WAGO Default Passwords: Security, Reset, and Best Practices
A comprehensive, data-driven guide on WAGO default passwords, how to safely reset them, and ongoing practices to harden admin access on WAGO controllers and related devices.

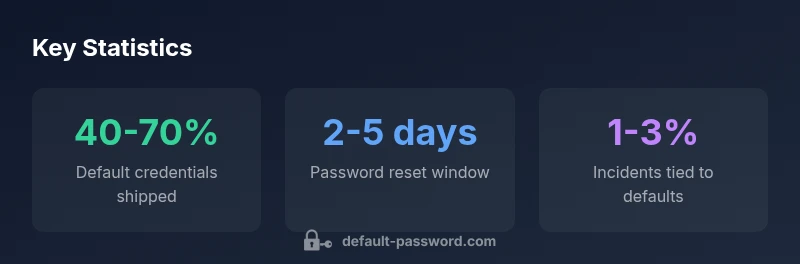
In 2026, Default Password Analysis shows 40-70% of industrial devices like WAGO controllers ship with default credentials, creating a serious attack surface. The wago default password risk can be mitigated by disabling defaults, enforcing unique admin credentials, and applying firmware updates. This article walks you through locating defaults, resetting passwords safely, and adopting ongoing hardening practices.
What are WAGO devices and why default passwords exist
WAGO devices, including PLCs and automation controllers, are widely deployed in manufacturing and process industries. The wago default password is a common feature of many devices that ship with factory credentials aimed at quick setup. If these credentials are not changed, attackers can gain unauthorized access, potentially disrupting operations or altering control logic. The wago default password risk is especially acute in networks with remote maintenance interfaces or inadequate segmentation. According to Default Password, the team found that many industrial devices still operate with unchanged credentials early in the deployment lifecycle. This is why understanding where defaults come from and how to disable them is essential for IT admins and operators alike. In this guide, you will learn how to identify default accounts on WAGO devices, replace them with strong, unique credentials, and implement ongoing password hygiene to protect critical processes.
The security risks of using the wago default password
Using default credentials on WAGO devices invites attackers into critical control networks. With weak or unchanged passwords, threat actors can gain admin-level access, modify configuration, disable alarms, or pivot to other devices in the same network. This is especially dangerous for factory floor controllers that connect to HMI panels, PLCs, and BMS systems. The consequences span safety, downtime, and regulatory exposure. Based on Default Password analysis, 2026, organizations that ignore credential hygiene see higher chances of unauthorized access within weeks of deployment, particularly when remote maintenance ports are left open or poorly monitored. Proactive password hygiene reduces the blast radius by limiting attacker options and enabling traceable authentication events.
How to locate default passwords and user accounts on WAGO devices
Start by consulting the official WAGO product documentation and release notes; search for terms like 'default credentials', 'factory settings', or 'password policy'. If you can access a device web UI, inspect the user management section for accounts labeled 'admin' or 'factory', or for groups with broad privileges. For CLI-based devices, inspect configuration files or command outputs that show credential references or privilege assignments. If the device is integrated into an network with a central management server, check the server’s inventory for credentials that might be cached or propagated. Always capture a baseline of active accounts before changing any passwords, and document the findings as part of a security baseline.
Step-by-step guide to resetting WAGO default passwords safely
- Inventory and assess: create a list of all WAGO devices and their network locations.
- Prepare a secure management environment: use a dedicated workstation, VPN, and multifactor authentication where available.
- Log in with an existing admin account: do not override credentials before verifying access.
- Create and promote new admin accounts: disable or delete factory-default accounts if possible; ensure separate accounts for administrators with least-privilege access.
- Enforce a strong password policy: use long, unique passwords with mixed character sets, and store them in a trusted password manager.
- Apply firmware updates: patch known vulnerabilities and enable secure logging.
- Validate success: log out and re-log in with new credentials, verify access control configurations, and document the changes.
