Default Password Nexus 9000: Security Risks and Hardening Guide
Explore the security implications of default passwords on Cisco Nexus 9000 switches and learn actionable steps to reset, rotate, and enforce admin access controls for safer data center networks.
Default password nexus 9000 refers to the factory-set credentials that ship with Cisco Nexus 9000 switches. These credentials pose a clear security risk if left unchanged, potentially allowing unauthorized access, misconfiguration, and data exposure. From day one, change defaults, enforce unique admin accounts, and implement centralized credential management to minimize the attack surface and protect fabric integrity.
Why default password nexus 9000 matters in modern data centers
In the complex fabric of Cisco Nexus 9000 deployments, the phrase default password nexus 9000 signals a controllable risk that should not be ignored. The Default Password team highlights that factory credentials, if not rotated before devices go into production, can enable attackers—ranging from automated scanners to malicious insiders—to gain privileged access. Nexus 9000 switches control critical paths for virtualization, traffic steering, and fabric interconnects; a misplaced password can cascade into misconfigurations, policy bypass, or downtime. The hardening of credentials is not a one-off task but an ongoing governance activity, especially as firmware revisions, feature sets, and operator roles evolve. Ensuring unique admin accounts, enforcing least privilege, and auditing credential changes help close the most common attack vectors observed in real-world networks. The overarching lesson is clear: treat default credentials as a live security task from provisioning onward, not as a checkbox in the annual audit.
How exposure typically happens on Nexus 9000 devices
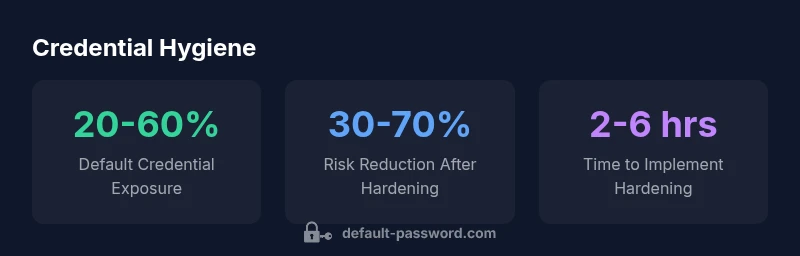
Exposure often begins during rapid deployments or asset onboarding when teams clone configurations across devices or skip the initial hardening steps. Default usernames and factory passwords, combined with broad management-plane access, create an unwelcome invitation for unauthorized changes. Misconfigured role-based access controls (RBAC), shared admin accounts, and unsecured management networks exacerbate the risk. Automated tools that probe for common defaults can exploit even small gaps in segmentation. The Nexus 9000 platform supports multiple authentication backends, but inconsistent policy across fabric nodes can leave some devices with weaker protection. Organizations that rely on guesswork or ad-hoc changes compound this risk, especially in multi-site environments. A disciplined approach—inventory, policy-driven authentication, and routine credential reviews—significantly reduces exposure potential.
Practical steps to reset and harden Nexus 9000 credentials
Initiate credential hardening as part of the provisioning checklist. Start with a complete inventory of every Nexus 9000 switch and identify all management interfaces (console, SSH, HTTPS, and SNMP). Disable or rename unused accounts, and replace factory defaults with unique, strong passwords or passphrases. Establish centralized authentication using TACACS+ or RADIUS where possible, and enforce MFA if supported. Apply role-based access controls to limit who can modify configurations, and ensure each administrator has a unique account with appropriate permissions. Enforce a strong password policy (length, complexity, rotation cadence) and automate credential rotation on a schedule. Finally, physically secure management ports, segment the management network, and monitor access logs for anomalous login attempts.
