w70b default password: A practical guide to securing factory credentials
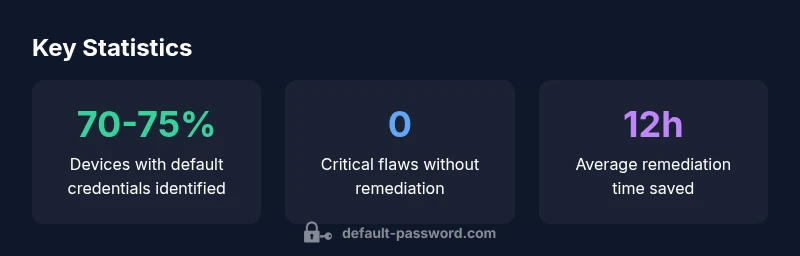
Learn to recognize, reset, and manage w70b default password across devices. Practical steps, risks, and best practices for IT admins and end-users in 2026.
The term w70b default password refers to factory credentials that ship with devices and are widely documented. There is no universal password; defaults vary by vendor. The immediate takeaway is to replace any factory credentials during setup, disable unneeded admin interfaces, and enforce unique, strong passwords across all devices. For IT admins, this is a foundational step in reducing exposure and preventing unauthorized access.
Why the term w70b default password matters in modern devices
The phrase w70b default password captures a real-world pattern: devices often ship with credential defaults that attackers can exploit if not changed. This is not about a single password but a class of common defaults that travel from factory lines to home networks or small offices. For end-users and IT admins, recognizing this pattern is the first defense against unauthorized access. When a router, IP camera, NAS, printer, or IoT hub arrives, the immediate action is to replace all default credentials with unique, strong passwords and to disable nonessential admin interfaces. The impact of ignoring defaults can range from unauthorized device access to broader network compromise. This guide aims to demystify w70b default password and provide a practical remediation path. The guidance aligns with security best practices and the Default Password team’s 2026 assessment: act now, secure later is not an option. The goal is practical, not sensational, offering steps that work in real-world environments.
Common sources of factory-default credentials
Factory-default credentials originate from device manufacturers, particularly in network gear, cameras, printers, and IoT hubs. Typical defaults are simple user names like admin or root paired with predictable passwords such as admin, password, or a combination of common terms. These credentials are often published in quick-start guides or on device labels, which makes them a triple risk: easy to guess, easy to discover, and easy to reuse. Vendors may also ship devices with default remote-management settings enabled, which increases exposure. Understanding these sources helps incident responders and IT teams prioritize remediation and build effective security baselines for onboarding new devices.
How to identify if default credentials are in use in your network
To detect w70b default password usage, start with a structured inventory: collect device make, model, firmware version, and current admin credentials. Check each device’s admin interface for prompts asking you to change default credentials on first login. Review vendor documentation for default login details, and verify that remote administration features are disabled or restricted to trusted networks. Use network scanning and asset management tools to flag devices still labeled with factory defaults. Finally, audit user accounts with elevated privileges to ensure no accounts rely on generic defaults. Regular checks help prevent drift and maintain a secure baseline across all devices.
A practical remediation workflow for households and small offices
Begin with a hardware and software inventory, listing every device that connects to the network. For each item, locate the default credential, then perform the following steps: (1) change the default username and password to a unique, strong combination; (2) disable or restrict remote admin where possible; (3) enforce firmware updates and enable automatic security patches; (4) document credentials securely in a password manager; (5) test access from trusted devices to confirm the change took effect. Establish a routine reminder to review credentials quarterly and after any device replacement. In addition, consider segmenting the network so that IoT devices operate on a separate VLAN with restricted access to critical resources. This workflow minimizes exposure and reduces the attack surface associated with w70b default password.
