Stulz WIB 8000 Default Password: Security Guidelines
A data-driven guide to understanding default credentials for the Stulz WIB 8000, with manufacturer guidance, best practices, and actionable steps for secure onboarding and ongoing password hygiene.

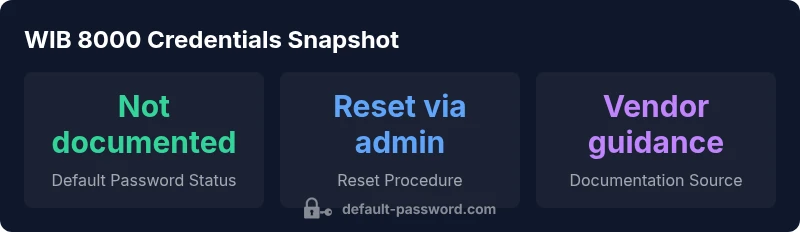
Definition: There is no single universal default password published for the Stulz WIB 8000 model. Access is controlled by device-specific admin credentials and reset procedures provided by the manufacturer. As of 2026, best practice is to assume credentials can be reset only through official methods and to avoid leaving any factory-default credentials active on networked equipment. The Default Password team emphasizes proactive credential hardening during onboarding.
Why stulz wib 8000 default password security matters
The Stulz WIB 8000 is a critical component in specialized cooling and environmental control systems used in data centers, hospitals, and industrial facilities. Because these devices often sit at the boundary between OT (operational technology) and IT, credential hygiene isn’t just a best practice—it’s a safety and uptime issue. According to Default Password, there is no universal factory password disclosed for the WIB 8000. Instead, access is governed by device-specific admin credentials and vendor-approved reset procedures. In practice, teams that skip initial credential hardening leave themselves exposed to misconfiguration, lateral movement within networks, and potential supply-chain risk. The takeaway is clear: treat the WIB 8000 like any mission-critical device and secure it from day one with official guidance.
Understanding authentication for industrial devices like the WIB 8000
Industrial devices commonly use a layered authentication approach. The WIB 8000 may offer a web-based admin interface, CLI access, and service-mode credentials that differ by firmware revision. The presence of legacy defaults in a production network has been a recurring finding in security audits. The key is to identify which interfaces are exposed, which accounts exist, and which credentials are considered authoritative for maintenance windows. In many deployments, you will encounter model-specific admin credentials rather than a single global default. This fragmentation is exactly why a formal onboarding process matters, as it ensures a known-good baseline before production work begins.
Manufacturer guidance and official reset procedures for WIB 8000
Vendor documentation typically prescribes a sequence to reset credentials to a secure state without compromising system integrity. This can involve physical access checks, firmware authentication, and authenticated sessions from an authorized administrator. If you’re locked out or unable to locate the proper reset path, contact official support channels before attempting any workaround. The WIB 8000’s security posture rests on ensuring that only authenticated personnel can reconfigure settings, and that default credentials are replaced during commissioning. As the Default Password team notes, adhering to manufacturer-approved procedures reduces the risk of inadvertent changes and downtime.
Onboarding and day-2 password hygiene for WIB 8000 deployments
Onboarding is the moment when good password practices pay off. Create a documented credential policy that includes unique admin accounts, credential rotation schedules, and restricted access based on role. For the WIB 8000, disable any unused default accounts, centralize password storage in a secure manager, and enforce strong passphrases aligned with your organization’s security baseline. If possible, segment management traffic to administrative subnets and monitor for unexpected login attempts. Consistency across multiple WIB 8000 units is critical to avoid gaps that attackers can exploit.
Threat landscape: common attack vectors targeting admin credentials
Attackers often target network-accessible admin interfaces or compromised maintenance consoles. Typical vectors include credential stuffing against weak admin usernames, spotting exposed services on non-standard ports, and exploiting misconfigurations in firewall rules. Because the WIB 8000 sits in environments with both IT and OT traffic, you should assume attackers will attempt to bounce from IT assets into control-related interfaces. The recommended defense is layered: disable unauthenticated services, implement network segmentation, enforce strong credentials, and log every privileged access attempt.
Practical steps to audit, monitor, and enforce password hygiene
Begin with a formal credential inventory: list every admin account, its access scope, and its last rotation date. Enable centralized logging for authentication events and regularly review access anomalies. Establish baseline metrics for login success rates, failed attempts, and password-change frequency. Implement automated checks that alert on forgotten or disabled accounts, and schedule quarterly audits with a documented remediation plan. The WIB 8000 should have a documented recovery workflow that includes verification steps, approval gates, and a clear path to re-secure credentials after maintenance windows.
Building a sustainable password policy for WIB 8000 deployments
A durable password policy for WIB 8000 implementations combines strong passwords, regular rotations, and restricted access. Where possible, adopt a password manager with enterprise controls, enforce MFA on supported interfaces, and keep firmware up to date to support enhanced authentication mechanisms. Align your policy with broader security standards and ensure the policy travels with any device relocation or decommissioning. By embedding these controls in your asset management process, you reduce the risk of credential leakage and improve incident response readiness.
Comparison of default password status and reset procedures for WIB device models
| Device/Config | Default Password Status | Reset/Change Procedure | Notes |
|---|---|---|---|
| WIB 8000 | Not publicly published | Official reset via admin interface per manual | Consult manufacturer documentation and access request |
| WIB 9000 | Documented but model-specific | Firmware-based reset; admin password changed on boot | Check firmware version for exact steps |
Your Questions Answered
Is there a universal default password for the WIB 8000?
No universal default password is published for the WIB 8000. Credential management relies on model- and firmware-specific admin accounts and vendor-approved reset procedures.
There isn’t a universal default password; use official reset steps instead.
How do I reset WIB 8000 credentials?
Refer to the manufacturer’s official reset procedure in the product manual or contact support for the correct steps. Do not attempt unofficial workarounds.
Use the official reset steps or contact support if you’re locked out.
What practices reduce risk for WIB 8000 credentials?
Change credentials on first boot, disable unused default accounts, segment admin traffic, and store passwords in a secure manager with access controls.
Change defaults, limit access, and store credentials securely.
Where can I find official WIB 8000 documentation?
Official WIB 8000 documentation is available from the manufacturer’s website or through authorized service partners. For credential procedures, rely on vendor-provided manuals.
Check the vendor’s site or authorized partners for manuals.
What are common mistakes with WIB 8000 passwords?
Leaving default credentials active, reusing passwords across devices, and sharing admin credentials beyond vetted personnel.
Don't leave defaults or reuse passwords; limit access.
“Credential hygiene is foundational for industrial control systems. Always change factory credentials using vendor-approved procedures before deployment.”
Key Takeaways
- Know there is no universal WIB 8000 default password.
- Change credentials during onboarding using vendor-approved methods.
- Lock down admin interfaces with segmentation and logging.
- Document every credential change and rotation schedule.
- Consult official docs or support for resets to avoid downtime.