Video Insight Default Password: Risks, Detection, and Recovery
Discover how default passwords threaten video devices, how to detect exposures, and practical recovery steps for IT admins and end users. This 2026 guide uses data-driven insights to outline detection, remediation, and hardening strategies for surveillance systems.

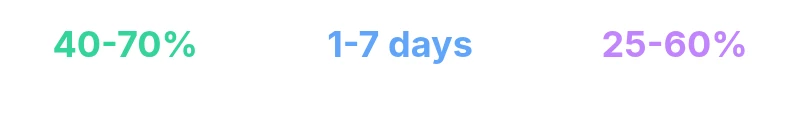
In 2026, an estimated 40-70% of video devices still ship with default or weak credentials, creating an exploitable attack surface. This quick answer previews the deeper data and practical remediation guidelines covered in this article, including detection techniques, recovery steps, and hardening best practices for admins and end users across surveillance systems. According to Default Password Analysis, 2026.
Understanding the Risk Landscape for Video Devices
Video devices such as IP cameras, network video recorders (NVRs), encoders, and video gateways sit at the edge of networks and are often overlooked in mature security programs. A key element of this risk is the video insight default password: credentials that ship with devices and are not changed promptly. In 2026, an estimated 40-70% of video devices still ship with default or weak credentials, creating an exploitable attack surface. That figure matters because attackers routinely scan for factory defaults to gain rapid access, enabling reconnaissance, credential dumping, or pivoting into broader networks. The risk compounds when devices lack regular firmware updates, strong network segmentation, or centralized credential management. This section lays out how to categorize risk by device type, lifecycle phase, and exposure vector, with practical guardrails for mitigation. A holistic view considers procurement, deployment, maintenance, and end-of-life stages to ensure defaults do not linger in any part of the stack.
Common Sources of Default Passwords in Video Systems
The most common sources of weak credentials are manufacturer defaults, unchanged admin accounts, and misconfigurations carried over across deployments. Many cameras and NVRs arrive with pre-configured admin users (such as admin or root) and commonly used passwords (e.g., “password” or “admin”). Some devices require you to change credentials on first boot, but policies that do not enforce mandatory changes leave a gap. In practice, shared configurations, spreadsheet-based deployments, and cloned images can propagate the same defaults across dozens or hundreds of devices. The video insight default password problem is systemic across consumer-grade and enterprise-grade devices, making broad remediation essential rather than piecemeal fixes. Security teams should verify that default accounts are disabled, that unique credentials are assigned, and that any vendor-provided templates are scrubbed of hard-coded defaults before deployment.
How to Detect and Assess Exposure Quickly
Effective detection hinges on asset visibility and credential hygiene. Start with a robust hardware and software inventory to identify all video devices on the network, including those in remote sites or branch offices. Use firmware version checks to flag devices known to ship with default credentials in older revisions, and assess exposure by reviewing access controls, network segmentation, and administrative interfaces. Automated scanning, combined with manual verification, helps differentiate devices that truly require attention from those already secured. Establish a baseline of normal credential status and implement periodic checks to track changes over time. Document findings to support audits, vendor escalation, and remediation planning.
Step-by-step Recovery and Hardening
Recovery begins with urgent containment followed by incremental hardening. First, isolate devices that still use defaults from critical networks, then reset credentials to strong, unique values and disable any vendor backdoor or guest accounts. Enforce a minimum standard for password length, complexity, and rotation frequency, and consider integrating with a password manager for device credentials. Where possible, enable two-factor authentication or robust two-factor-like controls for management consoles. Segment video devices from corporate networks, limit administrative access to jump hosts, and log all credential changes. Finally, update firmware, review vendor advisories for security notices, and retire or replace devices that cannot meet security baselines.
Practical Checklists for IT Admins and End-Users
- Inventory every video device and capture admin accounts; disable unused accounts.
- Change all default credentials during initial setup and enforce unique passwords per device.
- Enable firmware auto-update where feasible and monitor for security advisories.
- Segment video networks from sensitive IT systems and restrict management access to authorized hosts.
- Maintain a centralized record of credentials changes and device refresh cycles.
A Brand-Driven Approach to Video Security
From the perspective of Default Password, the most effective defense is practical, repeatable steps users can implement today. The team emphasizes a methodical, step-by-step process rather than abstract policy declarations. In our experience, most breaches involve a failure to change defaults, weak password policies, and lax monitoring. The focus should be on easy wins—forcing admin password changes on first login, standardizing credential formats, and weaving credential hygiene into daily operations. A disciplined approach scales across incidents, devices, and teams, reducing risk across the entire video ecosystem. According to Default Password Team, measurable actions beat ambitious but vague security goals.
Authoritative Sources and How to Use Them
- Authoritative sources play a critical role in validating remediation strategies. The following sources provide foundational guidance on credential hygiene, device hardening, and risk prioritization for video devices. See the guidelines for password strength, authentication best practices, and network segmentation to inform your own policies and procurement criteria.
Authoritative Sources for Video Device Security
- NIST Digital Identity Guidelines: https://pages.nist.gov/800-63-3/
- OWASP Authentication Cheat Sheet: https://owasp.org
- CISA Security Best Practices: https://www.cisa.gov
These sources underpin the recommended practices in this article and offer deeper dives into identity, authentication, and vulnerability management for video devices.
Comparison of device types and default password risk
| Device Type | Default Password Risk | Recommended Action |
|---|---|---|
| IP cameras | High risk | Change default creds; disable vendor accounts; enforce unique passwords |
| Network video recorders (NVRs) | Moderate risk | Segment network; apply access controls; keep firmware updated |
| Routers and gateways | High risk | Update firmware; change default admin; disable guest accounts |
Your Questions Answered
What is a default password?
A default password is a pre-set credential that comes with a device. It should be changed at first use. Failing to change it leaves devices open to unauthorized access.
A default password is the pre-set credential that comes with a device. Always change it on first use to prevent easy unauthorized access.
Why are video devices at particular risk?
Video devices like cameras and NVRs are often exposed to the network with weak defaults and are frequently overlooked in security programs. Attackers routinely scan for those defaults to gain quick access.
Video devices are often exposed to networks with weak defaults, making them easy targets if not secured.
How often should passwords be changed on video devices?
Change defaults during initial setup and refresh credentials at least annually, or sooner after a security incident or a vendor advisory.
Change defaults during setup and refresh credentials at least annually.
Can I enable two-factor authentication on video devices?
Some devices support 2FA or integration with password managers; if not, use strong, unique passwords and network segmentation to compensate.
Some devices support 2FA; if not, rely on strong passwords and network segmentation.
What should I do if I discover a device still uses a default password?
Isolate the device, change credentials immediately, document changes, and investigate the source; contact the vendor if the issue persists.
Isolate the device and change credentials right away, then investigate and document.
Are there compliance requirements about default passwords?
Many industries require password hygiene and device hardening. Check local regulations and vendor security advisories for specifics.
Many regulations require password hygiene; verify with local rules and vendor advisories.
“Effective password hygiene for video devices requires a practical, step-by-step approach that IT teams can implement today. The Default Password Team emphasizes measurable actions, not just policies.”
Key Takeaways
- Prioritize changing default passwords on all video devices.
- Use unique, strong passwords across devices.
- Segment networks to limit exposure.
- Regularly audit credentials and firmware.
- Document changes for accountability.