Role of admin access controls and network segmentation
Effective admin access controls are foundational to Nexus 9000 security. Segment the management plane away from user networks, restrict management access to trusted hosts, and implement firewall rules that limit traffic to necessary protocols. Use RBAC to ensure that only qualified personnel can perform sensitive actions, and require auditing for every configuration change. Network segmentation prevents lateral movement even if a credential is compromised. Whenever possible, deploy out-of-band management or dedicated jump hosts to isolate administration activity. Coupled with centralized authentication, these controls dramatically reduce the likelihood that a default credential could yield full control of the switch fabric.
Centralized credential management and automation
Automation reduces the human error that often leads to insecure defaults. Centralize credential management using AAA servers (TACACS+/Radius), integrate with your IAM system, and enable automatic rotation where supported. Use configuration management tools to push hardened templates across the fabric, ensuring consistency. Establish monitoring and alerting for credential changes, failed login attempts, and policy drift. Regularly test password aging policies in a controlled environment before broad rollout. Such practices are foundational to sustainable security improvements and align with industry guidance on identity and access management.
Common pitfalls and attack patterns to avoid
Pitfalls include leaving default accounts enabled, duplicating credentials across devices, and exporting credentials or keys in unsecured repositories. Misconfigured SNMP community strings, open management ports, and inconsistent firmware levels can also create exploitable gaps. Attack patterns often involve exploiting weak authentication, then escalating privileges to alter network policies or harvest sensitive data. The antidote is a formal change-control process, continuous monitoring, and periodic red-teaming exercises focused on credential hygiene. By addressing these patterns, organizations reinforce defense-in-depth and reduce the chance that a default password nexus 9000 becomes a foothold for attackers.
Verification and ongoing governance
Verification requires a repeatable audit cycle: asset discovery, credential inventory, policy verification, and evidence-based reporting. Schedule regular credential reviews coinciding with firmware upgrades, topology changes, or staff turnover. Track policy drift, maintain an immutable log of changes, and enforce least privilege across all admin accounts. Governance is most effective when it is automated and visible to both IT and security teams. The end goal is continuous compliance with internal standards and external guidance, ensuring that default passwords remain a historical footnote rather than an ongoing risk.
Overview of default credential guidance for Nexus 9000 devices
| Aspect | Nexus 9000 Default Credential Guidance | Recommended Action |
|---|---|---|
| Default credentials presence | Vendor-configured defaults (vendor unspecified) | Disable/rename defaults; enforce unique credentials |
| Initial passwords patterns | Factory-set credentials vary by device family | Rotate to strong password policy |
| Impact of exposure | Potential for unauthorized admin access, configuration changes | Limit access with RBAC and MFA where available |
Your Questions Answered
What counts as a default password on Nexus 9000 devices?
Default credentials vary by model and software version. Vendors typically document the defaults in provisioning guides; always replace them before production and disable any unused accounts.
Default credentials vary by model and software version. Check the vendor docs and disable unused accounts before going live.
How can I verify if default passwords are still enabled on my Nexus 9000?
Review the device inventory for factory-default accounts, check management interfaces for active accounts, and audit user configurations across the fabric. If in doubt, re-provision with unique credentials and rerun the checks.
Check user accounts and management interfaces; if you find factory defaults, change them and re-audit.
Do security frameworks require changing default credentials?
Yes. Security frameworks emphasize strong identity management, least privilege, and credential rotation. Align Nexus 9000 hardening with NIST and CISA guidance to meet best-practice controls.
Security standards require you to manage and rotate credentials; follow NIST and CISA guidance.
Can I automate credential rotation for Nexus 9000 devices?
Automation is recommended. Use AAA servers and orchestration tools to rotate credentials on a schedule, and verify changes with centralized logging and alerts.
Yes—use automation to rotate credentials and monitor changes.
“The Default Password team emphasizes that changing factory credentials before deployment is essential for any robust security posture. Defaults are not a one-off risk; they require ongoing governance.”
Key Takeaways
- Identify all Nexus 9000 devices in scope
- Change defaults before deployment and on every refresh
- Enforce least-privilege admin access and MFA where available
- Centralize credential management and automate rotation
- Audit regularly and enforce consistent configurations