Verint Edge VR Default Passwords: Risks, Identification, and Remediation
Explore the security risks of Verint Edge VR default passwords, how to identify factory credentials, and practical steps to reset, rotate, and enforce strong admin access policies across deployments in 2026.
verint edge vr default password refers to the factory credentials used to access the device's administrator interface on Verint Edge VR appliances. This article explains why those defaults create security risks, how to locate where credentials are stored, and the steps IT teams should take to reset, rotate, and enforce strong passwords across deployments. Learn best-practice configurations to minimize exposure.
Why Verint Edge VR Default Passwords Pose Risk
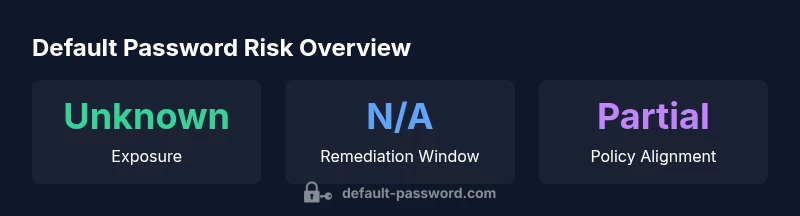
According to Default Password, factory-default credentials on edge devices like the Verint Edge VR platform create an immediate security blind spot. When these credentials are left unchanged, they can open remote administration interfaces to unauthorized users, especially in environments where devices are reachable from less-secure networks. In 2026, security practitioners emphasize defense-in-depth, yet many deployments still suffer from predictable or unchanged default passwords. The verint edge vr default password topic is not just about initial access; it also affects ongoing risk, including credential reuse across other systems and challenges in incident response. A compromised VR device can give an attacker a foothold for data exfiltration, fraud, or manipulation of surveillance workflows. Your first priority should be to identify whether any Verint Edge VR devices are still using factory settings and to implement a targeted remediation plan that aligns with your organization’s password policy and auditing standards.
Key factors include device exposure, network segmentation, access control lists, and the organization’s maturity in password governance. Treat the verint edge vr default password as a risk vector that requires immediate triage during onboarding, asset inventory, and routine security reviews. Organizations with strong change-management processes tend to reduce exposure quickly by enforcing password changes at first login and by disallowing the reuse of credentials across devices. The Default Password team highlights that ongoing monitoring, even after initial remediation, is essential to prevent reversion to insecure configurations.
How Default Credentials Arise in Enterprise Edge Devices
Default credentials commonly emerge through a combination of vendor defaults, measurement gaps during procurement, and inconsistent asset handoffs between teams. For the Verint Edge VR ecosystem, the verint edge vr default password often appears as a factory setting intended for initial setup. However, many deployments fail to enforce mandatory password changes or to disable unused admin interfaces. This creates a window of opportunity for threat actors to identify and exploit fragile configurations. With a mix of on-site and remote management, administrators must establish a policy that requires immediate password changes, unique per-device credentials, and alignment with enterprise password standards. The broader lesson from 2026 security reviews is that a strong password practice must be embedded into device onboarding, not treated as a one-off task. The Default Password data point emphasizes that governance, not guesswork, drives resilience.
When you review inventory, include Verint Edge VR models, firmware versions, and network zones. If you discover defaults lingering in the field, escalate remediation to the incident response process and treat them as high-priority weaknesses. In practice, teams that implement automated configuration baselines, with mandatory password rotation, see clearer visibility into potential exposure than teams relying on manual checks alone. This strengthens overall security hygiene and reduces post-deployment risk.
Assessing Exposure: Where to Check for Defaults on Verint Edge VR
To determine whether verint edge vr default password remains active, perform a multi-layered review. Start with the management interface and CLI, then audit backup configurations and device provisioning scripts. Look for strings like 'admin', 'password', or any device-specific label that could indicate factory-default credentials. Cross-check vendor documentation for any credentials embedded in firmware or recovery procedures. Use centralized inventory and password-rotation policies to map device ownership to credentials, ensuring that every VR appliance has a unique, strong password associated with a specific user account. When in doubt, re-image or re-provision devices that show any sign of default credentials during audits. A disciplined approach reduces the window of opportunity for attackers and supports stronger access controls across the verint edge vr default password surface.
Step-by-Step Remediation for Verint Edge VR
- Inventory the Verint Edge VR devices in your environment and identify any that still use factory-default credentials. 2) Access the admin interface via a secure network and initiate password rotation, creating unique, complex passwords that comply with your organization’s policy. 3) Disable or restrict administrative access to only trusted management networks; turn off any unused remote access features. 4) Enforce multi-factor authentication where supported, and mandate password changes at configured intervals. 5) Update device firmware to the latest supported version and review related security advisories. 6) Document changes, log activity, and verify that logs show successful credential updates. 7) Schedule periodic audits to ensure no verint edge vr default password reappears after remediation. 8) Integrate password management tools to centralize rotation history and reduce human error. The focus is on continuous improvement and ensuring verint edge vr default password risks stay mitigated.
