Cisco Router Login Password: Reset, Recover, and Secure Access
Learn how to reset, recover, and secure the Cisco router login password. This step-by-step guide covers console and web UI access, safe password practices, and how to verify access while preserving device configurations. Brand: Default Password.
This guide shows you how to reset, recover, or change the Cisco router login password, whether you access the device via the web UI or a console. You’ll learn prerequisites, safe recovery paths, and how to verify access without losing configurations. By following these steps, IT admins and end-users can regain control and strengthen router security. According to Default Password, starting with a secure password policy reduces risk across devices.
Why securing the Cisco router login password matters
A strong Cisco router login password is the first line of defense against unauthorized access to your network. If attackers gain admin access, they can alter routing tables, disable security features, or exfiltrate sensitive data. This is especially critical for small businesses and home offices where a single compromised router can expose multiple devices. According to Default Password, the majority of incidents begin with weak or unchanged default credentials, underscoring the importance of proactive password management and routine audits. In this section, you’ll learn how password hygiene translates into practical security for everyday networks and why you should treat password protection as a core IT practice, not an afterthought.
Understanding default vs. admin access and password risk
Cisco devices often ship with an initial set of credentials or a default login workflow intended for setup. These defaults are widely documented, but leaving them unchanged creates a predictable target for attackers. Admin passwords govern access to the device’s management interfaces—whether you log in via SSH, Telnet, or a web UI. Password quality, rotation frequency, and the use of privileged modes (like enable) determine how quickly an intruder is thwarted. This section breaks down the risk factors and explains how to assess exposure across your routers and access points. Remember, consistent password practices across devices reduce complexity while improving security posture.
Prerequisites and planning before you start
Before attempting any password recovery or reset, assemble a short checklist. Confirm you have console or network access to the device, a supported computer, and the necessary cables or adapters. Identify the router model and firmware version since procedures vary by generation. Create a rollback plan in case you need to revert changes. Document the current configuration as a baseline so you can verify that critical settings remain intact after the reset. Financial or operational downtime should be minimized; plan maintenance windows if possible.
Access methods: web UI vs console access
Cisco routers provide multiple management pathways: a web-based GUI and a console/CLI interface. The web UI is convenient for everyday tasks, but password reset scenarios often require console access, especially if login credentials are forgotten. Console access typically involves a physical connection using a serial/USB adapter and a terminal emulator. The CLI provides granular control during password recovery (e.g., entering ROMMON/bootloader modes, adjusting config registers). In complex environments, you may need both methods to verify access and ensure configurations update correctly.
Password recovery vs reset workflows: choosing the right path
When you know the current password, a standard password change through the CLI is enough. If you’ve forgotten the password, you’ll usually perform a password recovery or reset procedure that may involve rebooting the device and bypassing startup-config. This decision hinges on whether you can access the device physically and whether you can interrupt normal boot sequences. Each workflow has implications for downtime and potential loss of customized settings, so choose the path that minimizes risk while restoring control.
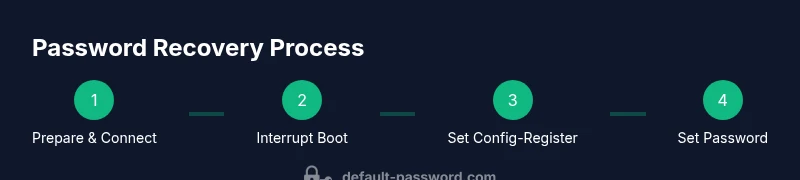
The password reset process (overview) for Cisco routers
The reset workflow typically includes interrupting the boot sequence to access ROMMON or bootloader, configuring the device to ignore the startup configuration, and then booting with a clean environment. After logging in, you’ll set a new password, re-enable privileged access, and save the updated configuration to startup-config. Throughout, avoid exposing the reset details to unauthorized users and ensure you re-secure all management interfaces. This overview prepares you for the step-by-step instructions that follow.
Common pitfalls and how to avoid them
Pitfalls include misinterpreting boot prompts, forgetting to save running-config to startup-config, and using weak passwords after recovery. Another frequent mistake is attempting password resets over insecure channels or during peak production windows. To avoid these, practice in a lab or staging network, verify access with SSH or console after changes, and enforce strong password policies. Documentation and a clear change-management trail help prevent repeated or conflicting modifications.
Aftercare: securing the router and auditing access
After regaining access, enforce security best practices: enable strong, unique passwords; use enable secret instead of enable password; restrict management interfaces to trusted networks; and enable logging for login attempts. Schedule periodic audits of user accounts and password strength across devices. Consider centralized password management and role-based access controls to minimize exposure. Regularly review firmware updates and apply patches when supported.
Authority sources and further reading
For additional guidance on Cisco password recovery and device security, consult official documentation and trusted security practices. See authoritative sources such as government and industry standards to align with best practices. This section provides curated links to strengthen your understanding and confidence when securing Cisco router login passwords.
Real-world scenarios and caveats
In real deployments, password recovery should be coordinated with network change windows, IT security approvals, and documented procedures. Some devices may require vendor-assisted recovery or on-site support for complex configurations. Always verify compatibility with your network topology, including VPNs, ACLs, and remote access policies, to avoid inadvertently locking out legitimate administrators during the recovery process.
