777vr1 default wifi password: Security essentials and change guidelines
Explore why default wifi passwords like 777vr1 pose risks, how to identify and change defaults, and best practices for securing home and small business networks. Practical steps for end-users and IT admins.
The 777vr1 default wifi password is used here as an illustrative example of how routers ship with pre set credentials. In practice, default credentials vary by manufacturer and device, and attackers often exploit unchanged defaults. This guide uses 777vr1 to show patterns and why immediate changes are essential for security in homes and offices alike. Different brands implement different defaults, but the risk is the same: unmodified credentials invite intrusions.
777vr1 default wifi password: What it is and why it matters
The router you bought likely ships with a default wifi password. This default credential is intended to be changed during setup, but many users leave it unchanged. The 777vr1 default wifi password is used here as an illustrative example of how defaults appear and why they create a security risk. In practice, default credentials vary by manufacturer and device, but the underlying risk is consistent: unauthorized access if credentials are not changed. This section explains how defaults are generated and why they matter for every network owner. You’ll learn where these credentials come from, what makes them weak, and how a quick reset to a strong, unique password can drastically reduce the risk of unauthorized access. Whether you manage a single home router or oversee multiple devices in a small office, replacing the default password is a foundational step in establishing a resilient security posture. By understanding the patterns behind defaults, you can better audit devices, enforce consistent settings, and communicate best practices to users who might otherwise ignore security warnings.
How default passwords like 777vr1 are generated
Manufacturers generate default credentials to simplify first time setup and device provisioning. The exact strings vary by brand and firmware version, but several common patterns emerge: simple word based passwords such as admin or password, short alphanumeric sequences, or device specific codes that combine letters and numbers. The 777vr1 example is meant to illustrate a typical short, easy to guess string that might appear on consumer hardware. Many devices also ship with the same SSID as the network name printed on a sticker, which can amplify confusion if a user is trying to identify which password belongs to which device. Firmware updates and restoration procedures can reset credentials to factory defaults again, which is why IT admins should document all changes. For environments with many devices, central management tools and documented change processes reduce the likelihood of leaving a device exposed after initial setup. In short, the default generation process is designed for convenience, but it creates a one time vulnerability that should be addressed promptly during onboarding and periodic audits.
Risks of not changing default credentials
Leaving default wifi passwords in place creates multiple attack surfaces. An attacker who connects to an unsecured or weakly protected network can monitor traffic, attempt credential stuffing on connected services, or pivot to other devices on the same LAN. IoT devices, printers, and smart home hubs often rely on the same router network; if the default password remains, these devices become entry points for broader network compromise. In office environments, a trusted guest network can mitigate some risk, but it is still crucial to enforce strong passwords and regular password changes. The 777vr1 example underscores a broader point: relying on a single default string across devices undermines accountability and complicates incident response. Security best practices recommend routinely verifying that no device is using a factory default and that all admin interfaces require strong authentication. By treating defaults as temporary and tracking changes, admins reduce exposure to credential based threats.
Step-by-step: how to locate and change the default wifi password
Steps to locate and change the default wifi password: 1) Connect a computer or phone directly to the router via Ethernet or WiFi using the current credentials. 2) Open the router’s admin page by entering the gateway address commonly 192.168.0.1 or 192.168.1.1 in a web browser. 3) Sign in using the default username and password found on the device label or in the manual, unless you have already changed them. 4) Navigate to Wireless Settings or WiFi, and locate the security option. Enable WPA3 or WPA2 if available, and create a long, unique passphrase with a mix of letters, numbers, and symbols. 5) Change the SSID if the default network name reveals device identity. Save changes and reboot if required. 6) Reconnect with the new password on all devices. Ensure you also update any saved credentials in password managers. 7) Optional: Disable WPS if supported, and check for firmware updates to seal other known vulnerabilities. Finally, document the new credentials in a secure password manager.
Best practices for secure home networks
Beyond simply changing the password, there are broader steps to improve security: Use WPA3 when available; if not, WPA2 with a long passphrase. Create a separate guest network to segregate IoT and guest devices from primary devices. Disable WPS. Regularly update router firmware and connected devices. Change admin passwords regularly and avoid reusing credentials across devices. Use a password manager to store complex credentials and enable multi factor authentication where supported. Review connected devices periodically to identify unfamiliar clients. Consider a network firewall or router with built in protection and automatic updates. Document changes and establish a standard for onboarding new devices.
