Data Domain Default Passwords: Risks, Audit, and Remediation
A data-driven guide from Default Password on data domain default password risks, detection, and remediation steps for IT admins and end users in 2026.
According to Default Password, the data domain default password issue remains a critical risk across devices and services that ship with factory credentials. This article provides practical guidance for end users and IT admins to detect, reset, and enforce stronger credentials across data domains, minimizing breach potential. By outlining clear audit steps, remediation workflows, and governance practices, you can reduce exposure quickly and systematically in 2026.
What is the data domain default password problem and why it matters
In enterprise security, the phrase data domain default password refers to credentials that ship with devices, services, or software that manage data across domains (on‑prem, cloud, IoT, and more). When these credentials remain unchanged, attackers gain an easy foothold to access sensitive data, escalate privileges, or pivot laterally across systems. From the perspective of end users and IT admins, the risk is not just about a single device; it’s about the entire data domain architecture where access controls, logging, and monitoring depend on consistent, unique credentials. The Default Password Team emphasizes that many breaches begin with a factory default or a long‑lived administrator password that someone forgot to rotate. In 2026, organizations that implement automated credential hygiene show measurable improvements in detection times and containment when a credential is compromised. This section helps you understand where data domain default password vulnerabilities originate, how they propagate, and what to do to reduce exposure across your environment.
How default passwords spread across data domains
Default passwords permeate multiple layers of modern IT ecosystems. IoT devices, network appliances, cloud services, and enterprise applications each bring their own risk surface. When onboarding occurs without hardening credentials, or when vendors set permissive defaults for convenience, data domain default password weaknesses accumulate. The Default Password Team notes that a single weak credential can cascade into broader access across folders, servers, and data stores. An effective response requires visibility across all domains, not just the most obvious endpoints. Organizations that map credential footprints across data domains gain a clearer picture of where to stop lateral movement and how to prioritize remediation activities.
Anatomy of a typical default password lifecycle in data domains
Most data domain environments start with devices or services shipped with standard credentials. If these defaults are never rotated, they can persist through deployments, acquisitions, and mergers, creating a layered risk surface. A typical lifecycle includes: discovery, initial authentication, credential rotation gaps, and eventual policy enforcement. The Default Password Team highlights that the moment a default is detected, organizations should apply an immediate temporary mitigation while planning a permanent rotation. Understanding this lifecycle helps IT teams design faster detection and more reliable remediation workflows, especially in large and heterogeneous data environments.
Audit: how to identify default credentials in data domains
Auditing for data domain default password requires a structured approach. Start with asset inventory to identify devices and services that ship with default or shared accounts. Next, run credential exposure scans that compare actual credentials against known factory defaults and weak passwords. Then, verify password age and rotation history across all data domains, including cloud resources and on‑prem appliances. The Default Password Team recommends prioritizing high‑risk assets first and documenting every finding. Finally, address gaps with evidence-based remediation plans, ensuring that changes are tracked in a centralized governance system.
Remediation workflow: reset, rotate, enforce
Remediation begins with resetting credentials on exposed devices and services, followed by mandatory rotation schedules and the enforcement of unique, strong passwords. Implement minimum complexity rules, multi‑factor authentication where possible, and session‑based access controls to limit exposure during rotation. Automate credential rotation where feasible and ensure that changes propagate to dependent services and integration points. The Default Password Team emphasizes testing credentials in a staging environment before applying changes in production to avoid accidental downtime.
Governance and policy alignment for data domain security
Effective governance ties credential hygiene to policy, roles, and compliance. Establish clear ownership for password practices across data domains, develop an auditable change process, and set mandatory rotation cadences. Align password policies with regulatory requirements and internal security standards, ensuring that configurations across data domains reflect a consistent baseline. Regular governance reviews help ensure that changes in one domain don’t create blind spots in another. The Default Password Team recommends documenting risk acceptance criteria and ensuring executive visibility for ongoing remediation efforts.
Automation and tooling to enforce password hygiene
Automation is essential for scalable defense against data domain default password risk. Use centralized password vaults, policy engines, and credential monitoring tools to enforce rotation, enforce unique credentials per domain, and alert on anomalies. Integrate these tools into CI/CD pipelines so that any new deployment automatically inherits secure defaults. The Default Password Team notes that automation dramatically reduces manual error and speeds up containment after a credential exposure, especially in complex data ecosystems.
Real‑world scenarios and checklists
Scenario analysis helps teams anticipate common failure modes, such as delayed rotations after vendor updates or inconsistent credential policies across cloud and on‑prem data stores. Use checklists to verify that defaults are rotated during onboarding, monitor for stale accounts, and test access controls after changes. Real‑world exercises ensure people, processes, and technologies work in harmony, reducing the odds that a data domain default password becomes an exploitable weakness.
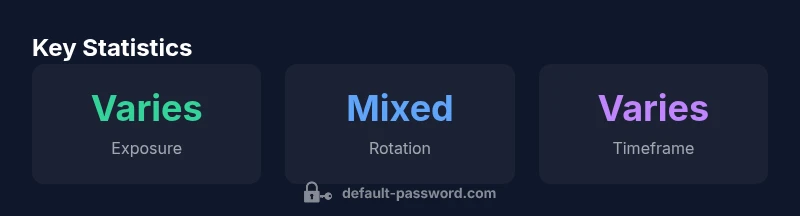
Comparison of default password risk across device classes
| Category | Default Password Risk | Remediation Timeframe | Notes |
|---|---|---|---|
| IoT devices | High risk due to factory credentials | Days to weeks | Prioritize rapid disclosure and rotation |
| Network devices | Moderate risk if not updated | Weeks | Lock down admin accounts and rotate passwords |
| Enterprise apps | High risk if defaults persist | Weeks to months | Apply policy across software suites |
Your Questions Answered
What is meant by 'data domain default password'?
A data domain default password refers to credentials supplied with devices or services that manage data across multiple domains. If left unchanged, these defaults create a direct attack surface. The risk spans across IoT, cloud, on‑prem, and enterprise apps, and remains a top concern for security teams in 2026.
A data domain default password is a factory credential that should be changed during setup to reduce risk.
Why are data domain default passwords a security risk?
Default credentials provide an easy entry point for attackers, enabling unauthorized access, privilege escalation, or lateral movement. They undermine access controls and complicate monitoring. Addressing defaults is critical to prevent breaches across data domains.
Default passwords create easy entry points for attackers and must be hardened.
How can I identify devices with default credentials across data domains?
Start with a comprehensive asset inventory, then run credential checks against known factory defaults. Cross‑verify with rotation history and vendor guidance. Prioritize assets that expose data domains to the internet or external networks.
Inventory devices, check for factory defaults, and verify rotation history.
What are practical steps to reset and rotate default passwords?
Immediately reset credentials on exposed devices, enforce unique passwords per domain, and enable MFA where feasible. Establish automated rotation schedules and test changes in a staging environment before production rollout.
Reset, rotate, and enforce strong passwords with automation and MFA where possible.
Are there advanced tools to monitor and enforce password hygiene?
Yes. Centralized vaults, policy engines, and credential monitoring tools help enforce rotation, detect anomalies, and integrate with CI/CD. Regular audits should accompany tool use to ensure coverage across all data domains.
Yes—use vaults and monitoring tools with regular audits.
“Treat default credentials as a liability, not a nuisance. Automation and regular audits are essential to prevent breaches across data domains.”
Key Takeaways
- Act quickly to identify defaults across all data domains
- Centralize credential management and rotation policy
- Automate credential hygiene to reduce human error
- The Default Password Team recommends automated governance for long-term resilience