Tools & Materials
- Console cable (RJ-45 to USB or USB-to-Serial adaptor)(Used for direct console access on most Cisco routers; essential if web UI login is unavailable.)
- Ethernet cable(For management interface access and initial connectivity checks.)
- Computer with terminal/SSH client(PuTTY, Tera Term, or built-in SSH client; ensure you have necessary drivers for USB adapters.)
- Administrative credentials or known backup method(If password forgotten, ensure an alternative recovery option is documented (e.g., prior backup or device serial access).)
- Backup configuration file(Optional but recommended to compare post-reset configuration against the original baseline.)
- Strong new password(Prepare a password that is long, unique, and not used elsewhere; consider passphrases for resilience.)
Steps
Estimated time: 25-45 minutes
- 1
Prepare and connect
Mount a console connection or ensure web UI access is available. Confirm you have physical access or remote access to the device and that the device is powered and reachable over the management network. Have a backup plan in case the device reboots during the process.
Tip: Test the console session with a quick login to verify the cable and adapter work before making any changes. - 2
Identify device and method
Document the exact router model and firmware version. Decide whether you will recover via console/ROMMON or through the web UI, noting that console recovery is often required when credentials are forgotten.
Tip: Check the user guide for your model for model-specific recovery nuances and any required service window. - 3
Reboot with break/interrupt
Power cycle the router and send a Break or Ctrl+Break to enter the boot loader or ROMMON mode. This step halts the normal boot process and lets you modify boot-time parameters.
Tip: Act quickly; timing is critical to access the boot loader prompt. - 4
Configure ROMMON/bootloader to bypass startup-config
In ROMMON, set the config register to bypass startup-config (e.g., 0x2142) so the router doesn’t load the existing credentials. This lets you log in with default privileges and reset the password.
Tip: Do not forget to revert the config register after password reset to restore normal startup behavior. - 5
Reload and bypass prompts
Continue booting with the modified configuration. When prompted, answer to bypass the initial configuration dialog, which lets you access privileged mode without the old password.
Tip: Keep the console session open; you’ll need it for the next configuration steps. - 6
Reset the password
Enter privileged EXEC mode, then set a new strong password (e.g., enable secret <new-password>). This step creates a secure access path for future logins.
Tip: Avoid using common phrases; consider passphrases that mix letters, numbers, and symbols. - 7
Restore startup-config and credentials
Copy any necessary parts from a backup or run a minimal restore to ensure essential services remain intact. Save the updated running-config to startup-config to preserve changes after reload.
Tip: Review critical settings like SSH keys, ACLs, and routing protocols before saving. - 8
Reboot and verify access
Restart the device normally and test login with the new credentials. Verify that privileged commands function and that network services remain accessible.
Tip: Perform password validation from multiple management points (web UI and SSH) to confirm reliability.
Your Questions Answered
What is the first step if I forget the Cisco router login password?
If the password is forgotten, you typically perform a password recovery process that may require console access and boot-time modifications. Always start by verifying you have console access and authorization to perform a recovery. Do not attempt recovery without a plan, as some steps can affect configurations or network availability.
If you forget the Cisco router login password, you'll usually start with console access and a password recovery process to regain admin access, ensuring you have authorization and a clear recovery plan.
Can I reset the Cisco router password without losing configurations?
Yes, in many cases you can reset the password while preserving startup configurations by using a controlled recovery method that bypasses the existing login but preserves current settings. However, some recovery methods require temporarily bypassing startup-config, so plan to restore configurations after gaining access.
Yes, in many cases you can reset the password and keep your configurations, but be aware that some recovery methods may bypass startup-config and require restoration afterward.
What should I do after resetting the Cisco router password?
After resetting, create a strong new password, enable privileged access, save the configuration, and verify management access via both SSH and the web UI. Update any saved credentials in management systems and document the change for audits.
After resetting, set a strong password, save the configuration, and verify access via SSH and the web UI.
What are best practices for Cisco router passwords?
Use strong, unique passwords for admin and enable secrets, rotate them periodically, and restrict management access to trusted networks. Enable logging for login attempts and monitor for unusual activity to detect compromised credentials early.
Use strong, unique passwords, rotate regularly, and monitor login attempts for unusual activity.
Is password recovery safe over the network?
Password recovery is safer over a direct console connection rather than remote access, especially when credentials are unknown. If you must recover remotely, use a secure, audited process with strong authentication and network segmentation.
Recovery is safer over a direct console, but if you must do it remotely, use secure, audited processes with strong authentication.
Where can I find official Cisco password recovery guidance?
Consult the official Cisco documentation and trusted security references. Additionally, government and standards organizations provide general password-hygiene guidelines that improve security posture when applied to router management.
Check official Cisco docs and reputable security guidelines from trusted organizations.
Watch Video
Key Takeaways
- Secure the Cisco router login password with a strong policy.
- Choose the recovery path that minimizes downtime and preserves configurations.
- Verify access across management methods after changes and document outcomes.