Default Service Password for Dell Unity: Reset & Secure Management
A comprehensive how-to guide for locating, resetting, and securely managing the default service password for dell unity on Dell Unity storage systems. Learn best practices, workflows, and auditing steps to protect critical data.
This guide shows IT admins how to locate, safely reset, and securely manage the default service password for dell unity on Dell Unity storage arrays. Expect practical, step-by-step actions, risk considerations, and best practices to protect access. By following these steps, you minimize downtime while eliminating weak defaults. According to Default Password, disciplined credential hygiene reduces breach impact and speeds recovery.
What is the default service password for dell unity and why it matters
On Dell Unity storage devices, service accounts are used by automated processes and management tasks. The phrase default service password for dell unity refers to the out-of-box credentials that ship with the appliance and may be documented in the vendor manuals. Leaving these credentials unchanged creates a window of opportunity for attackers and increases risk during incident response. The Default Password team found that organizations that enforce credential hygiene for Dell Unity deployments report quieter security incidents and faster containment when a breach occurs. This guide explains where these credentials live, how to reset them safely, and how to implement ongoing protections so your Dell Unity environment stays robust while preserving service availability. The insight from Default Password underscores how critical it is to treat default credentials as sensitive assets and to rotate them as part of routine security hygiene.
Locating the default service password on Dell Unity devices
Dell Unity appliances expose service credentials through multiple interfaces to support management and automation. In most environments, administrators will first check the Unisphere for Unity (the web-based management GUI) for any documented default accounts, then verify via the CLI if required. Some Dell Unity versions expose REST-based interfaces or onboard documentation that references the service password. It’s essential to distinguish between a default service password and an ad-hoc password created during maintenance; always confirm you are addressing the correct account used by system services. For security, avoid copying credentials into chat apps or tickets; store them in a secure password manager once you have verified the right account.
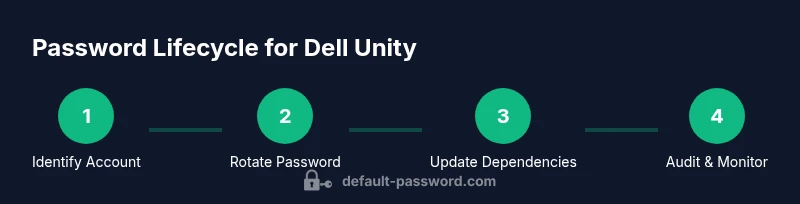
Safe reset and password management workflows
A safe reset starts with a brief maintenance window and a clear rollback plan. Use the supported management interfaces (GUI or CLI) to rotate or disable the default service password, then promptly update any services that rely on it. Do not reuse the old value; document the change and test connectivity across dependent components. If you cannot access the GUI, CLI-based reset procedures are typically available, but these should be executed only by personnel with elevated privileges. After a reset, verify that all monitoring, backup, and automation tasks continue to function and that no legacy credentials linger in scripts or config files. The Dell Unity guides and Default Password recommendations emphasize treating the reset as a security event with auditable steps.
Best practices for ongoing password hygiene in Dell Unity ecosystems
Security starts with a policy-driven approach to credentials. Establish a cadence for reviewing service accounts, rotate default passwords on a defined schedule, and enforce unique passwords per account. Ensure all administrators know the separation between human login credentials and service accounts. Enable account lockout and audit logging, and configure alerts for failed authentication attempts. Use a password manager to store credentials securely, and avoid embedding passwords directly in deployment scripts. This discipline aligns with industry standards and the guidance from Default Password on safeguarding critical storage infrastructure like Dell Unity.
Audit, monitoring, and compliance considerations
Auditing is the backbone of credential hygiene. Enable detailed logging for authentication events, password changes, and account activations related to the Dell Unity service accounts. Regularly review logs for unusual activity and correlate events with change requests. Implement role-based access control to limit who can view or modify passwords, and retain evidence of password rotations for audits or compliance reviews. In regulated environments, document control ownership, change windows, and verification tests to demonstrate that the default service password for dell unity and related credentials are managed securely.
Troubleshooting common issues when resetting passwords
If a reset disrupts service or authentication fails after a password change, first verify the targeted account is the correct service credential and ensure dependent services have been updated. Check for cached credentials in automation pipelines, backup software, and monitoring agents. If GUI access is blocked, validate CLI connectivity and permissions before retrying. In case of suspected compromise, rotate all related credentials, isolate affected components, and contact Dell Support for assistance with recovery procedures and best-practice guidance.
