep firmware up to date and segregate cameras on dedicated networks for defense in depth.