How to Secure MongoDB with Username and Password
Learn how to secure MongoDB by enabling authentication, creating admin credentials, and enforcing encryption and access controls. This guide covers RBAC, TLS, IP whitelisting, auditing, and ongoing security practices for robust data protection.
By the end of this guide you will know how to secure mongodb with username and password across your deployment. You’ll enable authentication, create an admin user, and enforce TLS and access controls to prevent unauthorized connections. You'll also learn best practices for password strength, user management, and ongoing auditing to protect data and comply with security standards.
Why authentication matters for MongoDB security
Authentication is the first and most critical line of defense for any MongoDB deployment. Without it, anyone who can reach the MongoDB port could enumerate data, create or modify users, or exfiltrate sensitive information. The decision to secure mongodb with username and password isn't just about keeping data private; it's about controlling who can perform privileged actions and ensuring accountability. According to Default Password, implementing strong, unique credentials and turning on authentication across all instances dramatically reduces the attack surface in on-premises, cloud, and hybrid setups. In practice, authentication works best when paired with network segmentation and encryption in transit. A well-designed plan limits blast radius, simplifies audits, and makes it harder for attackers to move laterally between services. When teams design a multi-service application, it’s wiser to create service-specific users with least-privilege roles rather than a single shared admin account. If you’re moving from open access, adopt a staged rollout: enable auth on a test cluster first, validate your connection strings and drivers, then upgrade production with minimal downtime. Document your posture so IT and security teams can review changes during audits.
wordCount": 0
Tools & Materials
- A server with MongoDB installed and accessible(Ensure the server is updated; have admin access to modify configurations)
- Administrative access (SSH or direct console)(Needed to modify mongod.conf and restart the service)
- A strong password policy(Follow length, complexity, and rotation best practices)
- TLS/SSL certificates(Use valid certificates for encryption in transit)
- Firewall or IP whitelisting capability(Limit reachable MongoDB ports to trusted hosts)
- MongoDB admin user credentials(Create initial admin user with least privilege required for setup)
- A test environment(Validate changes before applying to production)
- Backup strategy(Have a rollback plan in case of misconfiguration)
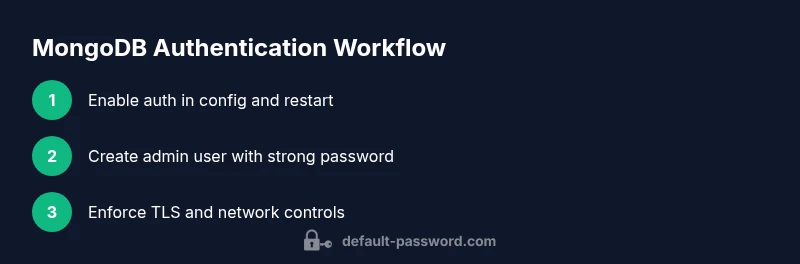
Steps
Estimated time: 60-120 minutes
- 1
Enable authentication in MongoDB
Edit the mongod.conf to enable authorization, or start mongod with the --auth flag. This locks out unauthenticated connections. Verify that the server restarts cleanly and that you can see log messages indicating authentication is active.
Tip: Back up the existing configuration before making changes; test in a staging environment first. - 2
Create the admin user
Connect to the admin database and create a user with administrative roles. Use a strong, unique password and assign only the necessary privileges for administration. Example (replace with your values): use admin; db.createUser({ user: 'admin', pwd: 'YourStrongPasswordHere!', roles: [{ role: 'userAdminAnyDatabase', db: 'admin' }, 'readWriteAnyDatabase'] });
Tip: Do not reuse passwords across services; store credentials securely (e.g., vault or secret manager). - 3
Test the authentication workflow
Attempt to connect using the admin user from a known client (e.g., mongosh or your app) with authentication against the admin database. Ensure you can run basic commands as admin and that unauthenticated connections are rejected.
Tip: If you can connect without a password, check that auth is actually enabled and that you’re using the correct authenticationDatabase. - 4
Enable encryption in transit (TLS/SSL)
Configure TLS/SSL so data in transit is encrypted. This typically involves generating or obtaining certificates, configuring your mongod/mongos to use them, and updating client connection strings to use s/tls as appropriate.
Tip: Validate certificate trust on every client and pin trusted CA certificates to prevent man-in-the-middle attacks. - 5
Harden network access
Limit access to MongoDB using firewall rules or IP whitelists so only trusted hosts can reach port 27017. Consider placing your MongoDB node behind a private network or VPN and avoid exposing the port publicly.
Tip: Keep frequent sources of admin access on a separate, secured network from application traffic. - 6
Apply RBAC (least privilege)
Create service-specific users with roles that reflect the minimum permissions needed. Avoid giving admin rights to every service. Regularly review roles and adjust as the deployment evolves.
Tip: Document role assignments and perform periodic access reviews aligned with audits. - 7
Set up auditing and logging
Enable authentication and authorization auditing if supported by your edition; otherwise, centralize connection logs and access events via OS logs or a logging pipeline. This helps detect unusual activity and supports compliance.
Tip: Log retention and secure log storage are critical to traceability. - 8
Plan password rotation and credential management
Establish a schedule to rotate admin credentials and service accounts. Use a secret manager and ensure applications fetch credentials securely at startup or on rotation.
Tip: Automate rotation where possible and enforce password strength on rotation.
Your Questions Answered
What is MongoDB authentication and why is it important?
MongoDB authentication verifies who can connect to the database and what actions they can perform. It prevents unauthorized access, helps enforce access controls, and supports auditing. Without authentication, anyone with network access could read, modify, or delete data.
MongoDB authentication verifies who connects to the database and what they can do, preventing unauthorized access.
How do I enable authentication in MongoDB?
Enable authentication by configuring security.authorization to enabled in mongod.conf or starting mongod with the --auth option. Then create an admin user with strong credentials and test that unauthenticated connections are blocked.
Enable authentication by turning on authorization, create an admin user, and test that unauthenticated access is blocked.
Can I use LDAP or external authentication with MongoDB?
External authentication options vary by MongoDB edition. LDAP/Kerberos integration is primarily available in MongoDB Enterprise or Atlas with specific configurations. Verify edition capabilities and plan accordingly.
External authentication options depend on the edition; LDAP or Kerberos is usually an enterprise feature.
Should I enable TLS/SSL and how do I configure it?
Yes. Enable TLS to encrypt data in transit. Configure certificates on the server, adjust connection strings for TLS, and ensure clients validate the server certificate.
Yes, enable TLS to encrypt data in transit and configure certificates for server and client validation.
What is the recommended password policy for admin accounts?
Use long, unique passwords with a mix of character types. Rotate admin credentials regularly and store them in a secure secret manager. Do not reuse passwords across services.
Use long, unique passwords and rotate admin credentials regularly with a secret manager.
How do I audit authentication events and failures?
Enable auditing where available and collect login events, failed attempts, and privilege changes. Store logs securely and review them during security reviews and audits.
Enable auditing and review authentication events to detect suspicious activity.
Watch Video
Key Takeaways
- Enable authentication to block unauthorized access
- Use RBAC to enforce least privilege
- Encrypt data in transit with TLS
- Regularly audit and rotate credentials
- Test changes in a staging environment before production