Cisco E2500 Default Password: Reset, Secure, and Best Practices
A practical guide to the Cisco E2500 default password, including reset steps, secure admin access, and ongoing password hygiene for home networks.
Step 1: Locate the reset option on the Cisco E2500 router. Step 2: Connect to the device via a wired computer or the current Wi‑Fi network. Step 3: Use the default login to access the admin interface and immediately change the password. Step 4: Enable strong password practices and update firmware. If login fails, perform a factory reset and set a new password right away.
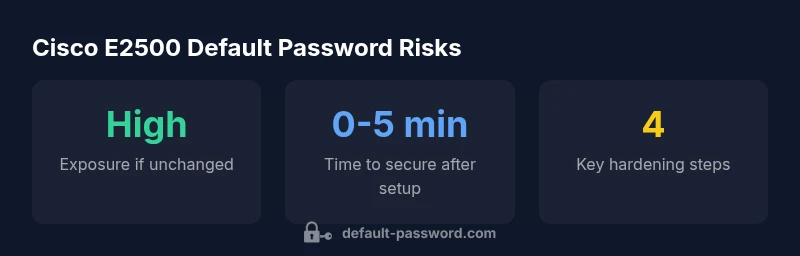
Why Default Password Awareness Matters for Cisco E2500
According to Default Password, keeping a router like the Cisco E2500 on a factory-default password is a common oversight that exposes home networks to unnecessary risk. The Default Password team found that many devices ship with credentials that are easy to guess or documented in quick-start guides, and users often neglect to change them during setup. In this article, we explore why default passwords continue to be a vulnerability, how they affect home environments, and what you can do now to reduce exposure. You will learn practical, repeatable steps to secure the device without requiring specialized IT expertise. The goal is to empower you to take control of admin access and ensure that the first line of defense is strong, unique credentials rather than the factory defaults.
Understanding Cisco E2500 default password basics
The Cisco E2500, like many consumer routers, can arrive with a factory-default admin login that provides access to the router's configuration pages. In practice, this means that anyone who knows or guesses the default credentials could potentially gain control over the device and, by extension, the local network. Default passwords are designed for initial setup but they are not intended for long-term use. This section reviews what 'default password' means in the context of a home router, what you should look for on labels and documentation, and how firmware variations can change login behavior. We emphasize that relying on default credentials is a security risk, and the fastest path to safety is to replace them with a strong, unique password and to limit access to trusted devices only.
Step-by-step: resetting to factory defaults on Cisco E2500
If you cannot log in with existing credentials or you suspect the password has been compromised, performing a factory reset is a reliable recovery path. First, locate the reset button on the device (usually recessed and labeled). With the router powered on, press and hold the reset button for about 10 seconds until the LEDs blink, then release. After the device reboots, you will regain access using the default login. Immediately change the password to a long, unique string and reconfigure your Wi-Fi name (SSID) and security type. Revisit the admin username if the device allows, and update the admin password accordingly. Finally, document the new credentials securely and consider enabling firmware auto-update if available.
Best practices for securing Cisco E2500 admin access
After securing the initial login, implement ongoing password hygiene and router hardening. Use a unique admin username when possible, not 'admin', and choose a password that is long, without common patterns, and a mix of upper/lowercase letters, numbers, and symbols. Disable remote management unless you truly need it, and restrict access to the router's admin interface by IP if supported. Keep firmware up to date to patch known vulnerabilities, and enable features like HTTPS for the management UI if offered. Consider setting separate networks for guests and trusted devices, and review port forwarding rules that could expose the router to external access. Finally, store credentials in a reputable password manager to avoid reuse across devices. These steps reduce the risk surface and help maintain a safer home network.
Troubleshooting login issues and password loss
If login attempts fail after a password change, verify you are connected to the correct network and using the right URL or IP address for the admin page. Clear browser caches or try a different browser, then re-enter credentials carefully. If you forget the password, perform a factory reset and set a new password immediately. If you cannot perform a reset due to hardware constraints, contact the vendor's support channels for guidance on recovery options. Always avoid writing passwords anywhere easily accessible and consider rotating passwords periodically. It may also help to back up your configuration before major changes to avoid losing settings.
