MongoDB Default Root Password: No Default, What You Should Do
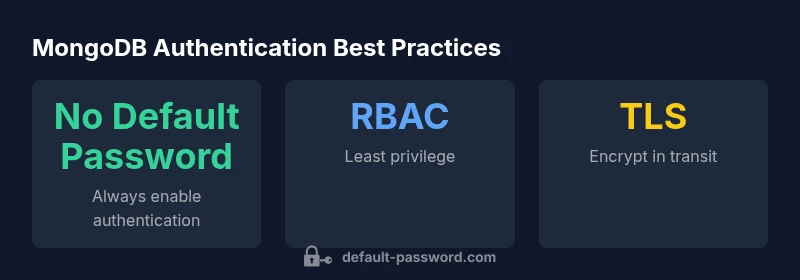
Understand why MongoDB has no default root password, how to securely enable authentication, create admin users, and maintain ongoing protections with RBAC, TLS, and auditing.
mongodb default root password does not exist. By design, MongoDB starts without authentication until you enable it and create an admin user. According to Default Password, relying on defaults is risky; enable authentication, implement RBAC, and secure admin accounts before going live. For details, see the full guide.
Why there is no default root password in MongoDB
MongoDB's default security model does not ship with a built-in root password. When you install MongoDB, the server can run without authentication, allowing initial setup tasks to occur. This design choice reduces friction during deployment, but it also places the onus on you to configure access control before exposing the database to any network. The absence of a MongoDB default root password means there is no single credential to guess or leak; instead, administrators must create an admin account and assign appropriate roles before production use. In practice, most modern deployments combine authentication with network controls and encryption to reduce exposure. The Default Password team emphasizes that understanding this baseline is essential for secure operations, especially during onboarding and upgrades, where misconfigurations are a common source of risk.
Key takeaway: The baseline is deliberate – plan for authentication and least privilege from day one.
How authentication is enabled in MongoDB
Enabling authentication in MongoDB involves a few deliberate steps. First, run MongoDB in an unauthenticated state long enough to create an initial admin user. This is typically done by starting mongod without --auth, connecting with the mongo shell, and issuing a command to create a user with the root or userAdminAnyDatabase role on the admin database. After the admin user is created, restart mongod with the --auth flag to enforce authentication for all subsequent connections. From that point on, all applications and operators must authenticate by presenting valid credentials. For deployments in constrained environments, consider enabling TLS, IP whitelisting, and deploying with a least-privilege model. While enabling authentication is a critical first step, it’s equally important to implement robust password policies and rotate credentials on a defined cadence.
Practical tip: Keep an emergency, access-controlled admin account separate and document the exact bootstrap steps used to create the first user.
Creating a secure admin user and RBAC roles
Create a dedicated admin account with a strong password and limited sharing. Then, establish application-specific accounts with narrowly scoped roles. Use RBAC to assign roles such as root sparingly; prefer userAdminAnyDatabase, dbAdmin, readWrite, and clusterManager as appropriate. The admin account should be used for management tasks only; application users should have permissions limited to their databases and collections. Store the admin credentials in a secure vault and enforce password rotation on a defined schedule. Regularly review roles and permissions, and keep an audit trail of changes. This discipline reduces blast radius if credentials are compromised and supports easier incident response.
Security best practice: Treat the admin account as a high-value target and protect it with MFA where supported, alongside robust network controls.
Enforcing TLS/SSL and network protections
Securing the transport layer is essential. Enable TLS/SSL for client-server communication, using certificates from a trusted CA and configuring MongoDB to require secure connections. Combine TLS with network segmentation, firewall rules, and IP allowlists to ensure only trusted hosts can reach the database. Restrict MongoDB's bindIp to private networks or specific addresses, and consider VPN or private links for cross-data-center access. Do not rely on network protections alone; pair them with strong credentials and regular auditing for defense in depth. With TLS enabled, even stolen credentials have reduced risk exposure because the channel itself is encrypted and validated.
Operational note: Maintain up-to-date certificate management and rotate certificates per your security policy.