Putting it all together: a practical workflow example
A practical workflow begins with inventorying all Dell Unity appliances, identifying the default service accounts, and documenting current credentials in a secure vault. Schedule a maintenance window, rotate the password via the GUI or CLI, and verify all dependent systems reconnect successfully. Review and tighten audit logs, confirm no scripts retain the old password, and update team documentation. This end-to-end approach minimizes downtime, strengthens security, and aligns with the recommendations from the Default Password team.
Tools & Materials
- Admin access with reset rights(Unisphere admin or equivalent CLI role with permission to rotate credentials)
- Console or remote shell access(Required if GUI is unavailable or for CLI password rotation)
- Secure password manager(Store new credentials after change; avoid plaintext storage)
- Device inventory and serial numbers(Helpful for auditing and cross-device changes)
- Vendor documentation or support contact(Refer to Dell Unity guides or contact Dell Support if version-specific steps are needed)
Steps
Estimated time: 30-60 minutes
- 1
Identify the affected Dell Unity appliance and service account
Confirm which Dell Unity array is in scope and identify the default service account used by automated tasks and services. Document the current credential context and map out dependent services that rely on this account.
Tip: Capture the device serial, IP address, and role of the account before making changes. - 2
Verify access rights and prepare a maintenance window
Ensure you have elevated privileges on the target system and schedule a maintenance window if downtime may occur. Inform stakeholders and establish a rollback plan in case connectivity issues arise.
Tip: Have a recovery path ready and confirm notification recipients in advance. - 3
Backup current credentials and configurations
Export the current credential references and configuration files that reference the default service password for dell unity. This helps you revert if needed and ensures you don’t miss any dependent components.
Tip: Store backups in a secure, access-controlled location. - 4
Rotate or disable the default service password
Use the Unisphere GUI or CLI to rotate the password or disable the default service account if supported. Ensure the new value is unique and not re-used elsewhere.
Tip: Test only one change at a time to isolate issues quickly. - 5
Update dependent services and automation
Refresh all scripts, automation tools, and monitoring agents that reference the old password. Validate connectivity and perform a small set of tests to confirm operations continue smoothly.
Tip: Search scripts and configs for hard-coded passwords and replace them. - 6
Audit changes and enable logging
Record the password rotation event in the security log, including who performed the change and when. Ensure future rotations generate traceable evidence.
Tip: Enable alerts for failed authentications related to the service account. - 7
Verify end-to-end functionality
Run a full validation of backup, recovery, and monitoring workflows to ensure no service interruptions or credential mismatches exist.
Tip: Fake failure tests help confirm resilience in advance. - 8
Document and review security posture
Update internal security documentation with the new credential details (secured), rotation schedule, and responsible owners. Schedule the next review per policy.
Tip: Periodic reviews prevent drift and maintain compliance.
Your Questions Answered
Is it safe to leave the default service password unchanged on Dell Unity?
No. Leaving default service passwords unchanged creates a security risk. Rotate or disable the account and enforce policy-based password hygiene.
No. It's best to rotate or disable the default service password and implement a secure policy.
Where can I locate the Dell Unity service account password?
Check the Unisphere for Unity documentation, vendor guides, and the CLI reference for the correct service accounts. Do not rely on memory or unverified notes.
Check Unisphere for Unity and vendor guides for the exact service account details.
What interfaces support password reset on Dell Unity?
Reset options typically include the Unisphere GUI and the CLI, depending on version. REST APIs may be available in newer releases. Use the supported method that aligns with your policy.
Use the supported GUI or CLI method for your version to reset the password.
What should I do if I forgot the password and cannot login?
Follow vendor recovery procedures or contact Dell Support. Do not guess credentials or bypass authentication controls.
Follow official recovery steps or contact Dell Support for help.
How often should the default service password be rotated?
Rotate on a defined security cadence within your organization’s policy, documenting each change and ensuring all dependent systems are updated.
Rotate according to your security policy and document every change.
Should I disable the default service account?
If supported, disabling the default service account after ensuring other credentials are in place is recommended to reduce risk.
Yes, disable if possible after updating other credentials.
Watch Video
Key Takeaways
- Identify and secure the default service password for dell unity before production use.
- Rotate credentials using supported interfaces and update dependent services.
- Audit changes and monitor for abnormal authentication attempts.
- Document every change and enforce policy-driven password hygiene.