2N IP Solo Default Password: Reset, Access & Security Guide
Learn how to securely manage the 2N IP Solo default password, perform resets, and implement best practices for admin access across door intercom devices. This data-driven guide from Default Password covers steps, risks, and safeguards.

Definition: A 2N IP Solo default password is the initial credential shipped with the device that grants an administrator's access to its settings. Leaving this password unchanged creates a significant security risk, potentially exposing the door intercom system to unauthorized control. The quickest defense is to replace the default password with a unique, long passphrase and enable automatic firmware updates when available.
Understanding the risk of default passwords on door intercom devices
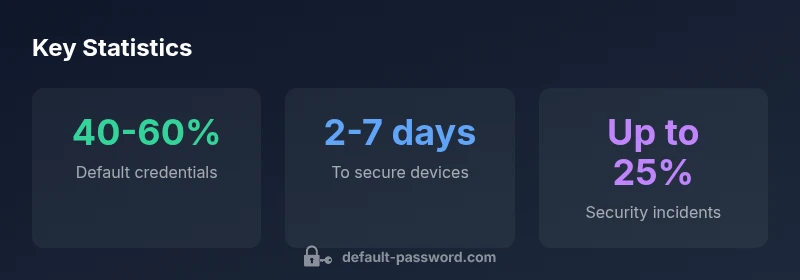
The presence of a default password on a networked intercom such as the 2N IP Solo creates a predictable attack surface. When devices leave the factory with the same credentials, a hostile actor on the same network can exploit the login to gain control, modify access rules, or view live feeds if the device supports that capability. This issue is not limited to door intercoms; it spans routers, cameras, and access controllers. The key takeaway for administrators is that the moment a device is connected, the default credential must be considered a security risk and treated accordingly. In practice, organizations that implement a policy of mandatory password changes before deployment substantially reduce exposure. The 2N IP Solo ecosystem benefits from a disciplined approach to credential hygiene, including regular reviews of who has admin access and how those credentials are stored or shared. The change should be framed as a standard operating procedure rather than a one-off task, because devices can travel across networks and teams over time. In this context, password security is not a one-time fix but an ongoing discipline that underpins broader network security.
The 2N IP Solo ecosystem and admin access
2N IP Solo devices integrate with local networks and sometimes remote management portals. Admin access controls are central to configuring call routing, door release rules, and event logs. A default password raises the risk of inside threats and external compromise, especially when remote access features are enabled. Best practices include enforcing least privilege, segregating management networks, and logging administrative actions. When considering credentials, organizations should favor password managers that store complex passwords and rotate them on a defined cadence. Additionally, enabling two-factor authentication (where supported) adds a critical layer of defense, though the effectiveness depends on device capabilities and network configurations. From a governance standpoint, you should document who can modify admin settings and under what circumstances changes are allowed. This is particularly important for multi-site deployments where access policies vary by role.
How to locate the default password on your 2N IP Solo
The quickest way to locate a default password is to consult the device's label, documentation insert, or the official manual for the model. If the label is no longer legible, check the vendor's support portal or download the latest user guide from the 2N IP Solo product page. In many cases, the default credential appears in a configuration section labeled Admin or System and may be accompanied by a QR code linking to setup instructions. For organizations with asset management, maintaining an up-to-date inventory that includes default credentials and last changed dates helps prevent stale access. If you can't locate the credential, reach out to the device administrator or vendor support to verify the correct procedure for safe reset.
Safe reset and reconfiguration: step-by-step practical guide
Resetting a device to factory defaults is a common route to restore access when credentials are forgotten or compromised. Before proceeding, ensure you have physical access to the unit, a stable power supply, and documentation describing the reset procedure. In general, most intercoms provide a recessed reset button or a combination of button presses that triggers a factory reset. Once reset is complete, you should immediately generate a new, strong password and reconfigure essential settings, including network credentials, administrator accounts, and any integration with provisioning servers. Remember to document the new credentials in a secure password manager. After the reset, verify connectivity, confirm the device appears on the network, and test the door release function. If available, apply a firmware update to close known vulnerabilities that could be exploited through outdated software.