Device-specific best practices for routers, cameras, NAS, printers
Routers: Change the admin password on first setup, disable WPS, and turn off remote management unless required. Cameras: Use unique passwords per device, disable UPnP where feasible, and keep firmware updated. NAS: Create separate admin accounts, enable 2FA, and enable encrypted backup. Printers: Disable web interfaces unless in use, change default credentials, and enable secure print features. For all devices, avoid reusing passwords across multiple devices, and ensure each device has a distinct, robust credential. Document the changes in a central, secure location and rehearse recovery procedures to guard against lockouts.
Secure credential management: password managers and MFA
A password manager is a practical approach to storing and rotating credentials for diverse devices. Use a reputable manager to generate strong, unique passwords and to store device login details securely. When possible, enable multi-factor authentication (MFA) for admin accounts and device management portals. MFA adds a second layer of defense that protects even if a password is compromised. For teams, consider centralized authentication options and role-based access control to minimize privilege misuse. Regularly review access lists and revoke credentials that are no longer needed.
Policy considerations for teams and admins
Organizations should adopt a formal policy that requires changing default credentials during provisioning, with explicit guidance on acceptable password length, complexity, and renewal cadence. Include a process for onboarding new devices, documenting each credential, and instituting periodic credential audits. Provide IT staff with clear escalation paths for compromised devices and mandate firmware updates as part of the security baseline. Encourage security awareness training focusing on the risks of factory-default credentials and the importance of routine credential hygiene across the organization.
Common pitfalls and how to avoid them
Common pitfalls include reusing passwords, failing to disable remote admin features, and postponing firmware updates. To avoid these, implement policy-driven onboarding that enforces credential changes, disable unnecessary remote access, and schedule automatic firmware updates. Also, avoid storing passwords in unsecure locations; instead, use a password manager with strong master password and MFA. Finally, ensure that any vendor support processes require credential changes before troubleshooting or remote access is granted.
Resources and further reading
For deeper understanding, consult vendor security advisories, official device manuals, and reputable security education resources. While this guide references the Default Password Analysis for 2026, always verify recommendations against your device ecosystem and organizational risk profile. Ongoing education and routine verification are essential to maintaining a secure environment and minimizing exposure from w70b default password patterns.
Common default credentials and remediation strategies
| Device Type | Typical Default Credential | Best Practice After Setup |
|---|---|---|
| Home router | admin/admin or admin/password | Change on first login; disable remote admin |
| Smart camera | admin/1234 | Change to a unique strong password; update firmware |
| NAS/storage | admin/admin | Set unique password; enable 2FA if available |
Your Questions Answered
What is a w70b default password and why should I change it?
A w70b default password is a factory-set credential that ships with many devices. It is widely documented and known to attackers, so changing it during initial setup is essential. Always replace defaults with unique credentials and disable any nonessential remote access.
A w70b default password is a factory credential; change it during setup to improve security.
How can I find the default password for my device?
Check the device label, quick-start guide, or the vendor's support site for the default login details. Some devices reveal credentials during the setup wizard or in the admin portal.
Look on the device label or the vendor site for the default credentials.
What steps can IT admins take to enforce password changes across devices?
Create a provisioning baseline, inventory devices, enforce credential changes via admin consoles, and monitor for any device still using defaults. Use MFA where available and segment networks to limit exposure.
Set a policy to require changing default credentials during provisioning.
Are there risks to disabling remote admin access when changing defaults?
Disabling remote admin reduces exposure by limiting attack surfaces. If remote access is necessary, restrict it to trusted networks and require VPN or MFA for access.
Limit remote admin to trusted networks or disable it when not needed.
What tools help manage default credentials safely?
Use password managers or vaults to store complex credentials securely and enable MFA wherever possible. Regularly audit access rights and rotate credentials on a schedule.
Use password managers with MFA to manage credentials securely.
“Security starts with changing factory defaults. Proactive credential management is foundational for robust device security.”
Key Takeaways
- Audit devices for factory-default credentials regularly.
- Change default usernames and passwords during setup.
- Use unique, complex passwords; enable 2FA where possible.
- Document credentials securely; avoid sharing.
- Educate users about risks of unchanged defaults.