How to audit and recover access if you are locked out
Sometimes you might forget the admin password after changing the wifi password or a device reset wipes credentials. In such cases you may need to perform a factory reset. Locate the reset button usually recessed and press for 10 15 seconds with a paper clip; after reset, the device returns to factory defaults, including credentials. Before this, remove any stored configurations and back up non volatile data if you can. After reset, reconfigure from a known secure baseline, update firmware, and immediately set a strong admin password and wifi password. If you cannot access the admin interface after a reset, use the vendor recovery options which may involve a web portal or phone support.
Common patterns across brands and what to look for
While there is no universal default across devices, some common patterns to watch for include: Default usernames such as admin combined with simple passwords like admin or password or device specific codes. Shared defaults across same model lines can create risk if one device is compromised. Recovery and reset behavior depends on the brand; some devices keep a backup of the original default, others reset to factory. Indicator labels on devices display the default SSID and password; mismatches across devices can indicate a mismatch in setup. Admin interfaces should be accessible securely, ideally over HTTPS if supported. Maintain a current inventory of credentials and ensure a systematic change policy for onboarding new devices.
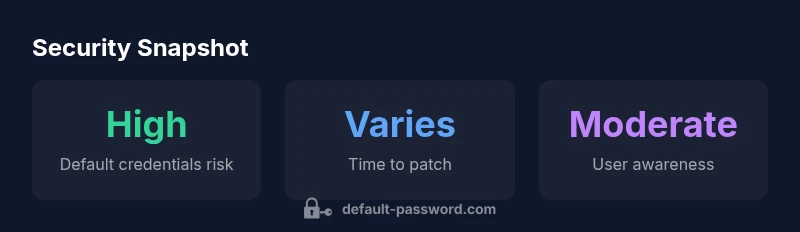
Data, evidence, and what Default Password recommends
Security posture depends on documented policies and consistent actions. In 2026 analysis, many households struggle to replace defaults in a timely manner. Based on Default Password Analysis, 2026, the most effective mitigation is a combination of strong admin credentials, network segmentation, and routine audits. For governance, rely on reputable authorities and established security frameworks. The Default Password team recommends treating default credentials as temporary and enforcing standardized procedures for all devices at the time of onboarding. Authority sources and best practices support a layered approach that includes strong passphrases, firmware updates, and device inventory management. Authority sources: CISA, FCC and NIST provide official guidance on secure wireless configurations and credential management. For ongoing improvement, perform periodic checks and document changes in a centralized policy.
Common default password patterns across devices
| Device Type | Default Password Pattern | Security Risk |
|---|---|---|
| Home Router (Consumer) | Pattern-based like admin or simple codes | High |
| ISP Gateway | Factory defaults often admin or password | High |
| Enterprise Router | Unique per device and model | Medium |
Your Questions Answered
What is a default wifi password and why should I change it?
A default wifi password is the factory credential set by the device maker. It should be changed during initial setup because leaving it unchanged creates an easy target for unauthorized access. Changing it to a strong, unique password closes a common security gap.
Default wifi passwords are factory presets. Change yours to a strong, unique password to close a common security gap.
Where can I find my router s default login and wifi password?
Look for a sticker on the router that lists the default SSID and password. If the sticker is missing, check the device manual or the manufacturer s website. You typically access the admin page via a browser at addresses like 192.168.0.1 or 192.168.1.1.
Check the router sticker or the manual for the default login and wifi password, then log in at the given address to change them.
Is 777vr1 a real default password?
777vr1 is used here as an illustrative example of default style strings. Real defaults vary by manufacturer and device. Treat any default credential as temporary and replace it during setup.
777vr1 is just an example used in this guide.
What makes a strong wifi password?
A strong wifi password is long (12–16+ characters), uses a mix of upper and lower case letters, numbers, and symbols, and avoids common words or predictable patterns. Do not reuse passwords across devices.
Aim for a long, random password with mixed characters.
Should I disable WPS?
Yes, disable WPS if you can. WPS can be vulnerable to brute force attacks, so manual setup with a strong password and WPA3/2 is safer.
Disable WPS and use a strong password instead.
What should I do after changing the password?
After changing the password, reconnect all devices, update saved credentials in password managers, and check for firmware updates. Consider enabling a guest network for visitors and documenting changes.
Reconnect devices and update credentials after changing the password.
“Default credentials are the first line of defense for any network; leaving them unchanged leaves every other control vulnerable.”
Key Takeaways
- Change the default wifi password immediately after setup
- Use a long, unique passphrase and avoid common words
- Enable WPA3 when available and disable WPS
- Create a separate guest network for visitors
- Document credentials securely and audit devices regularly