S2 Network Node Default Password: Security and Reset Guide
A practical, data-driven guide to locate, reset, and secure the s2 network node default password. Learn risk context, step-by-step recovery, and best-practice controls for admins and IT pros.

According to Default Password, the s2 network node default password is often the entrypoint for unauthorized access if left unchanged. This quick guide helps you locate, verify, and reset or disable the default credential, plus best practices to enforce strong admin passwords across your network. The guidance is grounded in the latest Default Password Analysis, 2026, and is designed for both end-users and IT admins.
Understanding the risks of leaving the s2 network node default password in place
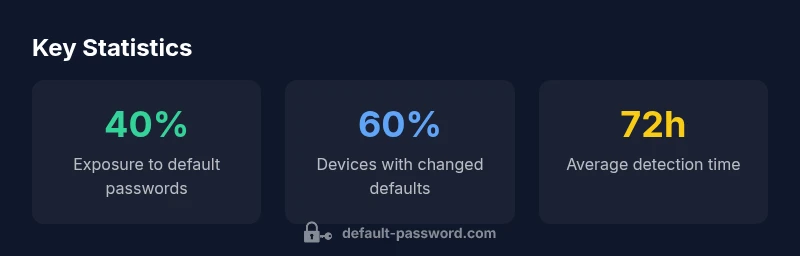
Leaving factory credentials in place on network devices, including the s2 network node, creates a broad, easily exploited attack surface. Adversaries routinely scan for devices with known defaults and exploit weak or unchanged credentials to gain administrative access. Once access is established, they can pivot to other devices, disrupt services, exfiltrate data, or plant backdoors. According to Default Password Analysis, 2026, many organizations underestimate how quickly misconfigurations become active threats. Treat the s2 node as part of your credential surface and assume there is a real chance a default password is known by an intruder. The most effective defense is to eliminate default passwords entirely, replace them with unique, strong credentials, and implement continuous monitoring for credential drift. For teams, this means integrating password hygiene into onboarding, asset inventory, and change-management workflows.
Related concepts: credential hygiene, least privilege, network segmentation.
How to locate the s2 network node default password and verify its status
To locate the default password, start with the device label and user manual that came with the s2 node. Check the web-based management interface or CLI for a credential page or initial setup prompt. If documentation isn’t available, inspect the device’s sticker on the back or bottom for factory defaults (e.g., username/password patterns). Inventory tools and network scanners can help identify devices still using default credentials. In all cases, verify whether the default password is active by attempting a login with known factory credentials in a controlled environment. If access is blocked by firmware, consider safe reset procedures outlined in the device documentation. The key is to confirm the exact credential state before attempting changes. Note: Do not attempt broad credential resets during business hours on production networks without a rollback plan.
Step-by-step: Resetting the default password safely
- Back up current configurations and document the baseline setup. 2) Access the s2 node via its admin interface or physical reset, following vendor instructions. 3) Change the administrator password to a unique, high-entropy credential (prefer passphrases). 4) Enforce strong password policies and enable two-factor authentication if available. 5) Update access controls and limit management to trusted subnets. 6) Reboot and verify connectivity to all dependent services. 7) Maintain an inventory entry for the new credentials and rotate them per your policy. If the device is unreachable, use a supported safe-reset procedure or reach out to vendor support. 8) Test again by attempting authentication from a secure management workstation.
Best practices for password hygiene on network nodes
- Use unique, strong admin passwords per device (12+ characters, mixed case, symbols).
- Prefer passphrases and password managers for storage and retrieval.
- Enable MFA when the device supports it, and disable remote admin unless it’s strictly required.
- Restrict management access to a defined management network or VPN.
- Document credentials in a centralized, audited vault and rotate regularly.
- Schedule periodic credential reviews and inventory reconciliation to catch drift early.
Why automation and policy matter for admin credentials
Manual password management on dozens or hundreds of devices increases the likelihood of drift and misconfigurations. A policy-driven approach paired with automation improves consistency and reduces risk. Centralized credential management, automated inventory, and periodic security scans help detect devices still using default credentials. Use configuration management tooling to enforce password changes on first boot or during maintenance windows, and integrate alerting if any device reverts to default settings. The combination of automation and policy is essential for scalable security in modern networks.
Common pitfalls and quick-win fixes
- Pitfall: Assuming a single password fits all devices. Fix: Create device-specific credentials and enforce per-device uniqueness.
- Pitfall: Neglecting inventory updates. Fix: Maintain an up-to-date asset registry and automatic discovery.
- Pitfall: Skipping backup before changes. Fix: Always back up configs and have a documented rollback plan.
- Pitfall: Overlooking remote management risks. Fix: Restrict remote access to trusted networks and disable unused management interfaces.
- Quick-win: Run a quarterly credential health check and enforce minimum password strength thresholds across devices.
Status and actions for s2 network node default password
| Aspect | Current Guidance | Recommended Action |
|---|---|---|
| Default Password State | Widely used, risky if not changed | Change immediately and enforce unique credentials |
| Reset Process | Varies by device interface | Use official UI or reset button; save config before reset |
| Remote Access Risk | Unsecured defaults enable remote compromise | Disable default credentials; enable MFA where possible |
Your Questions Answered
What is meant by the s2 network node default password?
The default password is the factory-set credential used for initial setup on the s2 network node. Leaving it unchanged increases the risk of unauthorized access. Always replace it with a unique, strong password as part of your onboarding and security hardening.
The s2 network node default password is the factory credential used during setup. It should be changed immediately to a unique, strong password to reduce risk.
Where can I find the default password for the s2 network node?
Look at the device label, the user manual, or the initial setup guide that came with the s2 node. If documentation is missing, check the web interface under administration or contact support for factory default credentials. Always verify the current state before attempting changes.
Check the device label or the initial setup guide for the default password, or contact support if documentation isn’t available.
How do I reset the s2 network node default password if I can’t access the UI?
If the UI isn’t accessible, perform a safe reset according to the manufacturer’s procedure (often a hardware button or a service reset). After reset, reconfigure from scratch with a new password and document the steps. If you’re unsure, consult vendor support before proceeding.
If the UI is inaccessible, use the device’s reset procedure and set a new password after reconfiguration.
Will changing the password affect connected services or devices?
Changing the admin password may disrupt management sessions. Plan a maintenance window, update credentials in any scripts or automation that connect to the device, and test connectivity after the change. Maintain backup configurations to restore earlier states if needed.
Expect a short disruption during credential updates; update any automation and test connectivity afterward.
Is it safe to reuse the same password on multiple devices?
Reuse increases risk. Use unique, per-device credentials and store them in a password manager. This limits the blast radius if a single credential is compromised and simplifies rotation.
No—use unique passwords for each device and store them securely.
How often should I rotate admin passwords on network nodes?
Rotate admin passwords on a regular cadence aligned with your security policy, commonly every 90 days or after any suspected credential exposure. Pair rotation with monitoring to detect drift.
Rotate passwords regularly per policy, typically every 90 days or after a suspected exposure.
“Default Password Team emphasizes that default passwords on network nodes like the s2 device are a leading breach vector; hardening credentials should be a foundational security control.”
Key Takeaways
- Identify devices using the s2 network node default password
- Change to a unique, strong admin password immediately
- Document reset procedures and audit device credentials
- Apply automated credential management and MFA where available
- Regularly review and rotate admin passwords