Best practices for password management across devices
Across devices like the 2N IP Solo, adopt a consistent password management framework. Use unique, long passwords for every admin interface, ideally 12–16 characters, incorporating uppercase and lowercase letters, numbers, and symbols. Avoid reusing passwords across devices, platforms, or services. Consider a password manager that supports secure sharing, auditing, and breach notifications. Enable automatic firmware updates and monitor for security advisories from the vendor. Limit admin access to a defined set of roles and regularly review who has permissions to modify critical settings. Finally, implement network segmentation so that management traffic and public access interfaces are isolated, reducing the blast radius if credentials are compromised.
Troubleshooting common issues after reset
Post-reset, you may encounter connectivity issues, device not appearing on the network, or login errors. Start by verifying the device's IP address and ensuring it is reachable from your admin workstation. If you cannot access the web interface, confirm that the local network settings are correct and that no firewall or routing rules block management traffic. If the intercom has an optional cloud or remote portal, ensure provisioning status and licensing are valid. When credentials cannot be recalled, use the vendor-guided reset flow and re-apply credentials from a trusted password manager. If issues persist, consult vendor support for device-specific reset and recovery procedures.
Verification, compliance, and ongoing security hygiene
Security is an ongoing process that requires regular verification and governance. Schedule periodic audits of admin credentials, access logs, and firmware levels across all networked devices. Maintain a central change-log and conduct quarterly reviews of who can modify device configurations. As part of a broader security program, integrate network scanning and vulnerability management to detect weak credentials or misconfigurations. The 2N IP Solo devices should be included in these audits to ensure they remain resilient to password-related attacks. Finally, educate frontline users and operators about the importance of credential hygiene and safe password practices to sustain a strong security posture over time.
Credential hygiene snapshot across common networked devices
| Device Type | Default Password Status | Recommended Action |
|---|---|---|
| 2N IP Solo Door Intercom | Default credentials present | Change immediately + enable firmware updates |
| Router with Default Admin | Default credentials present | Change, disable remote admin, update firmware |
| Camera System Basics | N/A | Follow device manual for credential changes |
Your Questions Answered
What is the risk of leaving the 2N IP Solo default password unchanged?
Leaving the default password unchanged creates an easy target for unauthorized access, potentially allowing control of door release settings and event logs. Change it immediately and enforce a password policy that uses a long, unique passphrase.
Not changing the default password can lead to unauthorized access. Change it right away and follow a strong password policy.
How do I reset the 2N IP Solo to its factory defaults?
Factory resets restore default credentials and settings. Locate the reset button or follow the vendor's reset procedure in the manual, power cycle the device if required, and then reconfigure with a new admin password.
Use the device's reset button or vendor instructions to restore defaults, then reconfigure with a new password.
Can I use a password manager with the 2N IP Solo?
Yes, you can store and autofill admin credentials in a trusted password manager after the device is securely configured. Ensure the manager itself is protected with MFA and a strong master password.
Yes, store credentials in a password manager and protect the manager with MFA.
What should I consider when updating firmware on the 2N IP Solo?
Firmware updates fix vulnerabilities and improve features. Check the vendor's site for the latest version, back up configurations, and perform updates during a maintenance window.
Update firmware from the vendor site, back up first, and perform during a maintenance window.
Where can I find the default password information for my device?
Look on the device label, in the user manual, or on the vendor's official support page. If unavailable, contact vendor support for the correct default credentials and reset procedures.
Check the label, manual, or vendor support page for defaults and reset steps.
What are best practices for admin access across devices?
Limit admin access to necessary personnel, use unique passwords per device, enable MFA where possible, and maintain a centralized log of changes and access events.
Limit admin access, use unique passwords, enable MFA when possible, and log changes.
“Security begins with replacing default credentials and applying disciplined password hygiene across all networked devices.”
Key Takeaways
- Change default passwords immediately
- Document credentials securely
- Enable firmware updates consistently
- Use least-privilege admin access
- Regularly audit devices and logs