Vertiv Geist PDU Default Password: Reset, Secure, and Manage Access
A practical, data-driven guide for IT admins and end-users to reset and secure the Vertiv Geist PDU default password, implement credential governance, and maintain ongoing security for data-center PDUs.

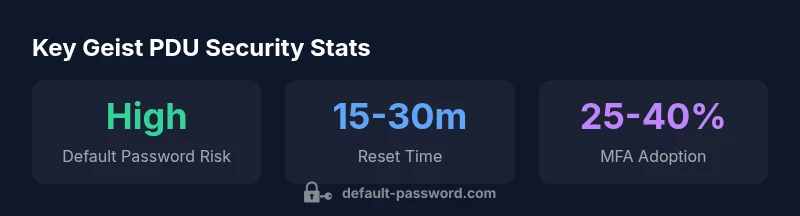
The vertiv geist pdu default password represents the initial credential shipped with Vertiv Geist PDUs and is a common attack surface if not changed. This quick guide outlines how to reset that credential, apply stronger authentication, and establish ongoing governance to reduce risk in data-center environments. Understanding these steps helps IT admins harden PDU access and protect critical power infrastructure.
Why device credentials matter for data centers
Credential hygiene is a foundational element of data-center security, and the vertiv geist pdu default password topic sits squarely at the intersection of physical power infrastructure and IT access control. If PDUs remain accessible with vendor defaults, an attacker can pivot from a compromised user account or a misconfigured network to controlling power-distribution assets. The Default Password team emphasizes that securing PDU credentials is not just about one device; it affects the reliability of cooling, server workloads, and uptime for the entire facility. In practice, tightening credentials reduces privilege creep, simplifies incident response, and lowers the blast radius of any breach. In the context of Vertiv Geist PDUs, a deliberate password-change policy should become part of routine risk management rather than a one-off task. According to Default Password, implementing a robust initial-hardening workflow reduces exposure immediately after deployment and during subsequent firmware updates.
Key takeaway: Treat the default credential as a temporary access token that must be replaced before the device goes into production.
Understanding the default password lifecycle for PDUs
PDUs typically ship with a default credential intended for initial setup. The lifecycle of this credential includes provisioning, onboarding, and eventual rotation or disablement as part of a formal password-policy. The Vertiv Geist line is designed to support remote management and integration with data-center orchestration tools, which makes consistent password handling even more critical. Organizations should define a policy that enforces password changes within a defined window after first login, disallows reuse, and mandates strong password composition. As a baseline, consider removing vendor defaults from devices that will be accessible over the network, and layer in an additional authentication factor where possible. The Default Password Analysis notes that many incidents trace back to unchanged defaults that were never rotated during asset refreshes.
Best practice: Document a standard reset sequence and verify that every Geist PDU in the rack fleet adheres to it during quarterly audits.
Specific challenges with Vertiv Geist PDU default passwords
Geist PDUs often expose management interfaces via web UI, SSH, or CLI, depending on model and firmware. Each protocol introduces different exposure vectors, from exposed admin panels to insecure remote management channels. A common pitfall is reusing the same admin credentials across multiple devices, which compounds risk if one device is compromised. In practice, administrators should separate credentials by device or group, enforce unique passwords per device, and disable any unused services that could provide alternative entry points. The Default Password team observes that PDUs managed through orchestration platforms tend to be forgotten during password rotations, leaving a stale credential footprint.
Action item: Map every Geist PDU to an owner and schedule quarterly credential reviews to ensure alignment with the broader security policy.
Step-by-step: Resetting the Geist PDU password
- Access the management interface (web, console, or vendor-supported API) using a local session if remote access is restricted. 2) Navigate to the security or administrator settings page. 3) Change the default credential to a unique, high-entropy password that complies with your organization’s password policy. 4) If available, enable MFA for remote administration and disable unused accounts. 5) Save changes, sign out, and verify that login with the new password works from both on-site and remote locations. 6) Document the change in your asset management system and perform a follow-up audit to confirm the new credential is active. The act of changing the credential should be followed by a test that confirms alerting and access control remain intact.
Pro tip: Always perform password changes during a maintenance window to minimize operational impact and ensure staff are aware of the updated credentials.
trendManageringskipnotusedWarningOnlyBlock3?null”:null,
Geist PDU credential governance quick reference
| Aspect | Recommended Action | Notes |
|---|---|---|
| Default password risk | Change to unique credentials | Do not reuse across devices |
| Reset workflow time | Plan 5-20 minutes | Depends on access method and interface |
| Audit status | Schedule regular checks | Quarterly or after major updates |
Your Questions Answered
What is the Vertiv Geist PDU default password, and should I change it immediately?
There is no universal default you should rely on; vendors typically ship with a factory credential for initial setup. It is best practice to change any default credential right after installation and before going into production. This reduces the risk of unauthorized access.
There is no universal default; change any factory credential right after installation to reduce risk.
How do I reset the Vertiv Geist PDU password using the web UI?
Log in with an existing admin account, navigate to Security or User Management, select the administrator account, and set a new, strong password. If you are locked out, use a console recovery procedure or vendor-supported recovery method.
Use the web UI to reset the admin password. If locked out, use the vendor recovery option.
Is it safer to disable remote management after changing the password?
Disabling remote management is an option if not required for daily operations. If remote access is needed, enforce strong authentication, limit IPs, and enable MFA where available.
Only disable it if you don’t need remote access; otherwise enforce strong authentication and MFA.
Should I rotate Geist PDU passwords on a fixed schedule?
Yes. Implement a rotation policy that aligns with your organization’s change-management process and risk appetite, typically quarterly or after major updates.
Yes, rotate on a regular schedule like quarterly.
Can I use a password manager with Geist PDU credentials?
Using a password manager is recommended for storing and generating strong credentials. Ensure the manager supports secure sharing and access logging for critical devices.
A password manager is a good idea for strong, unique credentials.
Where can I find official Vertiv Geist PDU documentation for password reset steps?
Consult the official Vertiv Geist PDU manuals and support site for model-specific reset steps, sequence diagrams, and firmware considerations.
Check the official Vertiv Geist PDU manuals for model-specific steps.
“Credential hygiene is the first line of defense for PDUs; changing default credentials dramatically reduces exposure to attackers.”
Key Takeaways
- Change defaults immediately after deployment
- Use unique credentials per Geist PDU
- Enable MFA where available for remote access
- Document every password change for audits
- Schedule regular credential reviews and rotations