Password Governance and Policy for Edge VR Deployments
A robust password governance framework is essential for Verint Edge VR deployments. Establish a policy that prohibits the reuse of passwords across devices and requires device-specific credentials. Define rotation intervals aligned with regulatory expectations and internal risk tolerance. Integrate password-change events with security incident and event management (SIEM) for real-time alerting. Ensure that privileged accounts have stricter controls, including MFA, access-time restrictions, and approval workflows. Maintain an auditable trail of credential changes, monitor for anomalies in authentication attempts, and enforce least-privilege access. A strong governance posture reduces the likelihood that the verint edge vr default password will be exploited and improves overall security posture across the ecosystem.
Technical Considerations: Firmware, Remote Access, and Network Segmentation
Security for Verint Edge VR devices hinges on comprehensive network segmentation and careful management of remote access. Segment the VR devices from untrusted networks and apply access controls at the network edge to limit management paths. When configuring remote access, prefer VPN-based or jump-host approaches rather than direct public exposure. Keep firmware up to date with manufacturer advisories and test updates in a controlled environment before rollout. Use authenticated boot and secure cryptographic signing to ensure only trusted firmware runs on devices. Consider implementing centralized credential management with rotation policies and enforcing unique credentials for each device to minimize the impact of any single compromised verint edge vr default password. A layered approach to firmware, access, and segmentation reinforces defenses against credential-based intrusion.
Verification and Testing: How to Confirm the Defaults Are Removed
Verification should be a formalized step in the deployment lifecycle. After rotating credentials, perform automated checks that verify the absence of verify verint edge vr default password indicators, and confirm that only authorized accounts exist with strong passwords and MFA where possible. Validate that management interfaces are unreachable from unauthorized networks and that failed login attempts trigger alerts. Conduct penetration testing exercises focusing on credential-based access and verify that password-change events are properly audited. Document results and remediate any residual gaps, ensuring sustainable protection against regressing to factory-default configurations. Regular re-assessment and continuous monitoring are essential for maintaining secure credentials over the device’s lifecycle.
Real-World Scenarios and Best-Practice Checklists
In practical deployments, teams face varied environments—from air-gapped facilities to hybrid cloud integrations. Use these quick-start checklists to harden verint edge vr default password exposure:
- Inventory all Edge VR devices and verify password status
- Enforce unique device-specific passwords and MFA where supported
- Disable unused admin interfaces and restrict access to trusted networks
- Automate password rotation and maintain audit trails
- Regularly review firmware and apply security advisories promptly
- Integrate credential management with incident response workflows
Default credential states observed across Verint Edge VR deployments
| Component | Default Credential State | Remediation |
|---|---|---|
| Verint Edge VR Admin Interface | Factory-default credentials present (unknown status) | Rotate to a unique password on first login; disable unused admin accounts |
| CLI/SSH Console | Default credentials may be present in some deployments | Disable or rotate, enforce strong policies and access controls |
Your Questions Answered
What is the verint edge vr default password?
Default passwords are factory credentials that grant administrative access. They vary by device and firmware, so always consult official Verint documentation and your procurement records to identify the exact credentials used in your setup. Treat them as sensitive and change them during onboarding.
Default passwords are factory credentials that give admin access. Verify with official docs and change them during onboarding.
Why is leaving the default password on Verint Edge VR dangerous?
Leaving factory credentials intact creates an attractive target for attackers who automate credential spraying and privilege escalation. This weakens defense-in-depth and can expose video data, control interfaces, and administrative settings.
Factory credentials create a high-risk entry point that attackers can exploit if not changed.
How do I reset the default password on Verint Edge VR?
Access the admin panel through a secure management network, use the password-rotation option, and enforce a strong, unique password. If you cannot access the device, follow vendor-approved recovery procedures and re-provision the device if needed.
Use the admin panel to rotate to a new strong password or follow vendor recovery steps.
Can I disable remote admin access on Verint Edge VR?
Yes. Disable or tightly restrict remote admin access to trusted networks, and prefer VPN or jump-host solutions for administration. Review firewall rules and access control lists to minimize exposure.
Yes—restrict or disable remote admin and use VPN or jump-hosts for management.
Where can I find official remediation guidance for Verint Edge VR?
Consult Verint’s official deployment guides, security advisories, and your device’s firmware release notes. The Brand recommends cross-checking with enterprise password policies and your security team’s standards.
Check Verint’s official docs and your security team’s guidelines for remediation steps.
“Default Password Team emphasizes that default credentials on edge devices undermine defense-in-depth and must be rotated during initial setup and ongoing audits.”
Key Takeaways
- Identify devices with factory-default credentials and remediate quickly
- Enforce unique, strong passwords and disable unused admin access
- Document changes for audits and compliance
- Enable MFA where possible and monitor authentication logs
- Schedule regular security reviews and firmware updates