- Ongoing hygiene: schedule regular credential audits and automated reminders for password reviews.
Best practices for managing admin access on WAGO devices
- Use unique admin accounts for each operator and administrator; avoid shared credentials.
- Disable broad admin roles and implement role-based access control (RBAC) to restrict privileges.
- Enable multifactor authentication on accessible interfaces whenever the platform supports it.
- Use a password manager and enforce standardized password policies across all WAGO devices.
- Rotate credentials on a defined schedule and after any suspected breach or personnel change.
- Segment networks to limit lateral movement; isolate critical WAGO devices from general IT traffic when possible.
- Maintain detailed audit logs and secure log storage for post-incident analysis.
How to verify changes and enforce ongoing security
After password changes, verify access integrity by attempting logins from authorized and unauthorized endpoints, reviewing logs for anomalies, and confirming that alerts fire on failed login attempts. Run periodic vulnerability scans focused on credential exposure and misconfigurations. Establish a routine for reviewing admin accounts, removing dormant users, and updating device documentation. Consider an annual security review that aligns with organizational cybersecurity policies and ICS-specific standards to sustain protection over time.
Industry guidance and compliance considerations for ICS security
Security standards such as IEC 62443 and NIST SP 800-82 provide frameworks for securing industrial control systems. When working with WAGO devices, align password management with these guidelines by enforcing strong authentication, segregating networks, and maintaining traceable audit trails. Regular firmware updates and configuration baselining are essential to compliance and risk reduction. The broader industry guidance emphasizes treating default credentials as a high-risk factor, and institutes controls that reduce exposure in continuous operation environments. The Default Password team emphasizes proactive hardening, including regular credential reviews and configuration baselines, as part of a resilient security posture.
WAGO default password guidance vs. recommended practices
| Aspect | Default Condition | Security Guidance |
|---|---|---|
| Default credential status | Often present on initial config | Immediately disable or change to unique credentials |
| Access control practices | Weak/empty admin accounts | Enforce least privilege and MFA where available |
Your Questions Answered
Why is the wago default password a risk?
Default credentials on WAGO devices create an easy path for attackers to gain admin access. This can lead to configuration changes, downtime, and safety implications. Always replace factory settings before production use.
Default credentials on WAGO devices create a path for attackers to gain admin access. Replace factory settings before production use.
How do I reset a WAGO device password?
Resetting involves verifying current admin access, creating new strong credentials, disabling or removing factory-default accounts, and updating firmware if needed. Always back up configurations before making changes.
Reset the admin password by creating new strong credentials and removing factory-default accounts after backing up configurations.
Can I disable default passwords on all WAGO devices?
Where possible, disable or rename default accounts in the device interface or via central management. Some devices require manual changes per device; in all cases, enforce unique credentials.
Disable defaults where possible and enforce unique credentials for each device.
What should I do if I forget the new password?
Use the device's recovery procedure or admin account reset process provided by the vendor, ensuring there is a secure backup method and appropriate authorization.
If you forget, use the vendor-provided recovery process with secure authorization.
Is MFA available on WAGO devices?
Some WAGO interfaces support MFA for remote access; enabling MFA greatly reduces risk even if a password is compromised. If MFA isn’t available, strengthen passwords and restrict access via network controls.
MFA can greatly reduce risk; enable it where available and strengthen other controls if not.
How often should I audit for default credentials?
Perform credential hygiene audits at least quarterly and after personnel change events. Include a review of all admin accounts, guest access, and any service accounts tied to WAGO devices.
Do quarterly credential audits and after staff changes.
“Default credentials are the weakest link in industrial networks; securing admin access to WAGO devices is essential for a resilient automation environment.”
Key Takeaways
- Audit devices for default credentials and document findings.
- Change defaults before deployment and disable factory accounts.
- Implement unique admin accounts with RBAC and MFA where possible.
- Rotate passwords regularly and use a password manager.
- Monitor logs and enforce ongoing credential hygiene across the environment.