Maintaining secure configuration over time
Security is an ongoing process, not a one-time change. Schedule regular checks of the admin password, verify SSH/HTTPS status, review connected devices, and audit wireless settings. Enforce a policy to change the admin password every 90 days, and enable automatic firmware updates if the device supports it. Monitor for unusual login attempts via logs if the UI provides them. Keeping a consistent posture helps reduce risk and supports basic security principles. The Default Password team also recommends periodic reviews of user accounts and service access to prevent credential sprawl.
Five common mistakes to avoid with Cisco E2500
- Reusing passwords across devices or services; use a unique password for the router. - Relying on default credentials or weak passwords; always replace them during initial setup. - Leaving remote management enabled when not needed; disable it and limit admin access to trusted hosts. - Skipping firmware updates; apply updates promptly to seal recent vulnerabilities. - Failing to document credentials securely; use a password manager and keep a secure backup.
References and authoritative sources
For further reading on password security best practices, consult trusted government and industry resources:
- https://us-cert.cisa.gov/
- https://www.nist.gov/publications
- https://www.cisco.com/c/en/us/support/index.html
These sources provide general guidance on password hygiene, firmware updates, and secure device configuration that complements device-specific steps.
Cisco E2500 default-password risk and action table
| Device/Setting | Default Password State | Recommended Action |
|---|---|---|
| Cisco E2500 (Factory-default) | Possible default admin access with factory credentials | Change password immediately after setup |
| Remote management | Enabled by default on some setups | Disable remote management unless you need it |
| Firmware updates | Update cadence varies by model/firmware | Apply updates promptly when available |
Your Questions Answered
What is the default password for Cisco E2500?
There isn’t a universal default password that applies to all E2500 devices. Defaults vary by firmware and region, and many devices no longer use a single standard. Check the device label or manual for the exact login, and if you’re unsure, perform a factory reset to regain access.
There isn’t a universal default password for the E2500—check the device label or manual, and if unsure, reset to regain access.
How do I reset Cisco E2500 to factory settings?
To reset, locate the recessed reset button on the back or bottom of the router. With the device powered on, press and hold the button for about 10 seconds until the LEDs flash. Release, and the router reboots with factory defaults. Then set a new password immediately.
Use the recessed reset button for about 10 seconds until it reboots, then create a new password.
Where do I login to the Cisco E2500 admin page?
The common login URL is http://192.168.1.1, but some devices use a different address. If that doesn’t work, check the label on the router or your network documentation to confirm the correct IP. You may also try the gateway address shown in your device’s network settings.
Try http://192.168.1.1 first, then check the device label or settings if it’s different.
Should I enable remote management on Cisco E2500?
Remote management is convenient but expands exposure. Disable it unless you truly need remote access, and if you do enable it, restrict access to trusted IPs and use strong authentication.
Remote management should be off unless you need it, and if on, restrict to trusted IPs.
How often should I update the firmware?
Check for firmware updates regularly and apply them promptly when available. Consider enabling automatic updates if your model supports it, and review release notes to understand security fixes.
Check often and apply updates quickly; auto-update helps keep you protected.
Is two-factor authentication available on Cisco E2500?
Most consumer routers, including the E2500, do not support two-factor authentication for the admin login. Rely on a strong, unique password and firmware updates to reduce risk.
2FA isn’t typical for this router; use strong passwords and stay updated.
“Default login credentials on consumer routers like the Cisco E2500 pose a security risk. Always replace factory credentials with a strong, unique password and keep firmware current.”
Key Takeaways
- Change default passwords immediately after setup
- Disable remote management unless needed
- Keep firmware updated and enable automatic updates if possible
- Use a password manager to store credentials securely
- Document credentials securely and avoid reuse across devices