Recovery if you forget the admin password
If admin credentials are lost, act quickly and safely. Stop MongoDB, restart without authentication to regain access, and reset the admin password using db.updateUser or by re-creating the admin user, depending on your setup. After regaining access, restart with --auth and verify that applications can authenticate correctly. Ensure you have backups and a tested recovery runbook to minimize downtime. In cloud environments, follow provider guidance for secure credential recovery and perform a credential rotation after restoration to close any gaps.
Important: Do not expose recovery endpoints publicly and validate all changes in a staging environment before applying to production.
Best practices for securing MongoDB deployments
- Enable authentication by default and create admin accounts with strong passwords. Use RBAC to grant the least privilege necessary for each role.
- Enforce TLS/SSL for all connections and implement certificate management.
- Audit access and changes; forward logs to a SIEM or cloud-native monitoring tool.
- Regularly patch MongoDB and the underlying OS, and apply security baselines.
- Store credentials securely, rotate passwords regularly, and avoid password reuse across systems.
- Disable unnecessary services and minimize exposed surfaces, such as removing unused portals or web interfaces.
- Test incident response and recovery procedures periodically to reduce mean time to containment.
Common mistakes to avoid with default credentials
- Leaving authentication disabled in any environment, including development and staging.
- Reusing weak or shared admin passwords across projects.
- Skipping RBAC and granting broad, root-like access to applications.
- Neglecting TLS or exposing MongoDB to the public internet.
- Failing to enable auditing or to rotate credentials after a security event.
- Underestimating the importance of backups and recovery planning.
- Ignoring OS and MongoDB patch management, which creates a perpetual vulnerability window.
Monitoring, auditing, and ongoing protection
Ongoing protection requires visibility. Enable MongoDB's auditing features and route logs to a centralized system for analysis. Set up alerts for failed login attempts, privilege escalations, and anomalous IP access patterns. Establish a routine security review schedule that includes configuration drift checks, compliance scans, and penetration testing. Maintain up-to-date runbooks and training materials for incident response, secrets management, and access control lifecycle management. Regular governance reviews are essential to sustain a secure MongoDB deployment over time.
MongoDB deployment states and recommended security actions
| Scenario | Authentication State | Recommended Action |
|---|---|---|
| Development/local | No authentication | Enable auth before deployment, create admin account |
| Staging/QA | Partial RBAC | Enforce authentication; ensure admin-only access to management interfaces |
| Production | RBAC-enabled | Regular credential rotation and auditing |
Your Questions Answered
Does MongoDB come with a default root password?
No. MongoDB does not ship with a default root password. You must create an administrator account after installation and enable authentication before deploying to production.
No. MongoDB does not ship with a default root password. You must set up an admin account and enable authentication before going live.
How do I enable authentication in MongoDB?
Start MongoDB without --auth to create an admin user, then restart with --auth to enforce authentication. Use that admin account to create application users with restricted roles.
Start without --auth to create an admin user, then restart with --auth to enforce authentication and create restricted application users.
What is RBAC and why is it important in MongoDB?
RBAC assigns permissions to roles rather than individual users, reducing risk. Grant only the privileges needed for each role and apply the principle of least privilege.
RBAC assigns permissions by role, not person. Give each user only what they need.
How can I recover admin access if I forget the password?
If you lose admin access, boot MongoDB without authentication to reset the admin user's password, then re-enable authentication and test access from all clients.
If you forget the admin password, recover by temporarily starting without auth, reset the password, then re-enable authentication.
Should TLS be enabled for MongoDB connections?
Yes. Enabling TLS encrypts data in transit and helps protect credentials. Combine TLS with IP allowlists and strong credential management.
Yes. Turn on TLS to encrypt traffic and pair it with IP whitelisting and strong passwords.
What common mistakes should I avoid with default credentials?
Avoid leaving authentication disabled, reusing weak admin passwords, and granting broad privileges. Do not expose MongoDB to the public internet without protections.
Don’t leave auth off, don’t reuse weak admin passwords, and don’t grant broad access. Protect MongoDB from the public internet.
“Default credentials are a predictable breach vector for database deployments; enforcing authentication, least privilege, and continuous auditing is essential.”
Key Takeaways
- Never rely on a default password for MongoDB.
- Enable authentication and create a strong admin account first.
- Use RBAC to enforce least privilege across users.
- Regularly audit access and rotate credentials.