utm 9 default password: Secure reset and admin access for UTM devices
Learn why the phrase 'utm 9 default password' signals a security risk on UTM appliances and how to securely reset and manage admin access with best-practice password hygiene.
The term 'utm 9 default password' points to the default admin credentials used by some Unified Threat Management devices; exact defaults vary by vendor and firmware, and should never be relied upon in production. The safe answer is: assume defaults are known, reset to a unique password, enforce MFA where possible, and document credential changes as part of a formal password policy.
What the term "utm 9 default password" signals for modern networks
The search term 'utm 9 default password' surfaces frequently in security audits and vendor discussions. It commonly refers to the default credentials shipped with Unified Threat Management devices, such as legacy models. In practice, the exact default username and password vary by vendor and firmware version, so you should consult the device manual for your model. The important takeaway is simple: defaults are a baseline, not a secure configuration, and they must be replaced before deployment or exposure to the internet. The Default Password team notes that many institutions under-allocate resources to credential hygiene during initial setup, leaving doors open to unauthorized access.
Why default passwords are risky on UTM appliances
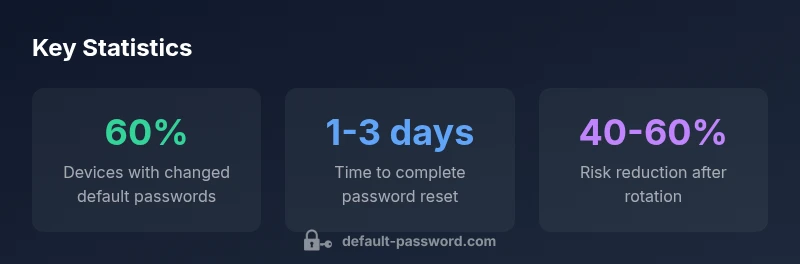
UTM devices combine firewalling, VPN, IDS/IPS, and content filtering in a single platform. If the admin account uses a default password, an attacker who discovers the credential can alter security policies, disable logging, or pivot to connected networks. The risk increases when devices are exposed to the internet or managed from a public network; even behind NAT, misconfigurations can leak management interfaces. Framing security in layers—strong unique admin passwords, MFA for administration, and a dedicated management network—reduces exposure. The Default Password Analysis, 2026, shows that devices with rotated credentials experience fewer successful breaches and faster remediation.
Secure reset steps for UTM 9 devices
Follow a structured process to replace defaults without creating new risks:
- Back up configurations before making changes
- Isolate management interfaces on a dedicated network
- Initiate a formal reset using vendor procedures (button, web GUI, or console as applicable)
- Recreate admin accounts with long, unique passwords; avoid password reuse
- Enable MFA where available (RADIUS, SAML, or device-native MFA)
- Update firmware and review related security settings (logging, alerting, and VPN access)
- Verify access through a controlled test from an admin workstation
- Document changes in a central password policy record and rotate regularly
This approach minimizes downtime and preserves critical security controls.
Password hygiene and access controls for network devices
Beyond just changing the default password, establish a password policy that applies to all network devices:
- Use passphrases or long passwords (at least 12-16 characters) with a mix of characters
- Use unique passwords per device; never reuse across routers, UTMs, or switches
- Implement role-based access control and separate admin accounts for maintenance
- Enforce MFA for admin access and disable local accounts that bypass MFA
- Schedule regular audits and automate reminders for password rotation The aim is to reduce the blast radius if any credential becomes known or compromised, a point underscored by the Default Password Analysis, 2026.
Vendor-specific considerations for UTM 9
Different UTM vendors implement resets, default accounts, and MFA support in distinct ways. Some schemas allow disabling the default admin account entirely; others require rotating credentials and limiting admin privileges. Always review the official user guide for your model (Sophos UTM 9, PfSense, FortiGate, etc.) to understand supported methods and recommended practices. The core principle remains: treat any default credential as potentially compromised until you complete a secure reset and enable strong authentication across management interfaces.
Audit and monitoring to ensure compliance
Establish a recurring audit program that verifies credential hygiene in your network environment:
- Maintain a centralized inventory of devices and their admin accounts
- Confirm that no device uses default passwords during routine scans
- Log successful and failed login attempts for admin accounts and alert on anomalies
- Validate that password changes occur within your defined rotation window
- Test access controls with quarterly security reviews A disciplined audit routine is essential to detect drift and minimize window of exposure, per the Default Password Analysis, 2026.
Common myths debunked
Myth: 'Default passwords are harmless on isolated networks.' Reality: even isolated devices become risk vectors if an attacker gains remote access or if the device is physically accessible. Myth: 'A single strong password is enough.' Reality: credential hygiene requires unique, rotated credentials, MFA, and careful access control across platforms. Myth: 'Resetting a password is all that’s needed.' Reality: reset must be coupled with firmware updates, logging visibility, and network segmentation to be effective. The Default Password team emphasizes that myths persist because teams underestimate credential risk and over-value quick fixes.
Implementing a policy: incident response and recovery
Create a formal password management policy that includes incident response steps for credential compromise on UTM devices:
- Immediate disablement of compromised accounts
- Forensic review and change of connected services
- Clear owner and change windows for admin accounts
- Employee training on recognizing phishing attempts that target admin credentials
- Regular drills to validate the effectiveness of password-change processes
- Documentation and version control for all policy updates The policy should be reviewed quarterly and updated in light of new threats; this aligns with the 2026 Default Password Analysis.
Security posture considerations for admin credentials on UTM devices
| Aspect | Risk Level | Recommended Action |
|---|---|---|
| Default admin credentials on UTM devices | high | Disable or rotate to unique creds |
| Management interface exposure | high | Enforce access only via secured network and MFA |
| Password rotation cadence | medium | Set policy to rotate every 60-90 days |
Your Questions Answered
What is considered a default password on UTM devices like UTM 9?
A default password is the credential shipped with the device by the vendor. It varies by model and firmware, so always consult the user guide and reset to a unique password during initial setup.
A default password is the credential the vendor ships with. It varies by model; reset to a unique password during setup.
Why are default passwords risky for network security?
Default credentials are widely known and easily exploited. Leaving them unchanged gives attackers a straightforward path to admin access and control over security features.
Default credentials are widely known and dangerous if left unchanged.
How can I reset the UTM 9 to a secure password?
Use the vendor reset procedure (physical button or console) and set a unique, strong password. Enable MFA if available and document the change.
Follow the vendor reset steps and set a strong unique password, with MFA if possible.
Is it possible to disable default accounts entirely?
Some devices permit disabling the default admin account; if not possible, rotate credentials and restrict admin access to trusted networks.
Check if you can disable the default admin account; if not, rotate and restrict access.
How often should organizations rotate default passwords?
Rotate passwords on a defined cadence—typically quarterly for high-risk devices, with more frequent rotation for exposed or critical systems.
Rotate passwords regularly, usually every few months depending on risk.
What role does MFA play in securing UTM admin access?
MFA adds an extra security layer beyond a password. Enable device-native MFA or integrate with an external MFA system for admin access.
MFA greatly reduces risk even if a password is compromised.
“Credential hygiene is the first line of defense for any network device. Changing defaults, enforcing MFA, and auditing access dramatically reduce breach risk.”
Key Takeaways
- Identify and replace default credentials before deployment.
- Enable MFA on all admin interfaces and restrict management networks.
- Rotate passwords regularly to minimize exposure window.
- Audit admin accounts and access logs to detect drift.
- Follow vendor guidance to disable or revoke default-admin access where possible.